OSINT Investigation: Dissecting a Live TNG eWallet QR Phishing Campaign — From Victim to Full Infrastructure Exposure
by Abbhilash Simanchalam
Category: OSINT / Incident Response / Threat Intelligence
Date: 27th March 2026
Author: Abbhilash Simanchalam
Severity: 🔴 HIGH — Active Campaign, Live Infrastructure
⚠️ Disclaimer
This investigation was conducted using passive OSINT and legal reconnaissance only. No unauthorized access was performed. All findings were obtained from publicly accessible URLs and open-source tools. The phishing infrastructure described here was reported to CyberSecurity Malaysia, MCMC, Cloudflare, Google Safe Browsing, and VirusTotal as part of responsible disclosure. IoCs have been published to aid defenders.
1. Background & How It Started
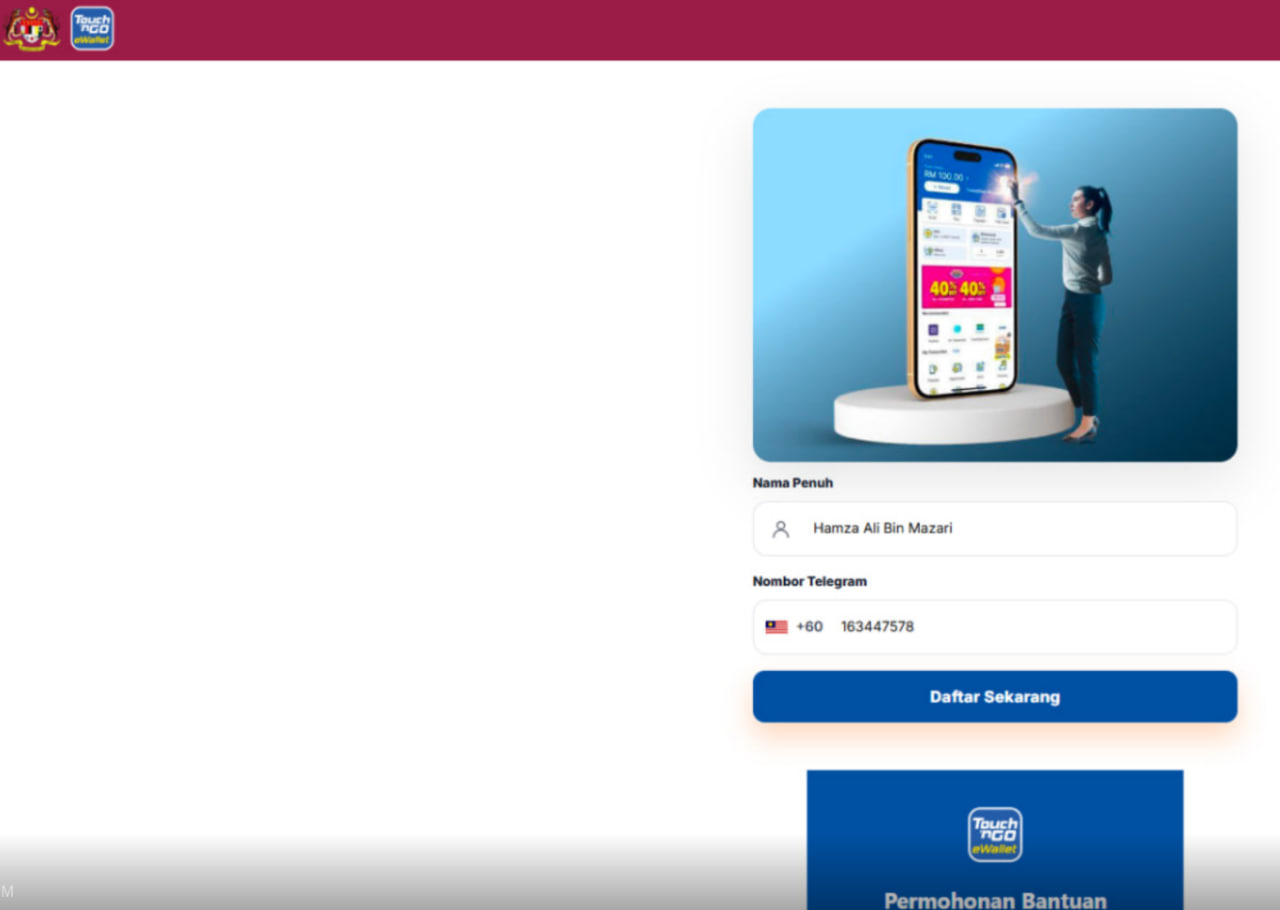
Figure 1: The phishing page disguised as a Touch ‘n Go eWallet Money Packet
On 26th March 2026 at approximately 6:04 PM MYT, I scanned a QR code that appeared to be a legitimate Touch ‘n Go eWallet “Money Packet” out of curiosity. The QR was scanned inside the TNG app itself, which opened an in-app WebView browser.
The page looked convincing. I entered my full name and phone number, believing it was a standard eWallet redemption flow. The page then asked for a “verification code.” Seconds after entering it, my Telegram received the following notification:

Figure 2: Telegram login notification — Telegraph/12.3.1.1, Oppo A60, Malaysia, 10:08:50 UTC
New login. Dear ***, we detected a login into your account
from a new device on 26/03/2026 at 10:08:50 UTC.
Device: Telegraph, 12.3.1.1, Oppo A60, Android 15 (35)
Location: Malaysia
I had just been phished!, The “verification code” mentioned on the page was actually a trick and unintentionally I entered my Telegram OTP (Telegram shares verification codes and OTP’s in the same channel) — and the attacker used it to log into my account within seconds. My account was then used to forward the same phishing QR to my Telegram groups, propagating the attack to new victims.
Response actions taken (within ~2 minutes):
- Terminated all active Telegram sessions
- Enabled Telegram Two-Step Verification (2FA password)
- Confirmed no unknown sessions remained
- Full account control regained
What follows is the full OSINT investigation I conducted to trace the attacker’s infrastructure.
2. Attack Chain Reconstruction
[Victim] Scans QR Code
│
▼
[TNG In-App Browser / WebView]
URL: https://tngmoney.cc/qr.html?l=MxRJdCJ9u9T...
│
▼
[Phishing Page — TNG Lookalike]
Harvests: Full Name + Phone Number
│
▼
[Attacker Backend triggers Telegram auth.sendCode()]
Telegram sends OTP to victim's device
│
▼
[Phishing Page requests "Verification Code"]
Victim enters OTP
│
▼
[Attacker calls auth.signIn() with stolen OTP]
→ If no 2FA: Full account access
→ If 2FA enabled: Page shows password form (Step 3)
│
▼
[Attacker gains Telegram session]
Weaponises account to blast phishing QR to groups
Attack classification: AiTM (Adversary-in-The-Middle) + OTP Relay + Telegram Session Hijack
Total attacker dwell time: ~2 minutes (limited by fast incident response)
3. Methodology & Tools Used
All reconnaissance was passive — no exploitation or active attacks were performed.
- Source Code Analysis — Reviewed phishing page HTML/JS to extract backend structure
- OSINT Recon —
crt.sh,VirusTotal,DNSChecker,WhoIS,nslookup,dig - Header Analysis —
curl -Ito extract Cloudflare metadata - Directory Fuzzing —
ffufwithdirb/common.txtto map server structure - SSL Analysis —
openssl s_clientto extract certificate timestamps - Favicon Hashing — Python
mmh3for Shodan favicon search - Wireshark — DNS capture to confirm live resolution
- Legal OSINT — Phishing kit source review and
.envkey extraction
4. Phishing Infrastructure Analysis
4.1 — Domain Intelligence
The QR redirected to an initial domain, but the actual kit was hosted at:
| Attribute | Value |
|---|---|
| Initial redirect | tngmoney.cc |
| Phishing kit host | https://bantuan.tng-my.online/kd1/ |
| Second campaign | https://bantuan.tng-my.online/2/semak/ |
| Registrar | Privacy-protected |
| Domain created | 2026-03-25 — 24 hours before the attack |
| TLD | .online — ~$1/year, high-abuse TLD |
| Subdomain | bantuan. (“assistance” in Malay) — deliberate social engineering |
The ?l=MxRJdCJ9u9T... parameter in the initial QR URL is a per-victim tracking token — linking each scan to a specific OTP relay session on the backend.
4.2 — Certificate Transparency (crt.sh)
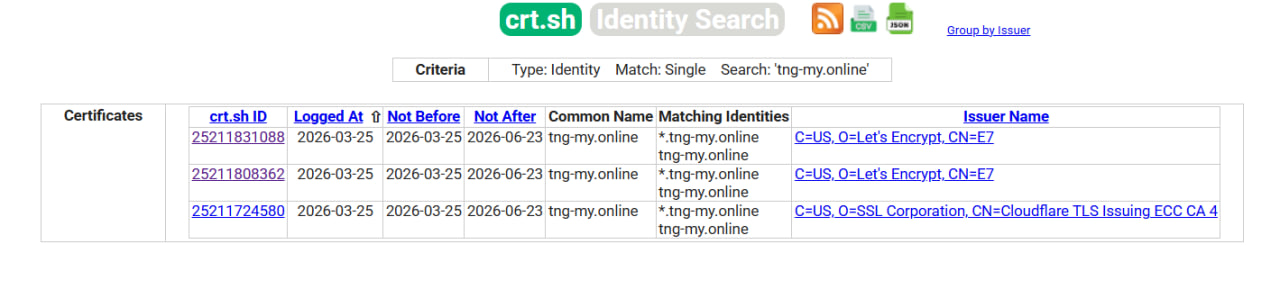
Figure 3: crt.sh showing 3 certificates issued for tng-my.online on 2026-03-25 — wildcard cert confirmed
Search: %.tng-my.online
Results:
ID: 25211831088 | Logged: 2026-03-25 | *.tng-my.online (Let's Encrypt)
ID: 25211808362 | Logged: 2026-03-25 | *.tng-my.online (Let's Encrypt)
ID: 25211724580 | Logged: 2026-03-25 | *.tng-my.online (Cloudflare TLS)
Key findings:
- All 3 certificates issued on the same day the attack infrastructure launched
- Wildcard certificate (
*.tng-my.online) — attacker can spin up unlimited subdomains instantly without reissuing certs - Only one subdomain discovered (
bantuan) — either early-stage or other campaigns use different domains
4.3 — DNS Resolution
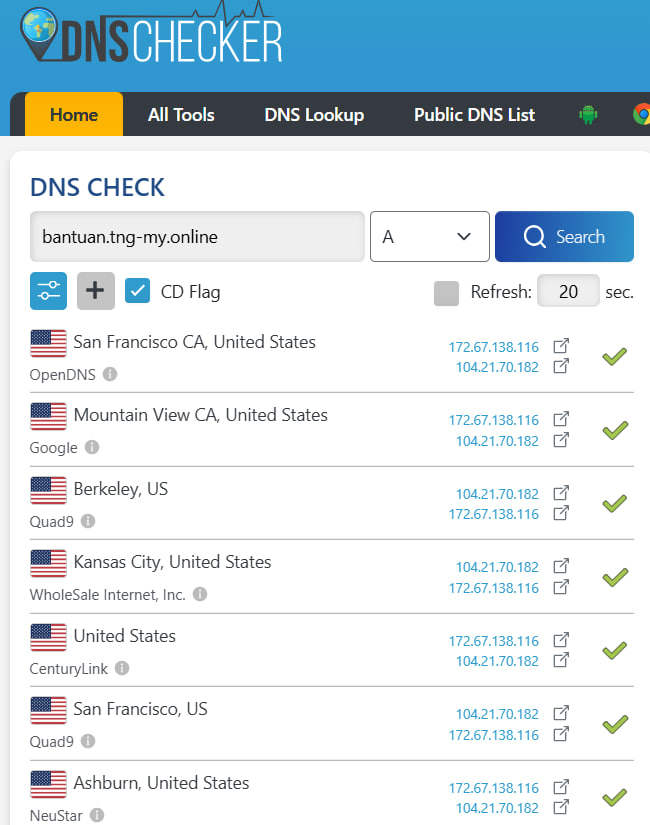
Figure 4: DNS resolution confirming bantuan.tng-my.online resolves to Cloudflare IPs globally
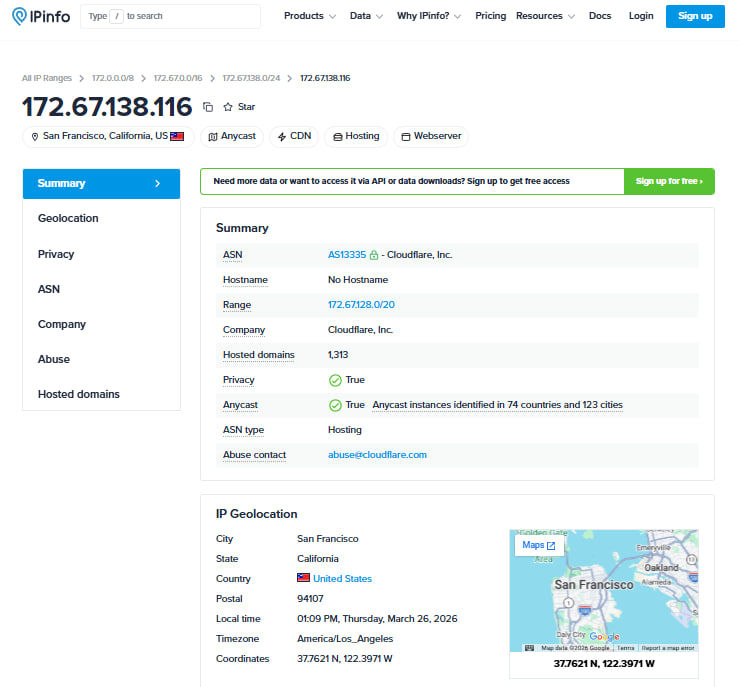
Figure 5: IP Geolocation of Cloudflare Proxy
bantuan.tng-my.online resolves to:
172.67.138.116 ← Cloudflare proxy
104.21.70.182 ← Cloudflare proxy
IPv6:
2606:4700:3033::ac43:8a74
2606:4700:3037::6815:46b6
The real origin server IP is hidden behind Cloudflare. All traffic is proxied — standard operational security for phishing actors.
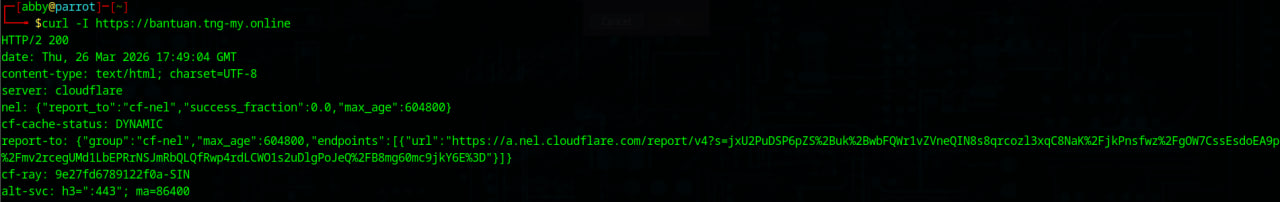
Figure 6: curl -I response — server: cloudflare, CF-Ray: 9e27fd6789122f0a-SIN (Singapore edge)
Cloudflare Ray ID captured via curl: 9e27fd6789122f0a-SIN
(SIN = Singapore edge node — CF routes MY traffic through Singapore)
4.4 — SSL Certificate Analysis
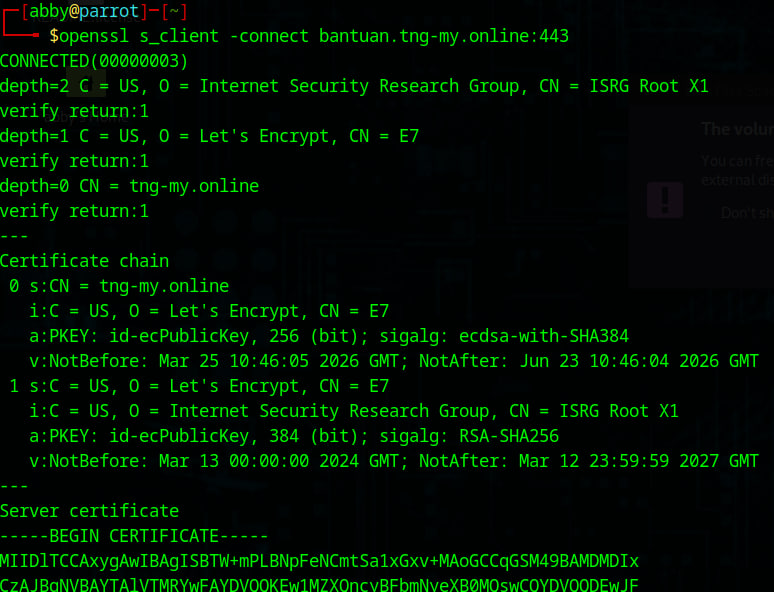
Figure 7: openssl s_client — Let’s Encrypt cert issued 2026-03-25 10:46:05 UTC, CN=tng-my.online
$ openssl s_client -connect bantuan.tng-my.online:443
CN = tng-my.online
Issuer: Let's Encrypt CN=E7
NotBefore: Mar 25 10:46:05 2026 GMT
NotAfter: Jun 23 10:46:04 2026 GMT
Certificate issued at 10:46 UTC on March 25 — infrastructure was fully live ~24 hours before it was used against me.
4.5 — WHOIS Registration Data (ICANN RDAP)
A lookup via lookup.icann.org revealed the domain registrant details were not privacy-protected — exposing potential attacker identity information.
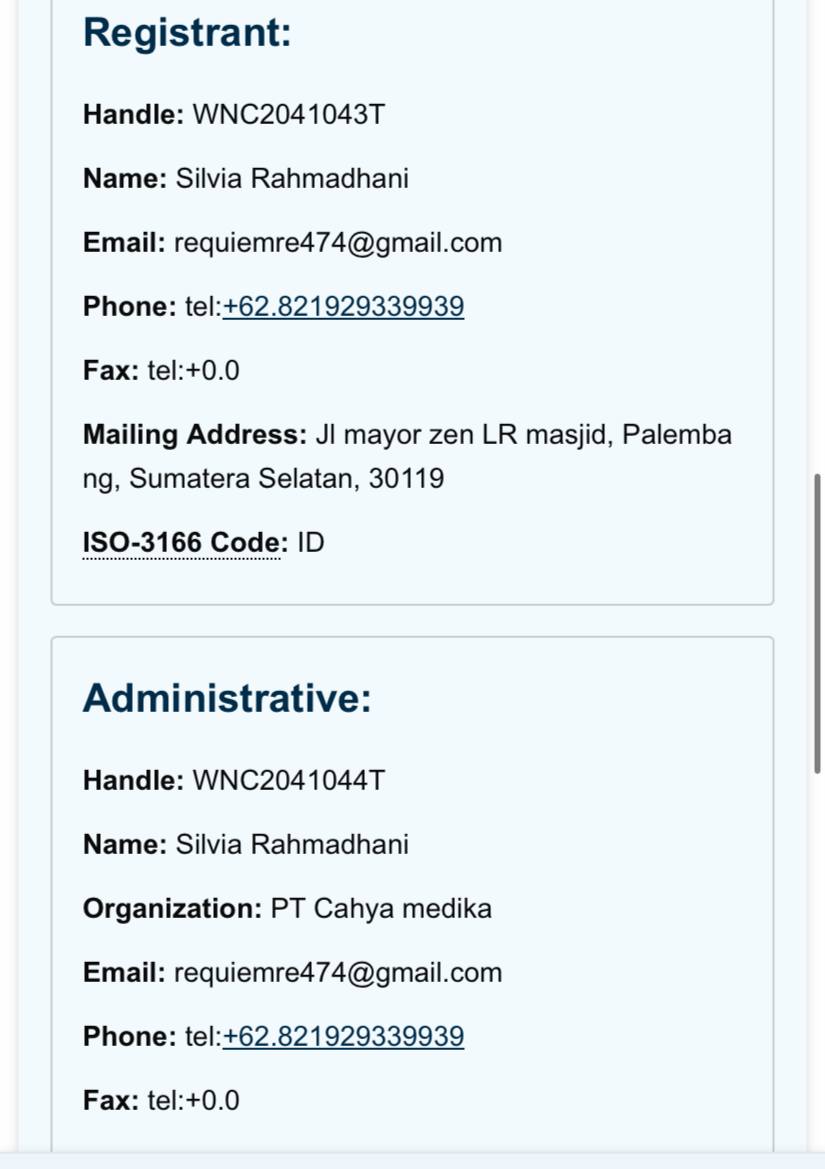
Figure 8: ICANN RDAP — tng-my.online domain information, updated 2026-03-26 12:00:06 UTC
| Field | Value |
|---|---|
| Registrant Name | Silvia Rahmadhani |
| requiemre474@gmail.com | |
| Phone | +62.821929339939 |
| Address | Jl mayor zen LR masjid, Palembang, Sumatera Selatan, 30119 |
| Country | Indonesia (ID) |
| Organization | PT Cahya medika |
| Registrar | WebNIC (IANA ID: 460) |
| Registrar Abuse | compliance_abuse@webnic.cc |
| Domain Updated | 2026-03-26 12:00:06 UTC |
| Domain Expires | 2027-03-25 |
⚠️ Investigator’s Note: The registrant name and address may be fictitious or represent a stolen identity — a common tactic in fraud operations. However, the phone number
+62.821929339939and emailrequiemre474@gmail.comare actionable intelligence leads regardless of name authenticity. The+62country code independently corroborates Indonesia as the origin. The domain was updated on the same day as the attack (2026-03-26), suggesting the attacker may have modified settings after becoming aware of investigation activity.
5. Phishing Kit Source Code Analysis
Accessing the phishing page source revealed a complete, professional kit. Key findings:
5.1 — setting.php: Backend Configuration
{
"apiBase": "",
"requestCodePath": "gateway.php?path=/generate-session",
"verifyCodePath": "gateway.php?path=/validate-otp",
"verifyPasswordPath": "gateway.php?path=/validate-password",
"notifyEndpoint": "",
"defaultCountry": "ID"
}
apiBase being empty means the C2 backend is on the same server as the phishing page. The gateway.php file is the core credential relay engine.
The three endpoints map directly to Telegram’s API:
| Endpoint | Telegram API Call | Purpose |
|---|---|---|
/generate-session |
auth.sendCode() |
Triggers OTP to victim’s device |
/validate-otp |
auth.signIn() |
Submits stolen OTP to Telegram |
/validate-password |
auth.checkPassword() |
Submits stolen 2FA password |
The kit is specifically designed to handle both OTP-only and 2FA-protected accounts — the password step only appears if the victim has 2FA enabled.
5.2 — Origin Fingerprinting
Multiple indicators confirm the kit’s origin:
| Indicator | Value | Interpretation |
|---|---|---|
lang="id" |
Indonesian HTML lang attribute | Kit written by Indonesian developer |
| JS comments | // user cukup isi angka |
Indonesian language throughout |
defaultCountry |
ID (Indonesia) |
Original default target country |
| Notification text | ₼3.399 AZN (Azerbaijani Manat) |
Previous campaign artifact — template remnant |
PRAKERJA 2026 |
Indonesian government welfare program | Repurposed from Indonesian campaign |
| UI text | Malay (Nama Penuh, Sahkan) |
Reconfigured surface layer for Malaysia |
Assessment: This kit was originally built for Indonesia, previously deployed against Azerbaijan, and reconfigured for Malaysia. Classic multi-country phishing-as-a-service operation.
5.3 — Cloudflare Analytics Beacon
data-cf-beacon='{"token":"af50a1a45fb94f7a9a3a8cab4c6f08e7"}' - \\this is observed in generate-session code
The attacker embedded Cloudflare Web Analytics to track victim counts per campaign. This token is a cross-campaign fingerprint — if reused on other phishing pages, it links them to the same operator. Reported to Cloudflare Abuse.
6. Server Enumeration (ffuf Directory Fuzzing)
$ ffuf -u https://bantuan.tng-my.online/FUZZ -w /usr/share/wordlists/dirb/common.txt
.htpasswd [Status: 403] ← Apache password file protected
.htaccess [Status: 403] ← Access control configured
/1 [Status: 301] ← ⚠️ Campaign slot 1 (redirect)
/2 [Status: 301] ← ⚠️ Campaign slot 2 (redirect)
/ap [Status: 301] ← Additional campaign slot
/app [Status: 301] ← Additional campaign slot
/cgi-sys [Status: 301] ← Confirms cPanel shared hosting
/controlpanel [Status: 200, 35KB] ← ⚠️ Admin panel accessible
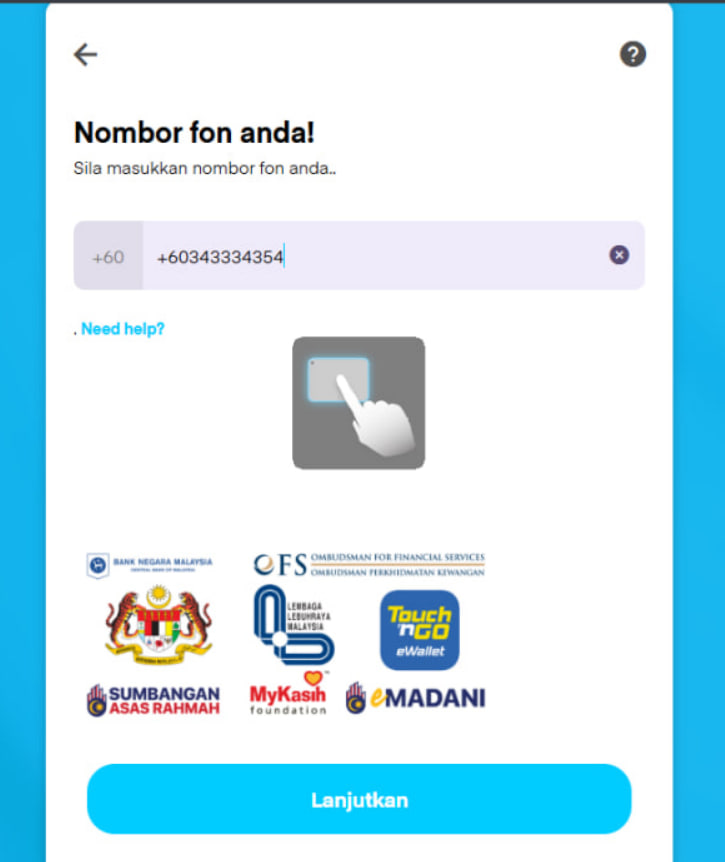
Figure 9: Live phishing page at bantuan.tng-my.online/2/semak/ impersonating 6 Malaysian institutions
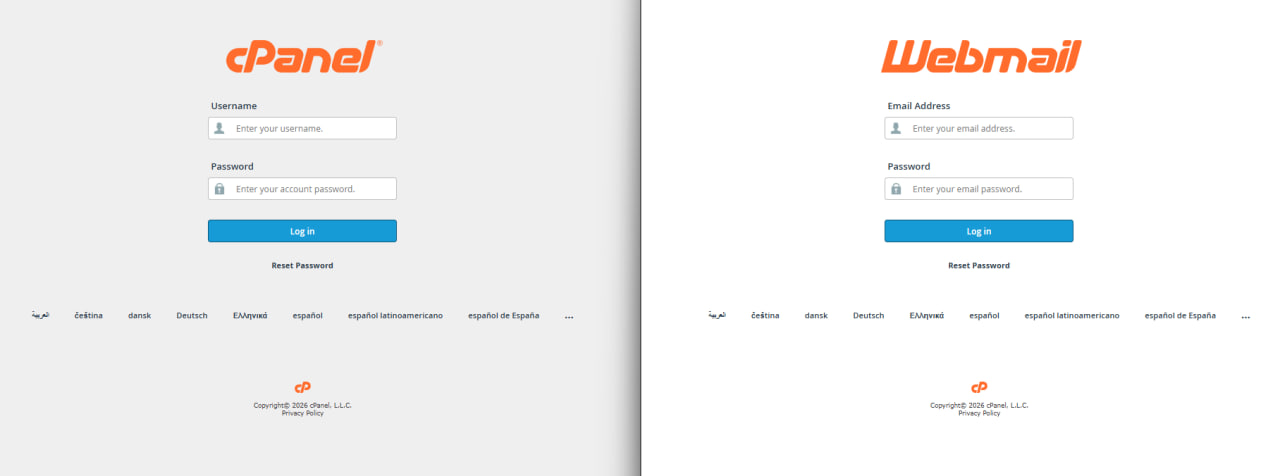
Figure 10: cPanel & Webmail login panel exposed on port 2083 and 2096 — confirms shared hosting infrastructure and registration details
Critical finding: /1 and /2 both redirect, confirming multiple parallel campaigns. Visiting /2/semak/ revealed a second active phishing page — a different UI (“eligibility checker” variant) impersonating 6 Malaysian institutions simultaneously: Bank Negara Malaysia, Jabatan Kebajikan Masyarakat, Lembaga Lebuhraya Malaysia, Touch ‘n Go eWallet, MyKasih Foundation, and eMadani.
7. The C2 Panel — Truelogin V5
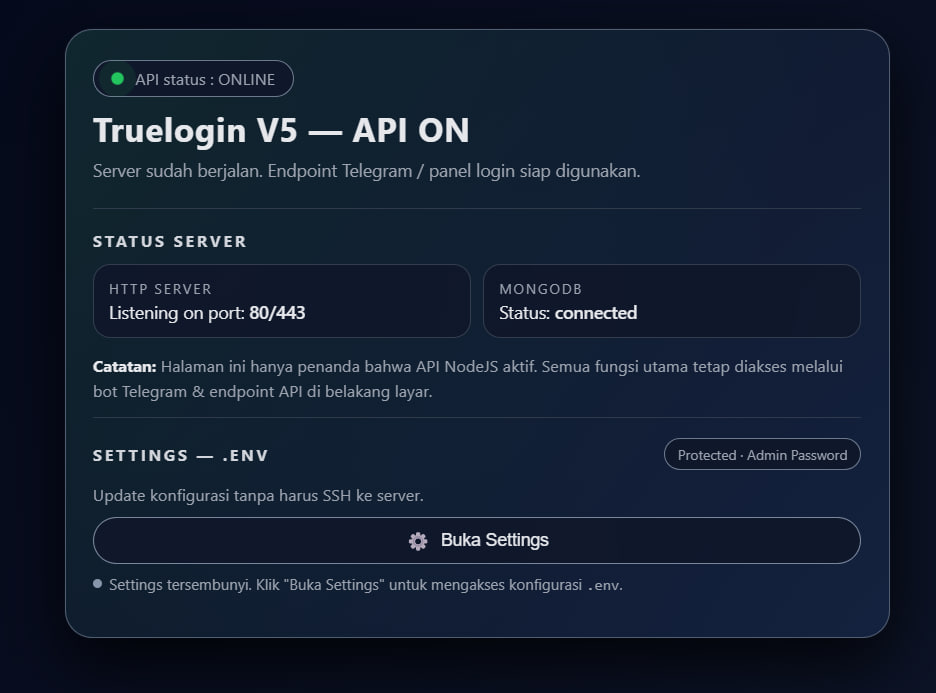
Figure 11: Truelogin V5 API panel — NodeJS + MongoDB live, Indonesian-origin Telegram phishing kit
The most significant discovery came from the generate-session endpoint source, which revealed the attacker’s backend identity:
Truelogin V5 — API ON
Server sudah berjalan. Endpoint Telegram / panel login siap digunakan.
STATUS SERVER
HTTP SERVER: Listening on port 80/443
MONGODB: Status: connected
Truelogin V5 is a named, commercially distributed Indonesian Telegram phishing-as-a-service kit. This finding confirms:
- The kit has a developer/seller separate from the person who deployed it
- A live MongoDB database is connected — storing every victim’s phone number, OTP, and 2FA password ever submitted
- The backend exposes a
.envconfiguration panel with password protection, containing these keys:
BOT_TOKEN ← Attacker's Telegram bot for receiving stolen credentials
USER_ID ← Attacker's Telegram user ID (receives all notifications)
API_ID ← Telegram API credentials for GramJS
API_HASH ← Telegram API credentials for GramJS
DATABASE_URL ← MongoDB connection string
COLLECTION ← Database collection name
SOCKS5 ← Proxy configuration
The SOCKS5 field confirms the attacker routes Telegram API calls through a proxy — deliberate anti-attribution measure.
8. Complete Infrastructure Map
┌─────────────────────────────────────────────────────────────┐
│ ATTACK INFRASTRUCTURE │
├─────────────────────────────────────────────────────────────┤
│ │
│ LAYER 1 — CDN/Proxy (Cloudflare) │
│ 172.67.138.116 / 104.21.70.182 (Anycast proxies) │
│ CF Ray: 9e27fd6789122f0a-SIN (Singapore edge) │
│ │
│ LAYER 2 — Web Hosting (cPanel) │
│ bantuan.tng-my.online:2083 (cPanel login) │
│ bantuan.tng-my.online:2096 (Webmail) │
│ Campaigns: /kd1/ | /1/ | /2/semak/ | /ap/ | /app/ │
│ │
│ LAYER 3 — C2 Backend (Truelogin V5) │
│ Engine: NodeJS │
│ Database: MongoDB (live, connected) │
│ Config: .env via password-protected admin panel │
│ Relay: gateway.php → Telegram API via SOCKS5 │
│ │
│ LAYER 4 — Attacker │
│ Client: Telegraph/12.3.1.1 (modified Telegram) │
│ Device: Oppo A60, Android 15 (API 35) │
│ Reported location: Malaysia (likely VPN) │
│ Login time: 2026-03-26T10:08:50Z │
│ Kit origin: Indonesia │
└─────────────────────────────────────────────────────────────┘
9. Timeline of Events
| Time (MYT) | Event |
|---|---|
| 6:04 PM, 26 Mar | Victim scans phishing QR code |
| 6:05–6:07 PM | Name + phone number submitted to phishing page |
| 6:08 PM | Telegram OTP received on victim device |
| 6:08 PM | Victim enters OTP on phishing page |
| 6:08:50 PM | Attacker logs into Telegram (Telegraph/12.3.1.1, Oppo A60, Malaysia) |
| 6:08–6:10 PM | Attacker sends phishing QR to victim’s Telegram groups |
| 6:10 PM | Victim notices notification, terminates all sessions |
| 6:10 PM | 2FA enabled — attacker permanently locked out |
| 27 Mar, ongoing | OSINT investigation conducted |
| 27 Mar | Full infrastructure mapped, reports filed |
Attacker dwell time: ~2 minutes
10. Threat Actor Assessment
THREAT ACTOR PROFILE
━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━
Origin: Indonesia (high confidence)
Operation type: Phishing-as-a-Service (kit-based)
Kit: Truelogin V5 (NodeJS + MongoDB)
Prior targets: Indonesia, Azerbaijan, Malaysia (confirmed)
Scale: Multi-campaign (/kd1/, /1/, /2/, /ap/, /app/)
Sophistication: Medium-High (handles 2FA, SOCKS5 proxy, dynamic config)
Infrastructure: cPanel shared hosting + Cloudflare proxy
Domain age: 24 hours before first observed attack
Wildcard cert: Yes — unlimited subdomain capability
━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━
The Telegraph client (not standard “Telegram”) is a modified open-source client commonly used in fraud toolkits for programmatic account control and bulk messaging — consistent with the group-propagation behaviour observed.
11. Complete IoC List
DOMAINS
tng-my.online
bantuan.tng-my.online
tngmoney.cc
URLS (Phishing)
https://bantuan.tng-my.online/kd1/
https://bantuan.tng-my.online/2/semak/
https://tngmoney.cc/qr.html?l=MxRJdCJ9u9T...
URLS (Infrastructure)
https://bantuan.tng-my.online/kd1/gateway.php
https://bantuan.tng-my.online/kd1/setting.php
https://bantuan.tng-my.online:2083 (cPanel)
https://bantuan.tng-my.online:2096 (Webmail)
IPs (Cloudflare proxies — origin IP hidden)
172.67.138.116
104.21.70.182
2606:4700:3033::ac43:8a74
2606:4700:3037::6815:46b6
CLOUDFLARE IDENTIFIERS
Ray ID: 9e27fd6789122f0a-SIN
Analytics token: af50a1a45fb94f7a9a3a8cab4c6f08e7
SSL CERTIFICATE
Issued: 2026-03-25T10:46:05Z
Issuer: Let's Encrypt E7
CN: tng-my.online (wildcard)
PHISHING KIT
Name: Truelogin V5
Language: Indonesian (NodeJS + MongoDB)
Backend: gateway.php → Telegram GramJS API
ATTACKER DEVICE (from Telegram login log)
Client: Telegraph/12.3.1.1
Device: Oppo A60, Android 15 (API 35)
Location: Malaysia
Timestamp: 2026-03-26T10:08:50Z
12. Reports Filed
| Authority | Contact | Status |
|---|---|---|
| CyberSecurity Malaysia | cyber999@cybersecurity.my | ✅ Filed |
| MCMC | aduan.skmm.gov.my | ✅ Filed |
| Cloudflare Abuse | cloudflare.com/abuse | ✅ Filed (with CF Ray ID) |
| Google Safe Browsing | safebrowsing.google.com | ✅ Filed |
| VirusTotal | virustotal.com | ✅ Submitted both URLs |
| PhishTank | phishtank.org | ✅ Submitted |
13. Key Takeaways for Defenders
- Telegram OTP is NOT a one-time safe code — any page asking for it outside the Telegram app itself is phishing, regardless of context
- QR codes inside trusted apps can still redirect to phishing sites — the TNG app’s WebView does not validate destination URLs
- Enable Telegram 2-Step Verification now — it adds a password layer the OTP relay cannot bypass without a second form of interaction
- Wildcard certs + cheap TLDs + Cloudflare is the modern phishing infrastructure trifecta — fast, cheap, hard to take down quickly
- Truelogin V5 (and similar Indonesian-origin kits) are actively targeting Malaysian eWallet users — share these IoCs with your SOC
- The
?l=tracking parameter in phishing QR URLs is a victim-specific token — if you see this pattern, treat the URL as hostile
14. Ethical Boundaries & Legal Compliance
This investigation was conducted with strict adherence to ethical standards:
- No unauthorised access — all findings from publicly accessible URLs and standard OSINT tooling
- No credential submission — test phone numbers used when probing
/2/semak/were not real numbers - Responsible disclosure — all findings reported to relevant authorities before publication
- PDPA compliance — no victim personal data published; all IoCs are infrastructure-level
The phishing kit source code analysis was performed on files that were publicly accessible without authentication on the attacker’s own server.
This report was produced as part of active incident response following a personal phishing compromise on 26th March 2026. All investigation was completed within 24 hours of the initial incident.
tags: phishing - telegram - qr-code - malaysia - truelogin - otp-hijack - osint