SOC137 – Malicious File/Script Download Attempt (Macro-Based DOCM Blocked)
by
🧠 Summary
This investigation was triggered by a SOC137 – Malicious File/Script Download Attempt alert involving a suspicious Microsoft Word macro-enabled document named:
INVOICE PACKAGE LINK TO DOWNLOAD.docm
Initial threat intelligence analysis using VirusTotal showed a high detection rate (38/66), indicating strong evidence of malicious activity.
Further analysis using Hybrid Analysis sandbox confirmed that the document contains malicious VBA macros, specifically an AutoOpen function designed to execute automatically when the file is opened.
The macro leverages PowerShell commands to download additional payloads from a remote server, a common technique used in malware delivery.
However, endpoint telemetry confirmed that the file was blocked at the security control level, and no execution or follow-up activity was observed.
The alert was classified as a True Positive – Blocked (No Impact).
🚨 Alert Overview
- Event ID: 76
- Rule: SOC137 – Malicious File/Script Download Attempt
- Severity: Medium
- Source Host: NicolasPRD
- Source IP: 172.16.17.37
- File Name: INVOICE PACKAGE LINK TO DOWNLOAD.docm
- File Hash: f2d0c66b80124fc059f636d08a474079
- File Size: 16.66 KB
- Device Action: Blocked
🔍 Investigation Steps
1. VirusTotal Analysis
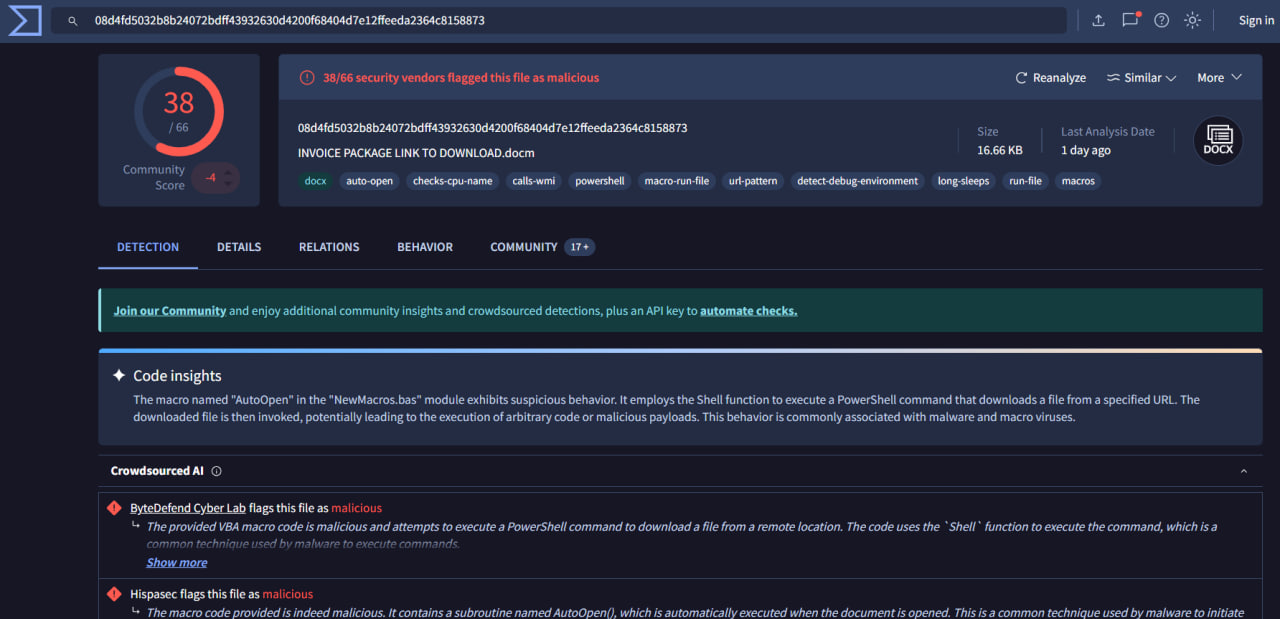
- Detection Rate: 38/66 (Malicious)
- Tagged behaviors:
macro-run-filepowershellauto-openlong-sleeps
💡 Insight:
The document contains a macro that automatically executes on open and uses PowerShell to download additional payloads — a strong indicator of malware delivery.
2. Code Behavior Insights
- Uses AutoOpen() macro
- Executes commands via Shell
- Downloads payload from external URL
⚠️ This is a classic malicious macro technique used in phishing campaigns.
3. Hybrid Analysis Sandbox
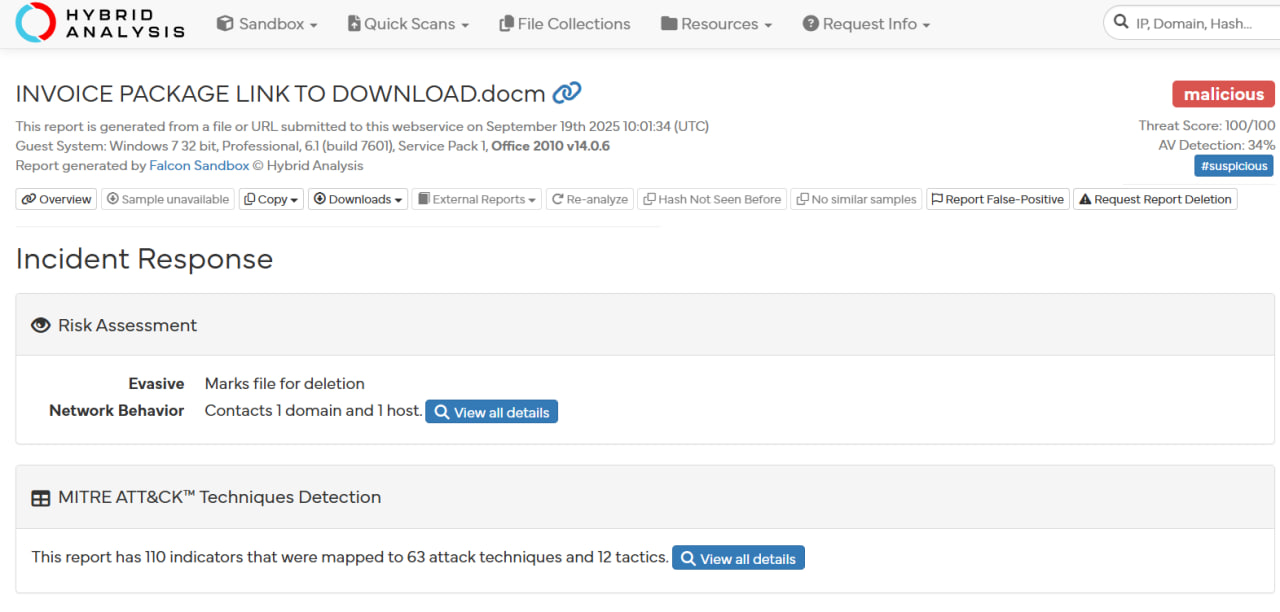
- Verdict: Malicious
- Threat Score: 100/100
- Observed behavior:
- Attempts external communication
- Payload download activity
- Anti-analysis / evasion techniques
4. Endpoint Investigation
All endpoint telemetry was reviewed:
| Artifact Checked | Result |
|---|---|
| Process Activity | No suspicious execution |
| Network Connections | No outbound C2 traffic |
| Command Line Activity | No PowerShell execution |
| Browser History | No related activity |
| File Execution | Not executed |
5. Security Control Validation
- Device Action: Blocked
- The file was prevented from execution before impact
✔ No signs of:
- Payload execution
- C2 communication
- Persistence
🧪 Indicators of Compromise (IOCs)
- File Hash: f2d0c66b80124fc059f636d08a474079
- File Name: INVOICE PACKAGE LINK TO DOWNLOAD.docm
🧬 MITRE ATT&CK Mapping
| Tactic | Technique |
|---|---|
| Initial Access | T1566.001 – Phishing Attachment |
| Execution | T1204.002 – User Execution |
| Execution | T1059.001 – PowerShell |
| Defense Evasion | T1497 – Sandbox Evasion |
| Command & Control | T1105 – Ingress Tool Transfer |
📊 Final Verdict
| Category | Result |
|---|---|
| Classification | True Positive |
| Impact | No Impact (Blocked) |
| Threat Level | Medium |
| Action Taken | Prevented by security control |
✅ Conclusion
This case represents a phishing-based malware delivery attempt using VBA macros.
The attack chain was successfully interrupted at the initial stage, demonstrating effective security controls.
The system remains uncompromised, and no further remediation is required.
tags: