SOC105 – Suspicious URL Request (Bitly Redirect – Benign Activity)
by
🧠 Summary
This investigation was triggered by a SOC105 – Requested T.I. URL Address alert involving a shortened URL (bit.ly/TAPSCAN).
Initial threat intelligence flagged the URL as suspicious; however, deeper analysis revealed that it redirected to a legitimate Google Play Store application (TapScanner).
Further validation using VirusTotal, AnyRun, and Hybrid Analysis showed no malicious behavior.
The activity was determined to be benign user activity, and the alert was classified as a False Positive.
🚨 Alert Overview
- Event ID: 75
- Rule: SOC105 – Requested T.I. URL Address
- Severity: High
- Source Host: MarksPhone
- Source IP: 10.15.15.12
- Destination IP: 67.199.248.10
- Destination Domain: bit.ly
- User: Mark
- Action: Allowed
🔍 Investigation Steps
1️⃣ URL Analysis
https://bit.ly/TAPSCAN
- VirusTotal:
- 1/95 detections
- Tagged as:
- Phishing (single vendor)
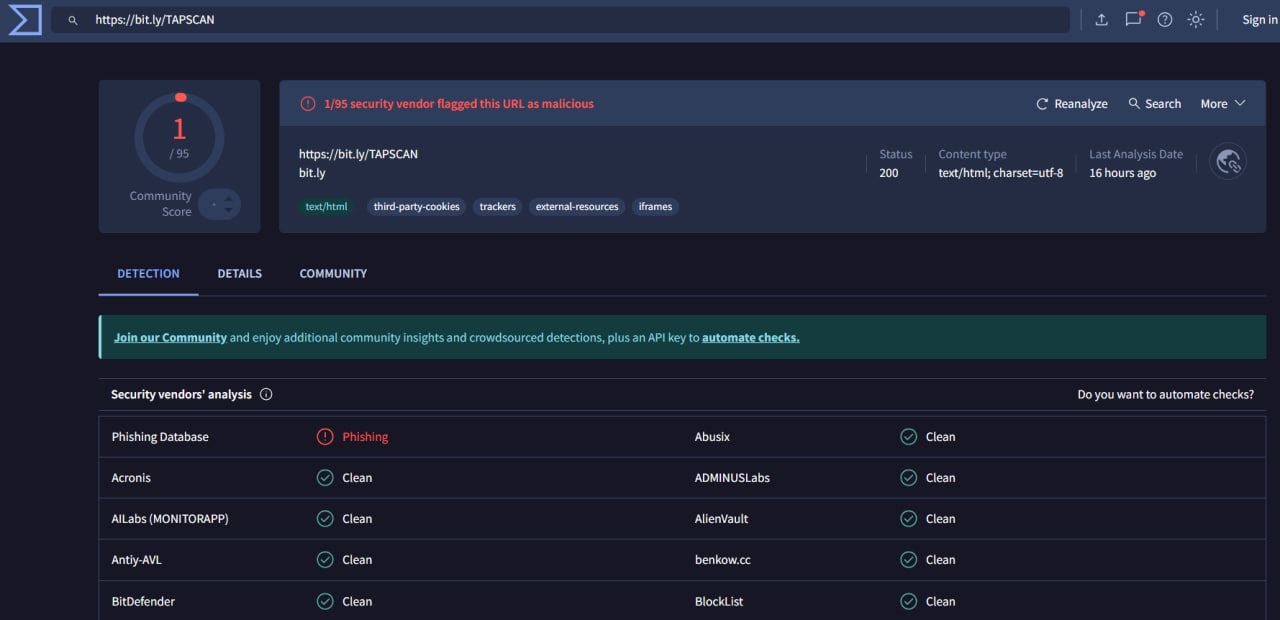
⚠️ Observation: Very low detection → requires deeper validation.
2️⃣ Sandbox Analysis (AnyRun)
- URL opened in sandbox environment
- Observed behavior:
- Redirected to Google Play Store
- No malicious scripts or payload execution
- No suspicious processes
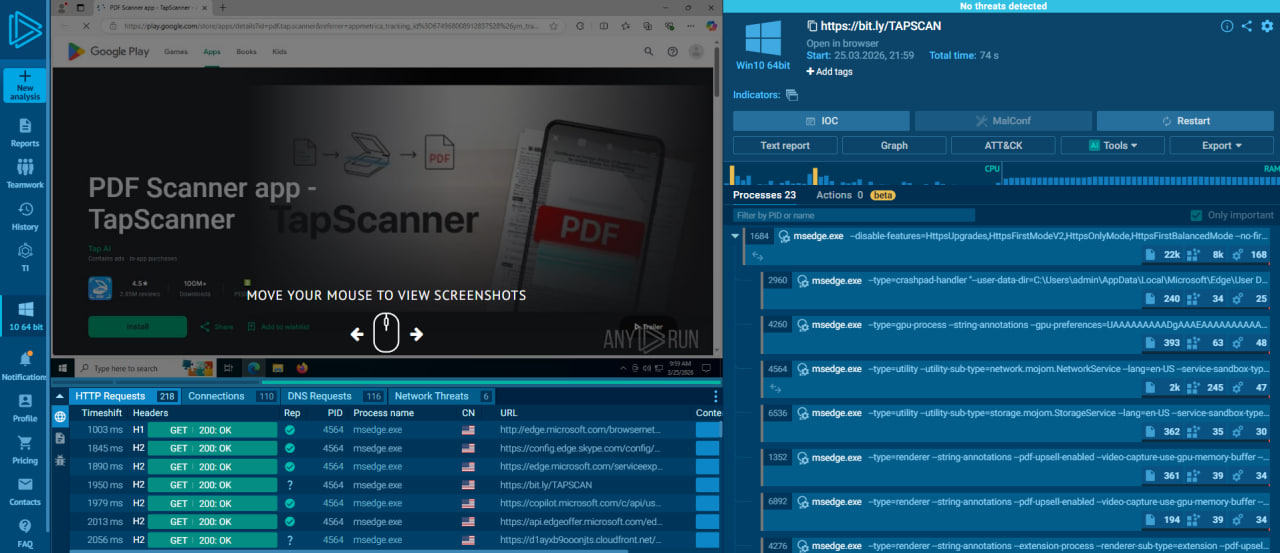
✅ Conclusion: No malicious behavior detected.
3️⃣ Hybrid Analysis
- Latest sandbox analysis (2024):
- No malicious indicators
- Clean behavior on Windows environment
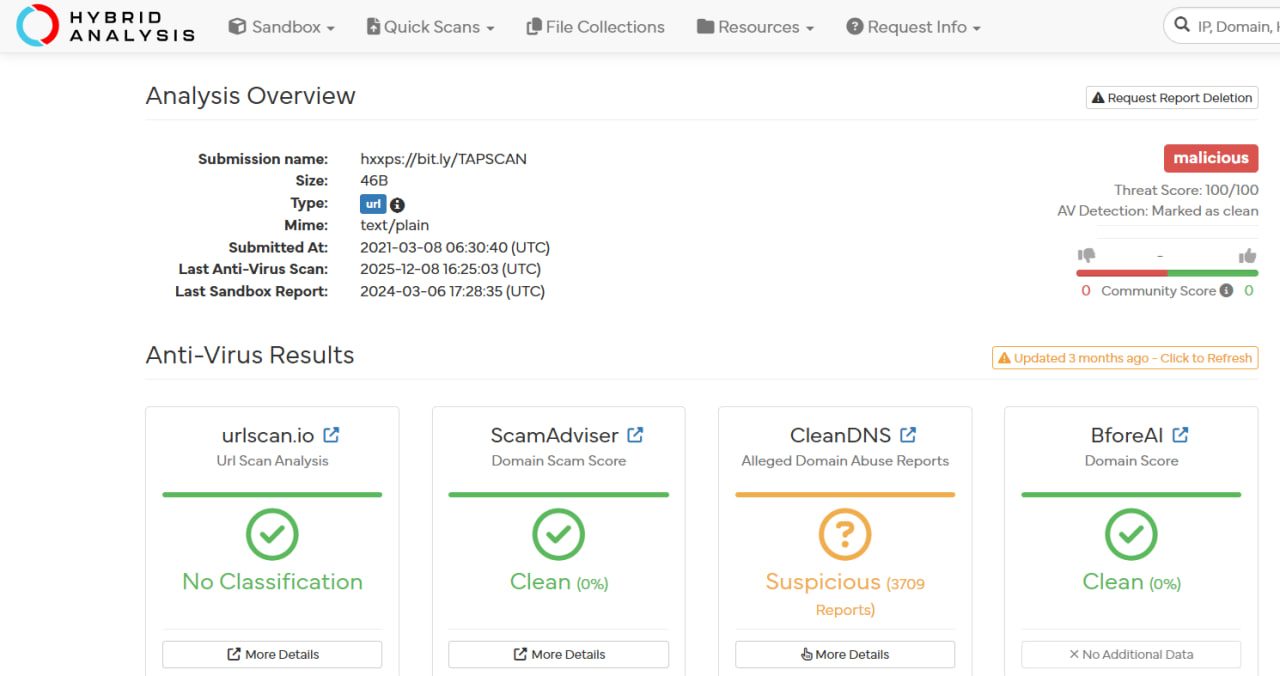
✅ Conclusion: No evidence of malicious activity.
4️⃣ IP Reputation Analysis
-
Destination IP:
67.199.248.10 - VirusTotal:
- 2/94 detections
- Ownership:
- Bitly Inc (URL shortening service)
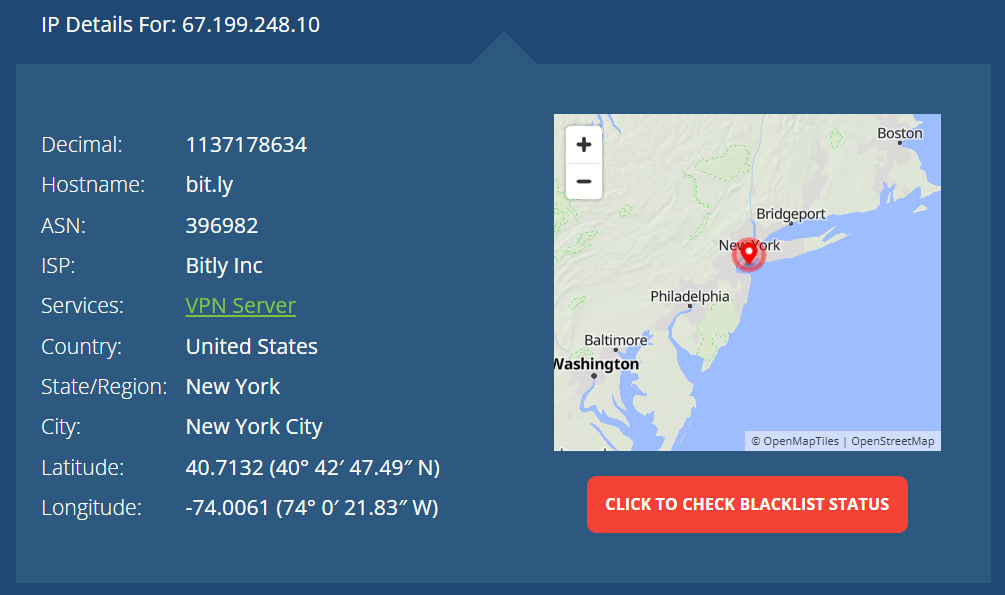
✅ Conclusion: Trusted infrastructure (Bitly service).
5️⃣ Traffic Behavior Analysis
- Process involved:
msedge.exe(browser)
- HTTP logs show:
- Normal web traffic
- Successful request (200 OK)
- No suspicious downloads or execution
✅ Conclusion: Standard user browsing activity.
⚠️ Final Verdict
| Category | Result |
|---|---|
| URL Reputation | Low Risk |
| Sandbox Result | Clean |
| IP Reputation | Trusted (Bitly) |
| Behavior | Redirect to Legitimate App |
| Impact | None |
| Severity | Low |
| Verdict | ❌ False Positive |
🛡️ Actions Taken
- 🔍 Investigated URL and redirection behavior
- 🧪 Performed sandbox analysis (AnyRun, Hybrid Analysis)
- 🌐 Verified IP reputation
- 📝 Classified alert as False Positive
📌 Conclusion
This alert represents a false positive triggered by a shortened URL.
The investigation confirmed:
Bitly URL → Redirect → Legitimate Google Play Page → No Threat
Despite initial suspicion, the activity was purely benign user interaction with a trusted service.
This case highlights the importance of:
- 🔍 Expanding shortened URLs before judgment
- 🧠 Validating behavior through sandbox analysis
- ⚠️ Avoiding reliance on single-engine detections
- 🌐 Understanding common services like Bitly
tags: