SOC105 – Suspicious URL Request (Firewall Test Activity)
by
🧠 Summary
This investigation was triggered by a SOC105 – Requested T.I. URL Address alert involving a request to an external IP address (115.99.150.132) hosting a suspicious resource.
Initial threat intelligence checks showed moderate detections on VirusTotal; however, sandbox analysis (AnyRun) revealed no malicious behavior.
Further investigation identified that the request was blocked by the firewall, and the user agent string explicitly indicated a testing scenario:
Firewall Test - Dont Block.
Based on all findings, the activity was determined to be part of a controlled firewall/security test, not an actual attack.
🚨 Alert Overview
- Event ID: 28
- Rule: SOC105 – Requested T.I. URL Address
- Severity: High
- Source Host: BillPRD
- Source IP: 172.16.17.47
- Destination IP: 115.99.150.132
- User: Bill
- Action: Blocked
🔍 Investigation Steps
1️⃣ URL Analysis
http://115.99.150.132:56841/Mozi.m
- VirusTotal:
- 8/95 detections
- Tagged as:
- Malware
- Suspicious
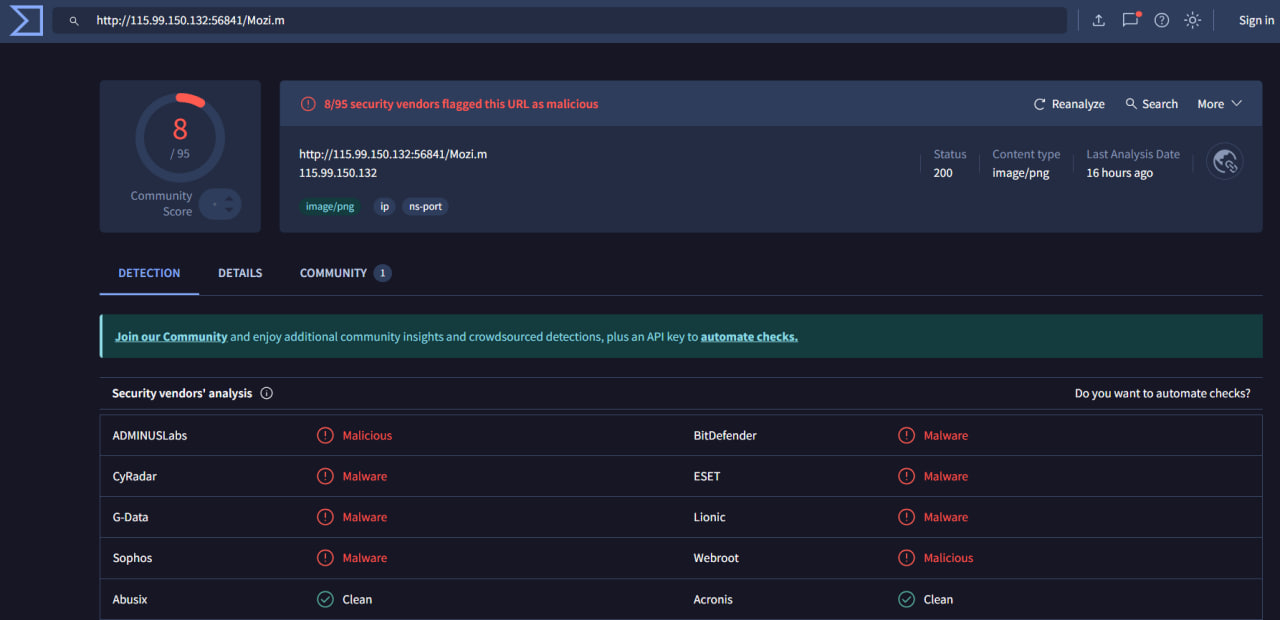
⚠️ Observation: Moderate detection → requires further validation.
2️⃣ Sandbox Analysis (AnyRun)
- No malicious behavior observed:
- No process injection
- No suspicious network activity
- No payload execution
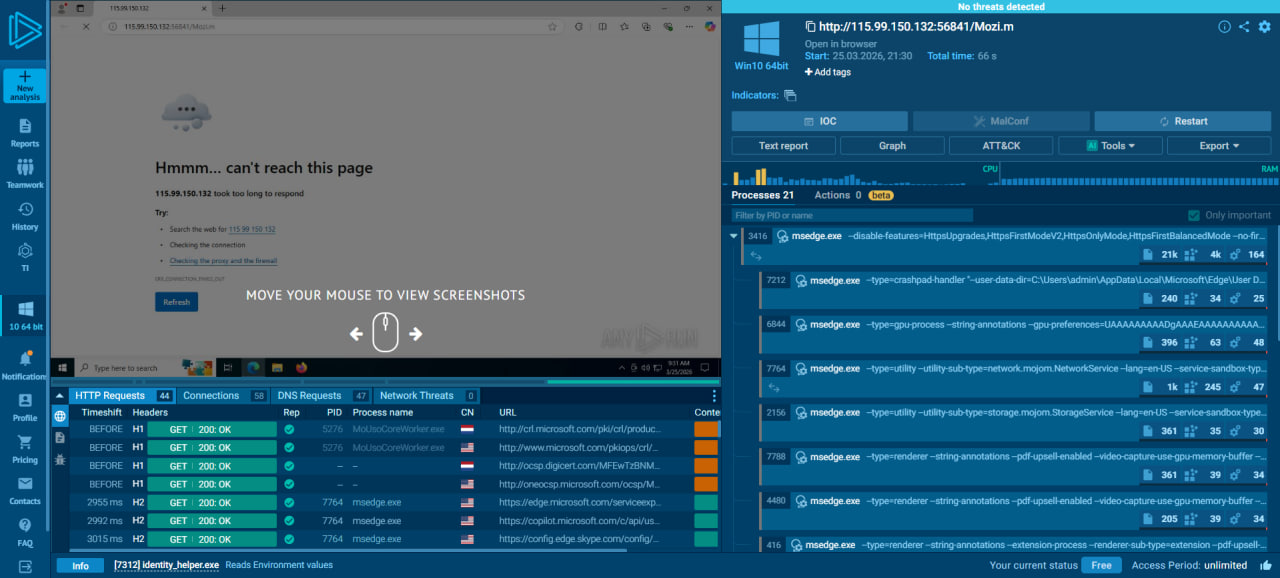
✅ Conclusion: No runtime malicious activity.
3️⃣ Hybrid Analysis Check
- Marked as malicious
- However:
- Last sandbox run was outdated
- No recent dynamic evidence
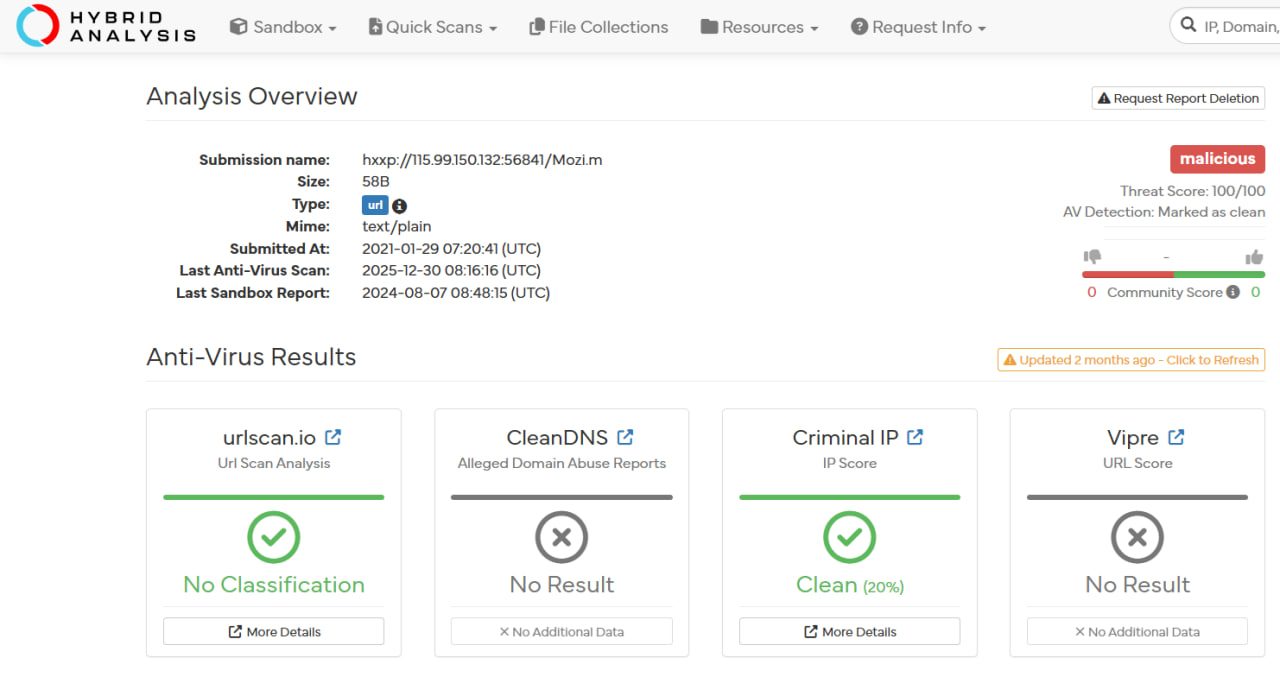
⚠️ Conclusion: Intelligence is stale / not reliable alone.
4️⃣ Log Analysis (Critical Step)
Raw log findings:
Request URL: http://115.99.150.132:56841/Mozi.m
- Action: Blocked
- Process: chrome.exe
- User Agent: Firewall Test - Dont Block
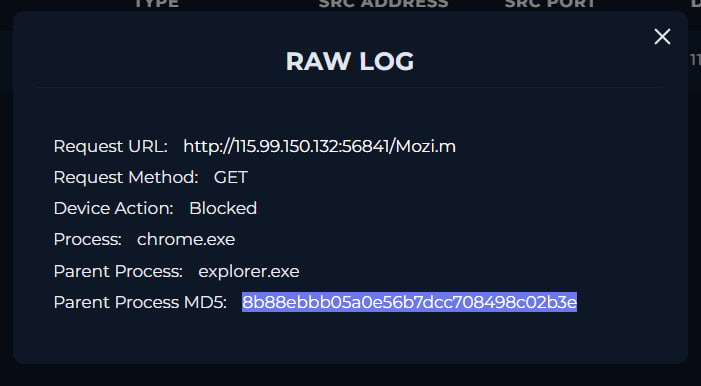
🔥 Key Insight:
- Traffic was blocked before execution
- User agent clearly indicates intentional testing activity
⚠️ Final Verdict
| Category | Result |
|---|---|
| URL Reputation | Suspicious |
| Sandbox Result | No Malicious Behavior |
| Firewall Action | Blocked |
| Context | Security Test Activity |
| Impact | None |
| Severity | Low |
| Verdict | ⚠️ Benign (Security Test / False Positive Context) |
🛡️ Actions Taken
- 🔍 Investigated URL, sandbox, and threat intel sources
- 📌 Verified firewall successfully blocked the request
- 🧠 Identified test indicator in user agent
- 📝 Classified activity as benign test activity
📌 Conclusion
This alert represents a controlled security test rather than an actual attack.
The investigation revealed:
Suspicious URL → Blocked by Firewall → No Execution → Test Indicator Present
Despite moderate threat intelligence detections, the absence of malicious behavior and the presence of a test-specific user agent strongly indicate that this was an intentional simulation or validation activity.
This case highlights the importance of:
- 🧠 Understanding context beyond threat intelligence
- 🔍 Correlating logs with behavioral analysis
- ⚠️ Avoiding over-reliance on static detections
- 🛡️ Recognizing internal security testing patterns
tags: