SOC105 – Suspicious URL Request (Benign GitHub Resource)
by
🧠 Summary
This investigation was triggered by a SOC105 – Requested T.I. URL Address alert involving a request to a GitHub-hosted resource.
Initial review flagged the URL as suspicious; however, deeper analysis revealed that the request was made to a legitimate GitHub content delivery domain.
Further validation using VirusTotal, AnyRun sandbox, and IP reputation checks confirmed that the activity was benign.
The alert was ultimately classified as a False Positive.
🚨 Alert Overview
- Event ID: 20
- Rule: SOC105 – Requested T.I. URL Address
- Severity: High
- Source Host: gitServer
- Source IP: 172.16.20.4
- Destination IP: 151.101.112.133
- Destination Domain: raw.githubusercontent.com
- User: gitUser
- Action: Allowed
🔍 Investigation Steps
1️⃣ URL Analysis
https://raw.githubusercontent.com/django/django/master/setup.py
- VirusTotal results:
- 1/95 vendors flagged as malicious
- Content type:
text/plain - Status:
404 Not Found
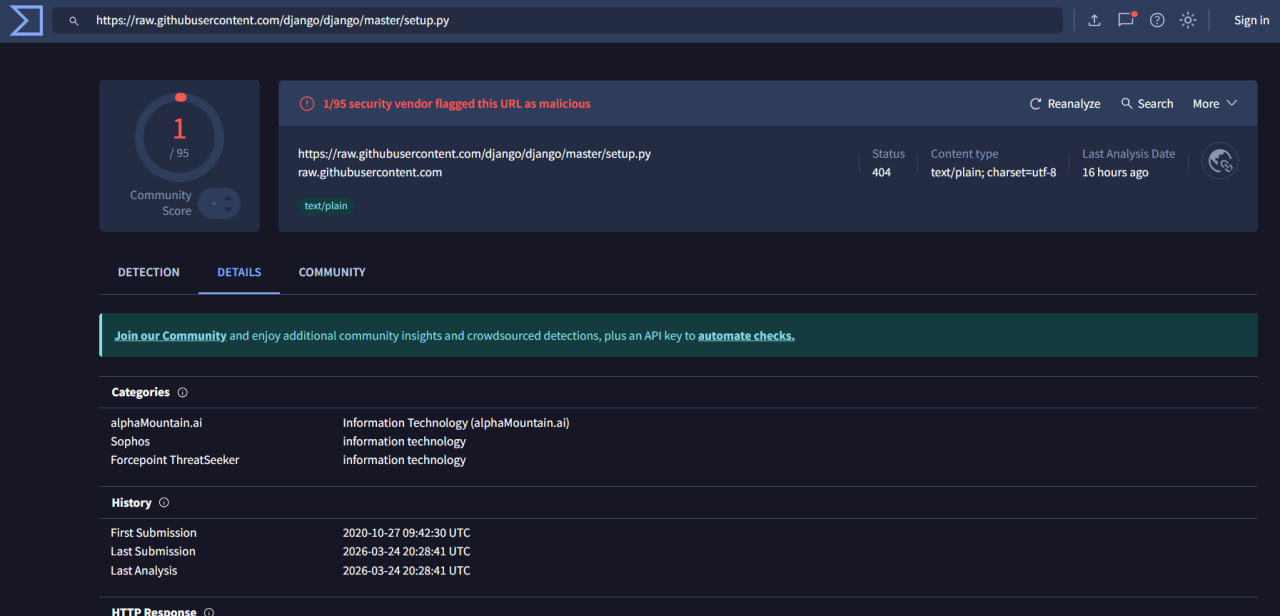
✅ Conclusion: Very low detection → likely false positive.
2️⃣ Sandbox Analysis (AnyRun)
- The URL was analyzed in a sandbox environment
- Observations:
- No suspicious behavior detected
- No malicious processes spawned
- No network anomalies
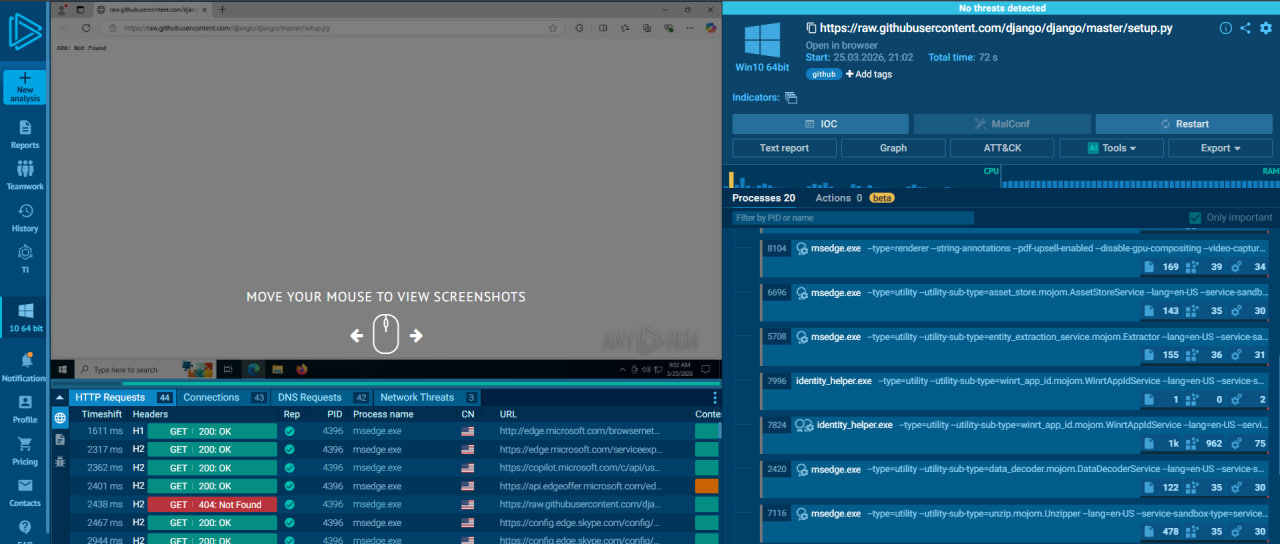
✅ Conclusion: No signs of malicious activity.
3️⃣ Network & Traffic Analysis
- HTTP logs show:
- Request returned 404 Not Found
- No payload delivered
- Process involved:
msedge.exe(browser process)
✅ Conclusion: No file download or execution occurred.
4️⃣ IP Reputation Analysis
-
Destination IP:
151.101.112.133 -
VirusTotal:
- 0/94 detections
- ASN: Fastly, Inc. (legitimate CDN provider)
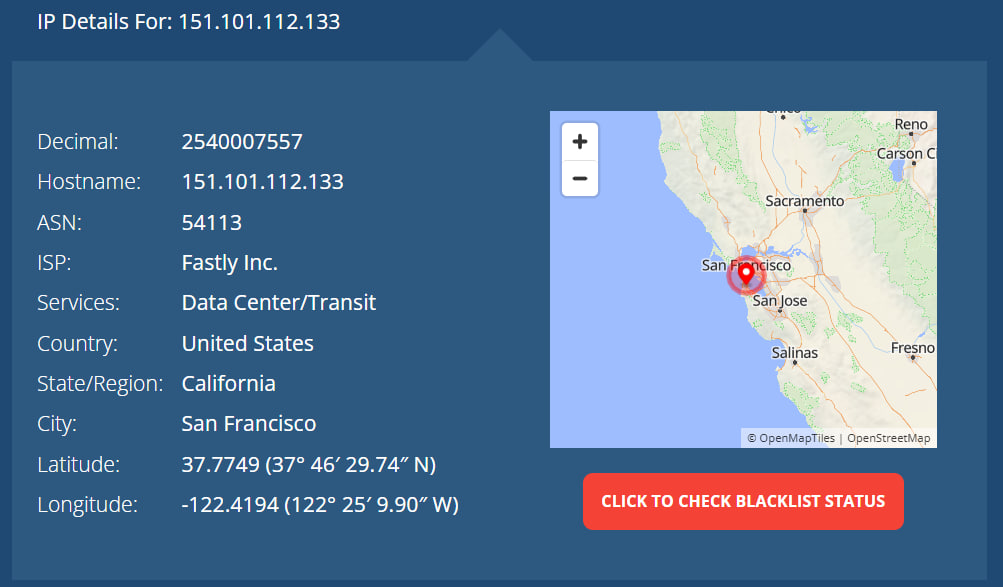
✅ Conclusion: IP belongs to a trusted CDN (GitHub infrastructure).
⚠️ Final Verdict
| Category | Result |
|---|---|
| URL Reputation | Clean / Low Risk |
| Sandbox Result | No Malicious Behavior |
| IP Reputation | Trusted (Fastly CDN) |
| User Activity | Legitimate Request |
| Impact | None |
| Severity | Low |
| Verdict | ❌ False Positive |
🛡️ Actions Taken
- 🔍 Investigated URL, IP, and sandbox behavior
- ✅ Confirmed no malicious activity
- 📌 Marked alert as False Positive
- 📝 Documented findings
📌 Conclusion
This alert represents a false positive triggered by automated threat intelligence detection on a legitimate resource.
The investigation confirmed that:
GitHub CDN URL → No Payload → No Execution → No Threat
Despite being flagged, the URL belongs to a trusted platform (GitHub via Fastly CDN) and did not exhibit any malicious behavior.
This case highlights the importance of contextual analysis in SOC operations, where not all flagged alerts indicate real threats.
Proper validation steps such as sandboxing, IP reputation checks, and log analysis are essential to avoid unnecessary escalation.
tags: