SOC105 – Malicious URL Access Leading to Trojan Infection
by
🧠 Summary
This investigation was triggered by a SOC105 – Requested T.I. URL Address alert involving a connection to a suspicious domain: pssd-ltdgroup.com.
Threat intelligence analysis using VirusTotal revealed that the URL was flagged as malicious by multiple vendors.
Further investigation confirmed that a malicious Excel file (.xlsm) containing VBA macros was downloaded and executed on the endpoint.
The file was identified as a Trojan, and the affected system (BillPRD) was immediately contained.
🚨 Alert Overview
- Event ID: 16
- Rule: SOC105 – Requested T.I. URL Address
- Severity: High
- Source Host: BillPRD
- Source IP: 172.16.17.47
- Destination IP: 5.188.0.251
- Destination Domain: pssd-ltdgroup.com
- User: Mike01
- Action: Allowed
🔍 Investigation Steps
1️⃣ URL Analysis
The requested URL was analyzed using VirusTotal:
https://pssd-ltdgroup.com
- 13/95 vendors flagged the URL as malicious
- Classified as:
- Phishing
- Malware hosting
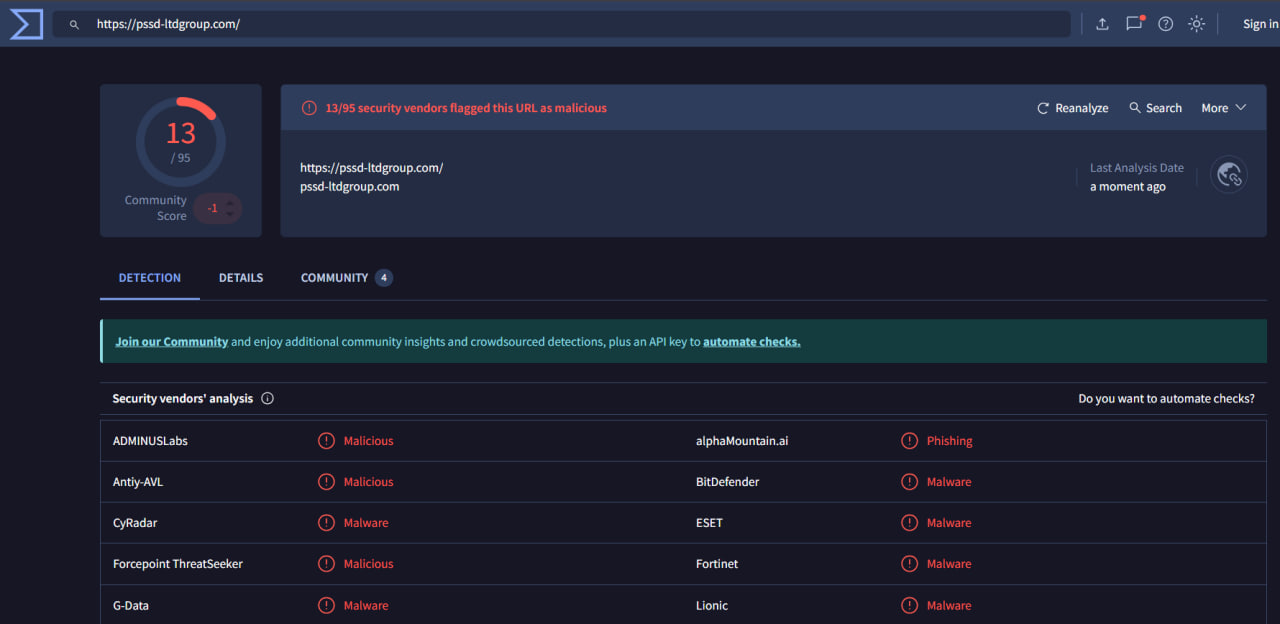
✅ Conclusion: The domain is malicious and likely used for malware delivery.
2️⃣ Log Analysis
Raw logs confirmed that the user accessed the malicious URL and downloaded a file.
Evidence:
Request URL: https://pssd-ltdgroup.com
File: Krankheitsmeldung_092020_07.xlsm
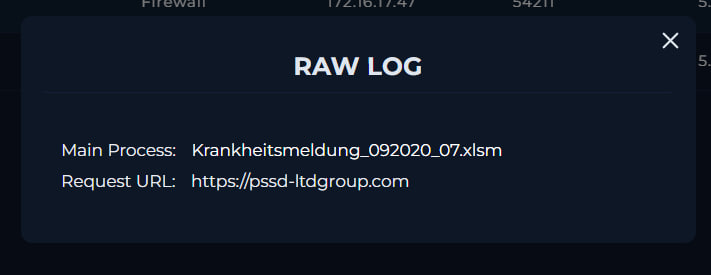
✅ Conclusion: The malicious URL successfully delivered a payload.
3️⃣ Endpoint Analysis
The affected host BillPRD showed execution of the downloaded file:
- File path:
C:\Users\Bill\Desktop\Krankheitsmeldung_092020_07.xlsm
- File size: 558 KB
- Executed shortly after download
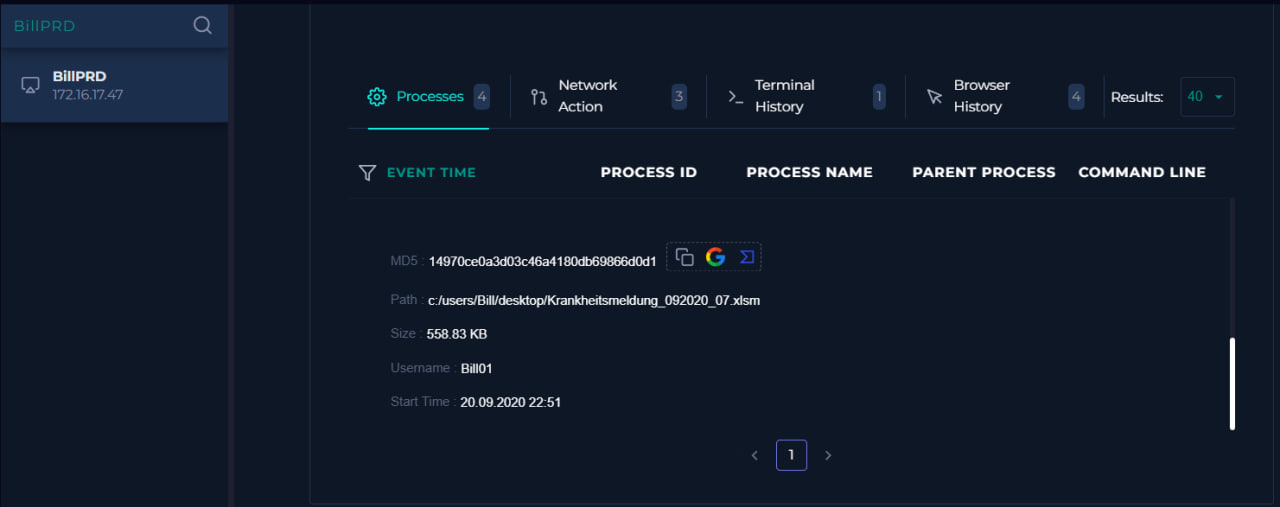
✅ Conclusion: The file was executed by the user → confirms user-driven infection.
4️⃣ File Analysis (Malware Confirmation)
The file hash was analyzed on VirusTotal:
- 47/66 vendors flagged it as malicious
Key indicators:
- Malicious VBA macros
- Obfuscated code
- Auto-execution behavior
- Suspicious API calls
Tags observed:
macrospowershellobfuscatedrun-dllauto-open
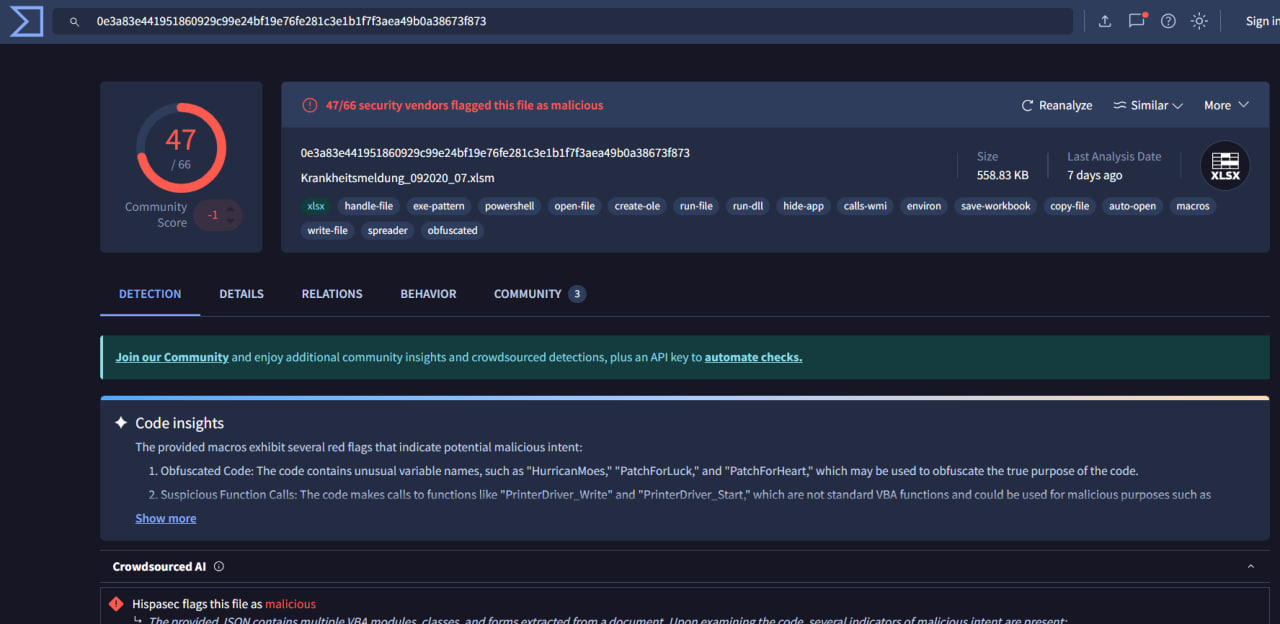
✅ Conclusion: Confirmed Trojan malware delivered via malicious Excel macro document.
🧬 MITRE ATT&CK Mapping
| Tactic | Technique |
|---|---|
| Initial Access | T1566.001 – Phishing: Spearphishing Attachment |
| Execution | T1204.002 – User Execution: Malicious File |
| Execution | T1059.005 – Command and Scripting Interpreter (VBA) |
| Defense Evasion | T1027 – Obfuscated Files or Information |
| Command & Control | T1071.001 – Web Protocols |
⚠️ Final Verdict
| Category | Result |
|---|---|
| URL Reputation | Malicious |
| File Analysis | Trojan (Malicious VBA Macro) |
| User Activity | Downloaded & Executed File |
| Impact | System Compromised |
| Severity | High |
| Verdict | ✅ True Positive |
🛡️ Actions Taken
- 🚫 Contained affected host (BillPRD)
- 🔍 Investigated URL and file indicators
- 🧹 Prevented further execution and spread
- 📌 Confirmed malware classification via threat intelligence
📌 Conclusion
This incident demonstrates a classic phishing-based malware delivery attack, where a user accessed a malicious URL that served a weaponized Excel document containing VBA macros.
Upon execution, the file initiated malicious activity consistent with Trojan behavior, confirmed by multiple security vendors.
The attack chain can be summarized as:
Malicious URL → File Download → User Execution → Trojan Infection
Timely detection through threat intelligence and log analysis enabled rapid containment of the affected host, preventing further escalation.
This case highlights the importance of:
- 🔐 Blocking malicious domains at the network level
- 📧 Strengthening user awareness against phishing attacks
- 🛡️ Monitoring macro-enabled document execution
- ⚡ Acting quickly on high-confidence threat intelligence alerts
tags: