SOC145 – Ransomware Detected (Avaddon Ransomware Infection)
by
🧠 Summary
This investigation was triggered by a SOC145 – Ransomware Detected alert involving a suspicious executable named ab.exe.
Initial threat intelligence analysis using VirusTotal revealed a high detection rate (62/72), strongly indicating malicious activity.
Further dynamic analysis using AnyRun sandbox confirmed ransomware behavior, including execution of WMIC commands to delete shadow copies, a known technique used by ransomware to prevent recovery.
Additional validation using Joe Sandbox identified the malware as part of the Avaddon ransomware family, associated with the RIDDLE SPIDER threat group.
The affected host was immediately contained, and the alert was classified as a True Positive ransomware infection.
🚨 Alert Overview
- Event ID: 92
- Rule: SOC145 – Ransomware Detected
- Severity: Critical
- Source Host: MarkPRD
- Source IP: 172.16.17.88
- File Name: ab.exe
- File Hash (MD5):
0b486fe0503524cfe4726a4022fa6a68 - File Size: 775.50 KB
- Action: Allowed
🖥️ Endpoint Information
- Hostname: MarkPRD
- Operating System: Windows 10 (64-bit)
- User Activity: File download and execution
🔍 Initial Findings
- Suspicious executable detected on endpoint
- File execution allowed by system
- High severity alert triggered
⚠️ Immediate deep-dive investigation required due to ransomware risk.
🧪 Threat Intelligence – File Analysis
🔎 VirusTotal (File Hash)
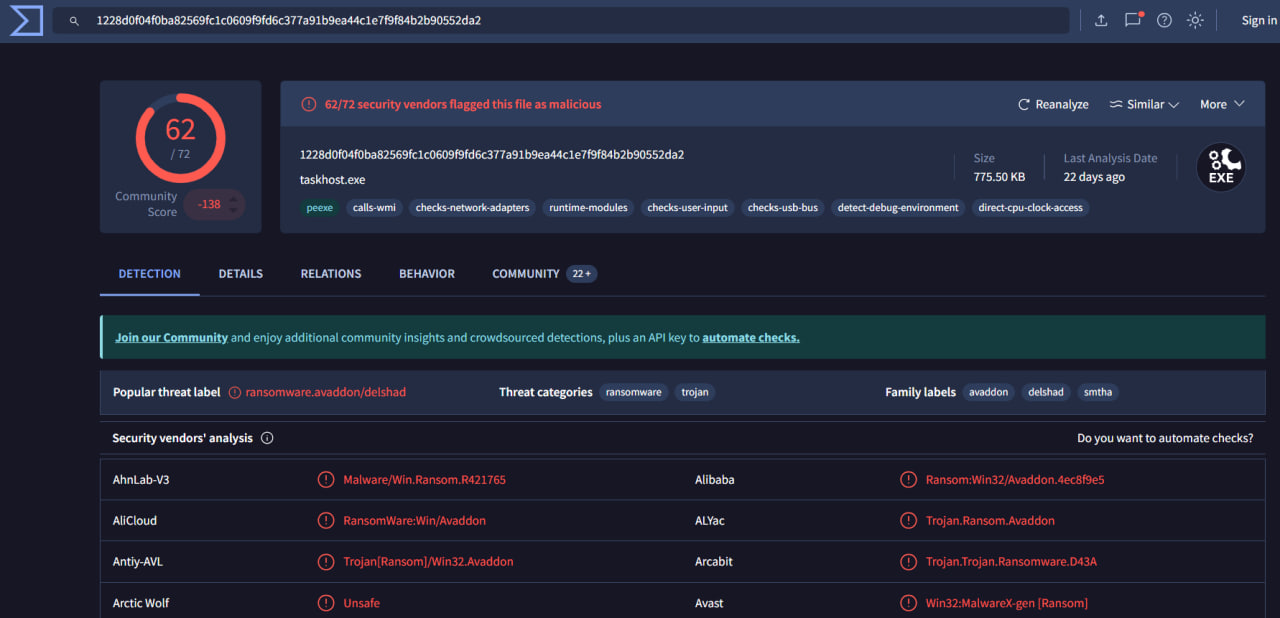
| Result | Value |
|---|---|
| Detection Ratio | 62 / 72 |
| Verdict | Malicious |
🧬 Threat Classification
- Malware Type: Ransomware
- Family: Avaddon
- Associated Labels: Trojan, Ransomware
🧠 Interpretation
- Extremely high detection rate → confirmed malware
- Multiple vendors classify it as Avaddon ransomware
🧬 Dynamic Analysis (AnyRun Sandbox)
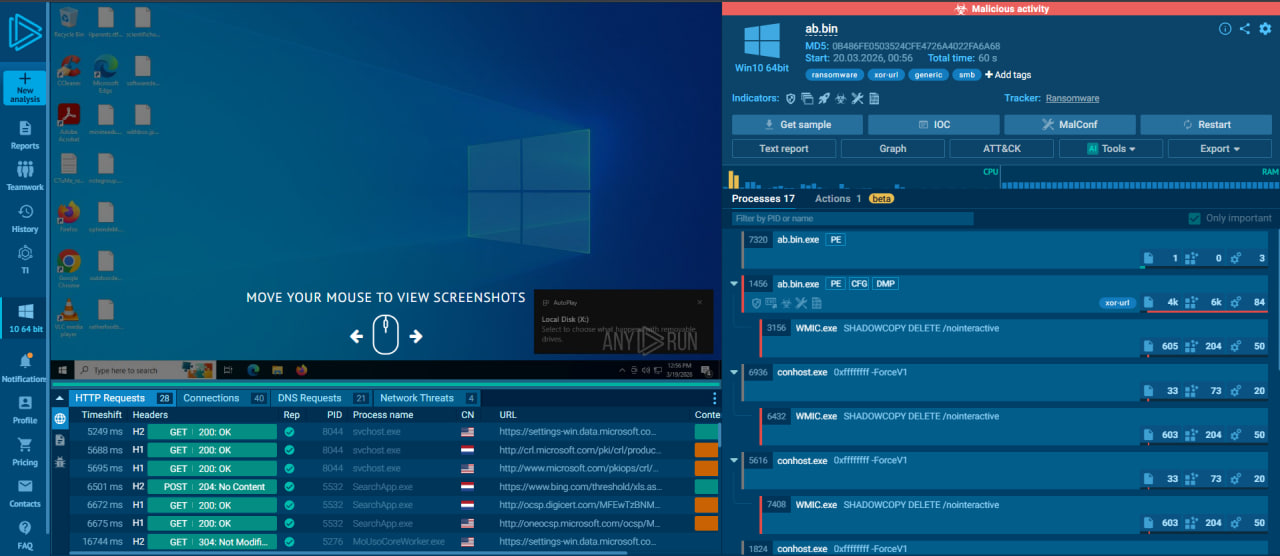
🔎 Observations
- File executed as
ab.bin.exe - Multiple suspicious child processes spawned
- Use of WMIC commands
🚨 Critical Behavior Detected
WMIC.exe SHADOWCOPY DELETE /nointeractive
🧠 Analysis
- This command deletes volume shadow copies
- Prevents victim from restoring files
- Strong indicator of ransomware behavior
📊 Process Behavior Analysis
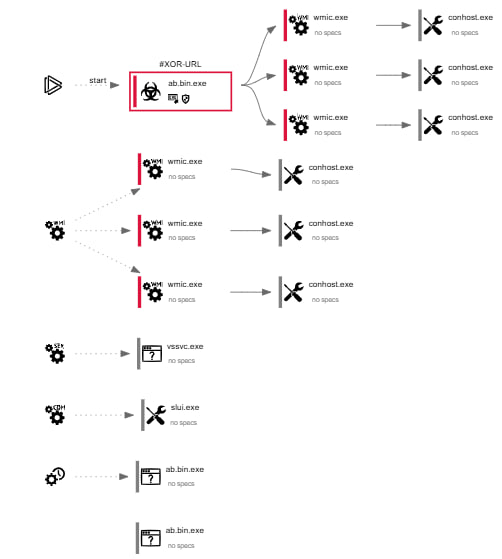
🔎 Key Findings
- Parent process:
ab.bin.exe - Child processes:
WMIC.execonhost.exevssvc.exe
🧠 Interpretation
- Process chain indicates:
- Execution
- System modification
- Defense evasion
🧪 Threat Intelligence – Malware Family
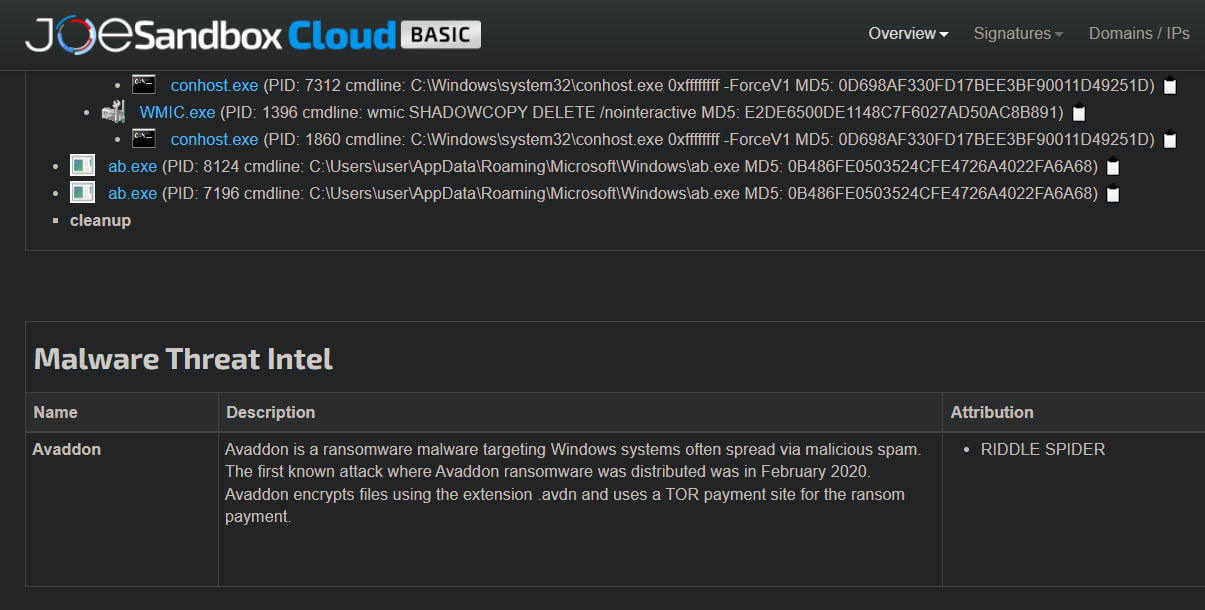
🔎 Joe Sandbox Findings
| Attribute | Value |
|---|---|
| Malware Family | Avaddon |
| Threat Type | Ransomware |
| Attribution | RIDDLE SPIDER |
🧠 Intelligence Insight
- Avaddon ransomware:
- Encrypts files with
.avdnextension - Uses TOR-based ransom payment portals
- Commonly distributed via phishing or malware loaders
- Encrypts files with
📊 Behavioral Indicators
| Indicator | Status |
|---|---|
| Malicious File Execution | ✅ Confirmed |
| Shadow Copy Deletion | ✅ Confirmed |
| Ransomware Behavior | ✅ Confirmed |
| Known Malicious Hash | ✅ Confirmed |
| Sandbox Malicious Activity | ✅ Confirmed |
🧾 Investigation Steps
- Reviewed alert metadata and file details
- Analyzed file hash in VirusTotal
- Observed high detection ratio (62/72)
- Executed file in AnyRun sandbox
- Identified ransomware behavior (shadow copy deletion)
- Analyzed process tree and system activity
- Verified malware family using Joe Sandbox
- Correlated all threat intelligence data
- Confirmed ransomware infection
- Contained affected endpoint
🚨 Incident Response Actions
- ✅ Host isolated / contained
- ✅ Malicious file identified and analyzed
- ✅ Ransomware behavior confirmed
- ✅ Threat intelligence correlation completed
- ✅ Evidence preserved for forensic investigation
🧬 MITRE ATT&CK Mapping
| Tactic | Technique | Description |
|---|---|---|
| Execution | T1204.002 – User Execution | User executed malicious file |
| Defense Evasion | T1070.004 – File Deletion | Shadow copies deleted |
| Impact | T1486 – Data Encrypted for Impact | Ransomware encryption |
| Discovery | T1082 – System Information Discovery | System info gathering |
| Command & Control | T1071.001 – Web Protocols | Potential C2 communication |
📌 Final Verdict
| Category | Result |
|---|---|
| Malware Presence | Confirmed |
| Threat Type | Avaddon Ransomware |
| Initial Vector | Malicious File Execution |
| Host Compromise | Confirmed |
| Alert Classification | True Positive |
| Incident Severity | Critical |
🏁 Conclusion
This alert represents a confirmed ransomware infection involving Avaddon malware.
Key evidence includes:
- High-confidence VirusTotal detections
- Ransomware behavior in sandbox (shadow copy deletion)
- Confirmed malware family via Joe Sandbox
The malware demonstrated classic ransomware techniques, including:
- Execution of malicious payload
- Disabling recovery mechanisms
- Preparing system for file encryption
Immediate containment was required to prevent:
- Data encryption
- System damage
- Lateral movement
tags: