SOC104 – Malware Detected (WinRAR False Positive Investigation)
by
🧠 Summary
This investigation was triggered by a SOC104 – Malware Detected alert involving the executable winrar600.exe.
Initial analysis suggested a potential malware detection; however, further investigation revealed that the file was downloaded from the official WinRAR website and exhibited no malicious behavior.
Threat intelligence (VirusTotal) showed only 1/70 detections, and dynamic analysis using AnyRun sandbox confirmed that the file behaved as a legitimate installer.
The alert was ultimately classified as a False Positive.
🚨 Alert Overview
- Event ID: 84
- Rule: SOC104 – Malware Detected
- Severity: Medium
- Source Host: SusieHost
- Source IP: 172.16.17.5
- File Name: winrar600.exe
- File Hash (MD5):
c74862e16bcc2b0e02cadb7ab14e3cd6 - File Size: 2.95 MB
- Action: Allowed
🖥️ Endpoint Information
- Hostname: SusieHost
- Operating System: Windows 10 (64-bit)
- User Activity: Browser-based download
🔍 Initial Findings
- No suspicious process activity
- No abnormal CLI usage
- No malicious browser artifacts
- Agent status reported as down
⚠️ Despite limited telemetry, investigation continued using sandbox and network analysis.
🌐 Network Analysis
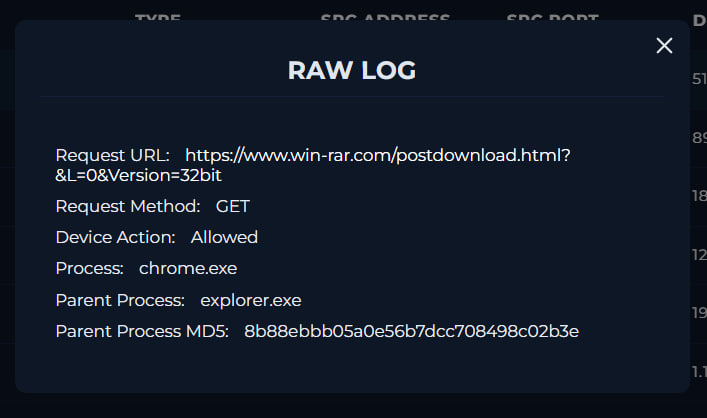
| Attribute | Value |
|---|---|
| Process | chrome.exe |
| Parent Process | explorer.exe |
| Request Method | GET |
| URL | https://www.win-rar.com/postdownload.html |
| Action | Allowed |
🧠 Analysis
- File downloaded via browser (user-initiated action)
- URL belongs to official WinRAR website
- No suspicious parameters or obfuscation
🌐 Threat Intelligence – IP Analysis
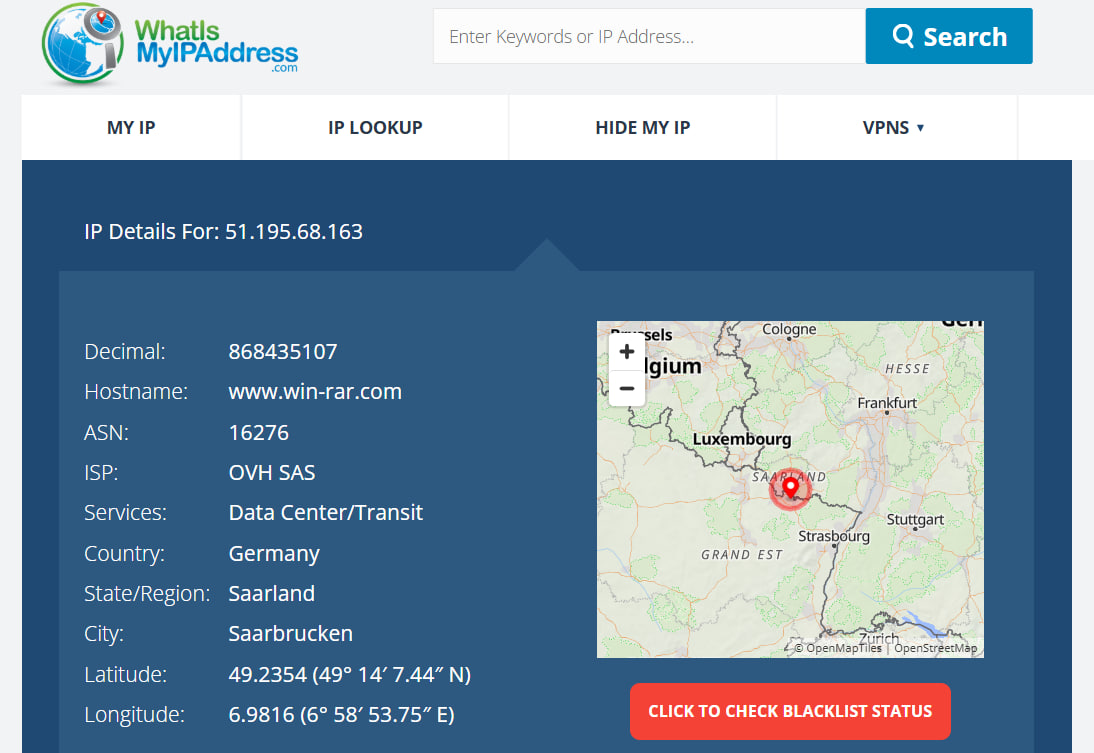
| Field | Value |
|---|---|
| IP Address | 51.195.68.163 |
| ISP | OVH SAS |
| Country | Germany |
| Hostname | win-rar.com |
📌 Intelligence Insight
- Legitimate hosting provider
- Matches official WinRAR infrastructure
- No malicious reputation detected
🧪 Threat Intelligence – File Analysis
🔎 VirusTotal (File Hash)
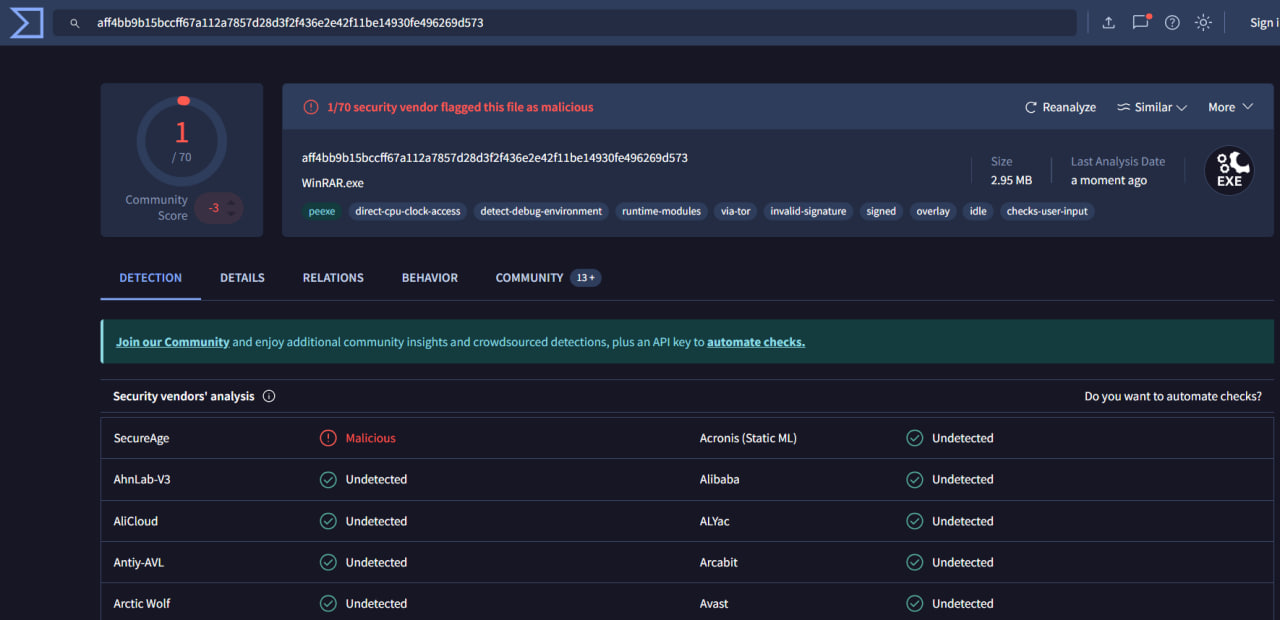
| Result | Value |
|---|---|
| Detection Ratio | 1 / 70 |
| Verdict | Likely Clean |
🧠 Interpretation
- Only 1 vendor flagged the file
- Very low detection → likely false positive
- No known malware family associated
🧬 Dynamic Analysis (AnyRun Sandbox)
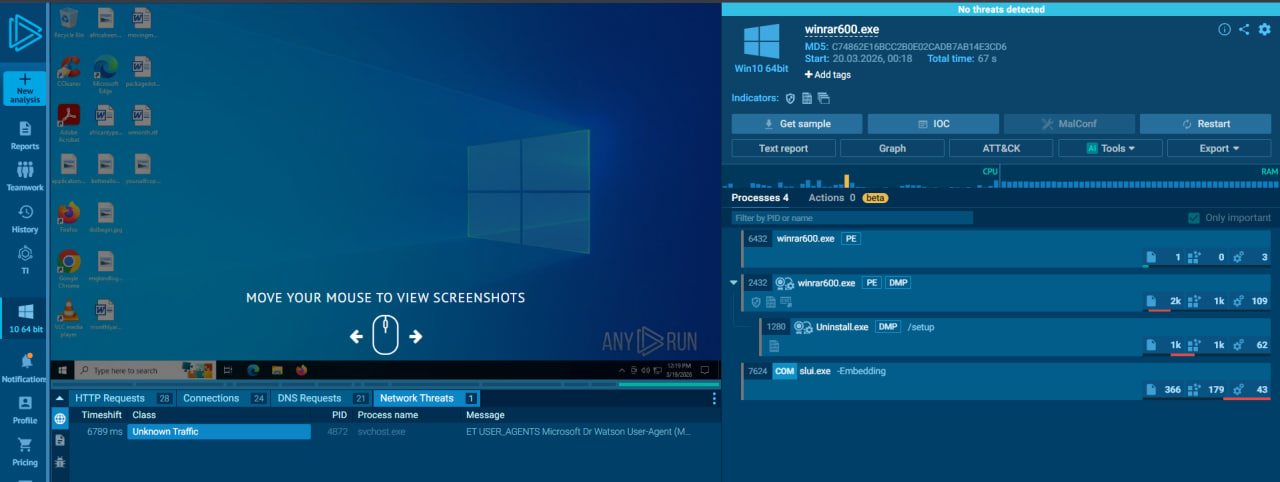
🔎 Observations
- No malicious behavior detected
- No persistence mechanisms
- No registry modifications
- No suspicious network communication
🧠 Process Activity
| Process Name | Description |
|---|---|
| winrar600.exe | Main executable |
| explorer.exe | Windows shell |
| chrome.exe | Browser |
| slui.exe | Windows licensing component |
✔️ All processes are legitimate
📊 Behavioral Indicators
| Indicator | Status |
|---|---|
| Malicious File Download | ❌ Not Detected |
| Suspicious Network Traffic | ❌ Not Detected |
| Known Malicious Hash | ❌ Not Detected |
| Sandbox Malicious Behavior | ❌ Not Detected |
| Endpoint Visibility | Limited |
🧾 Investigation Steps
- Reviewed alert metadata and file details
- Checked endpoint telemetry (process, CLI, browser)
- Identified download source from raw logs
- Verified URL legitimacy (win-rar.com)
- Performed VirusTotal hash analysis
- Observed low detection ratio (1/70)
- Executed file in AnyRun sandbox
- Confirmed absence of malicious behavior
- Correlated all findings
- Determined alert classification
🚨 Incident Response Actions
- ✅ Alert analyzed and investigated
- ✅ File verified as legitimate
- ⚠️ No containment required
- ⚠️ No remediation required
- ⚠️ Recommended monitoring due to agent downtime
📌 Final Verdict
| Category | Result |
|---|---|
| Malware Presence | Not Detected |
| Threat Type | Legitimate Software |
| Initial Vector | User Download |
| Host Compromise | Not Observed |
| Alert Classification | False Positive |
| Incident Severity | Low |
🏁 Conclusion
This alert represents a false positive detection involving a legitimate WinRAR installer.
Although initially flagged as malware, deeper analysis showed:
- Legitimate download source
- Clean sandbox behavior
- Extremely low VirusTotal detection
No evidence of compromise or malicious activity was found.
⚠️ The only concern observed was endpoint agent downtime, which should be addressed to ensure full visibility in future incidents.
tags: