SOC282 – Phishing Alert Escalated to Malware Execution via ZIP Payload
by
🧠 Summary
This investigation began as a Phishing Alert (SOC282 – Deceptive Mail Detected) triggered by a suspicious email sent to a user.
- Initial Analysis: Revealed signs of social engineering using a fake reward (“Free Coffee Voucher”) and a typosquatted sender domain.
- Deep Dive: Uncovered a malicious ZIP attachment (coffee.zip) and a redirect-based malware delivery chain using AWS S3.
- Critical Finding: Endpoint analysis confirmed that the user downloaded and executed the malware (Coffee.exe), leading to command execution via cmd.exe.
[!CAUTION] This case escalated from a phishing attempt to a confirmed malware execution incident (host compromise).
🚨 Alert Overview
- Event ID: 257
- Rule: SOC282 – Phishing Alert – Deceptive Mail Detected
- Severity: Medium → 🔴 Escalated to Critical * Source Email:
free@coffeeshooop.com - Destination User:
Felix@letsdefend.io - SMTP IP:
103.80.134.63 - Subject: Free Coffee Voucher
- Device Action: Allowed
📧 Email Analysis
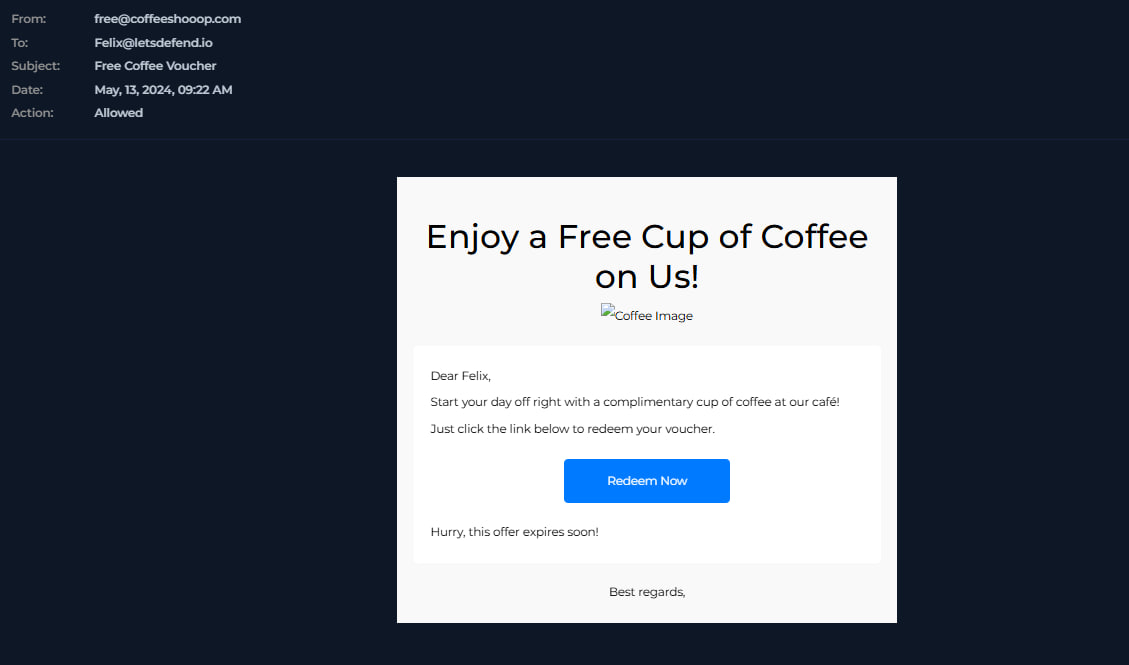
🚩 Indicators:
- Typosquatting domain:
coffeeshooop.com - Social engineering lure: “Free Coffee Voucher”
- Urgency tactic: “Hurry, this offer expires soon”
- Malicious link + attachment included
📎 Attachment Analysis
File Name: free-coffee.zip
🚨 Risk:
- Used to bypass email security.
- Likely contains executable payload.
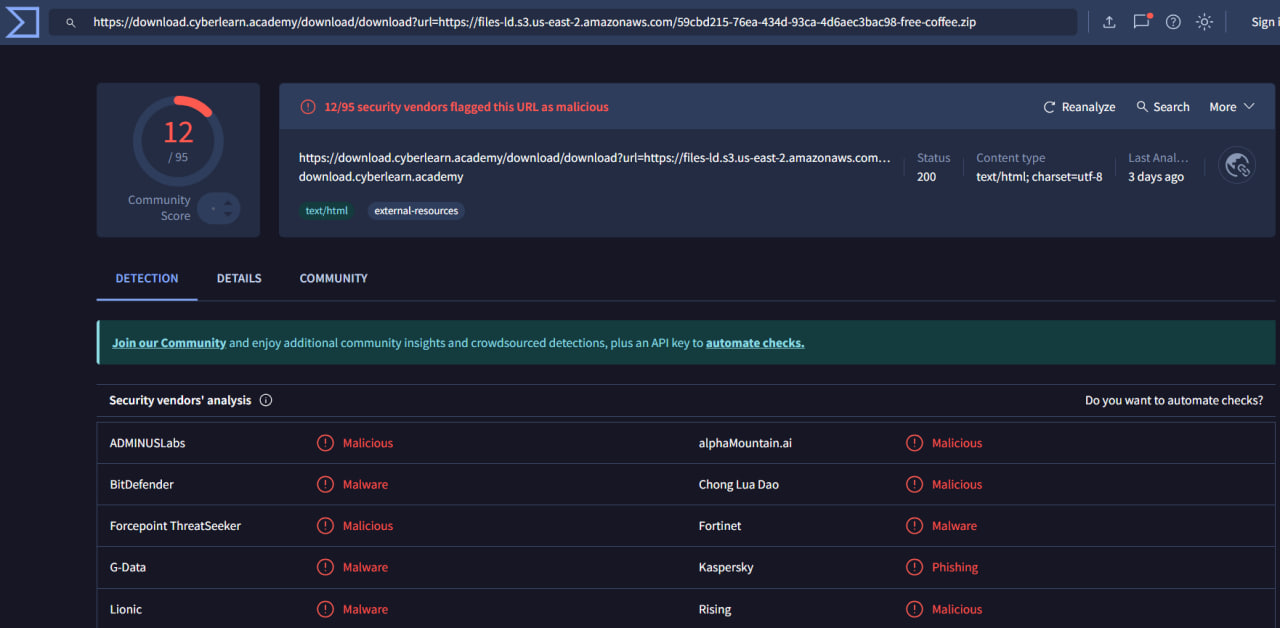
🌐 URL & Redirect Analysis
https://download.cyberlearn.academy/...
➡ Redirects to: AWS S3 → free-coffee.zip
🚩 Findings:
- Redirect chain used to evade detection.
- AWS S3 abused for payload hosting.
- Staged malware delivery.
🧪 VirusTotal Analysis
- Results: 12 / 95 vendors flagged as malicious.
- Classified as: Malware / Phishing.
💻 Endpoint Process Analysis (🔥 CRITICAL EVIDENCE)
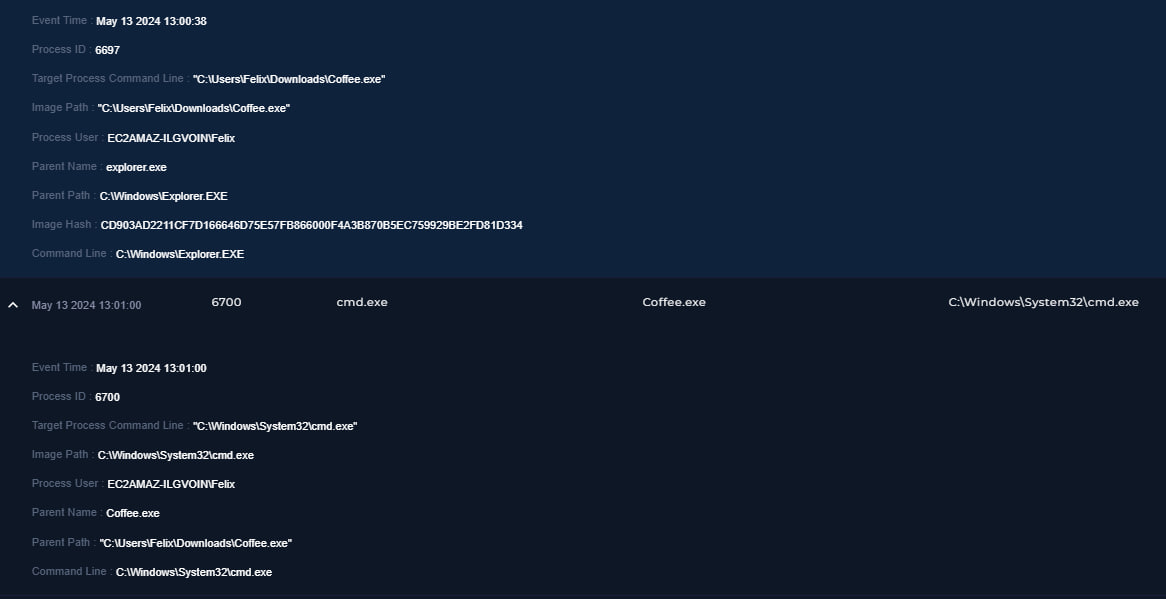
📌 Findings:
- File executed:
C:\Users\Felix\Downloads\Coffee.exe - Parent process:
explorer.exe - User Action: Indicates user manually executed the file.
🚨 Malicious Behavior Observed:
Process spawned: cmd.exe
Execution chain:
explorer.exe- ↳
Coffee.exe - ↳
cmd.exe(🔴 Confirmed Command Execution)
🔍 Additional Details:
- Process ID: 6697
- User: Felix
- Hash:
CD903AD2211CF7D166646D75E57FB866000F4A3B870B5EC759929BE2FD81D334
🔗 Full Attack Chain
- Phishing Email received.
- User clicks link / downloads ZIP.
- User extracts
free-coffee.zip. - User executes
Coffee.exe. - Malware spawns
cmd.exe. - System Compromise achieved.
🧾 Artifacts Identified
| Type | Value | Description |
|---|---|---|
| URL | https://download.cyberlearn.academy |
Malicious redirect URL |
| IP Address | 103.80.134.63 |
SMTP server |
| IP Address | 172.67.166.172 |
Hosting infrastructure |
| IP Address | 37.120.233.226 |
C2 IP Address |
| IP Address | 172.16.20.151 |
Felix Host IP Address (Affected Host) |
| File | Coffee.exe |
Malicious payload |
| Hash | CD903AD2...1D334 |
SHA256 File hash |
📊 Investigation Findings
| Category | Result |
|---|---|
| Phishing Email | Confirmed |
| Malicious Attachment | Confirmed |
| Malicious URL | Confirmed |
| File Download | Confirmed |
| File Execution | 🚨 Confirmed |
| Command Execution | 🚨 Confirmed |
| Host Compromise | 🔴 Confirmed |
📌 Final Verdict
- Attack Type: Phishing + Malware Execution
- Technique: Social Engineering + Payload Execution
- Payload: Malicious EXE (
Coffee.exe) - Impact: 🔴 Host Compromise
- Alert Classification: True Positive
- Severity: 🔴 Critical
🛡️ MITRE ATT&CK Mapping
| Tactic | ID | Technique | Description |
|---|---|---|---|
| Initial Access | T1566.002 |
Spearphishing Link | Phishing lure containing a malicious link to download.cyberlearn.academy. |
| Execution | T1204.002 |
User Execution: Malicious File | Victim manually downloaded, extracted, and executed Coffee.exe. |
| Execution | T1059.003 |
Command and Scripting Interpreter: Windows Command Shell | Coffee.exe spawned cmd.exe to execute arbitrary commands. |
| Command & Control | T1105 |
Ingress Tool Transfer | Use of AWS S3 and redirect chains to deliver the malicious ZIP payload. |
| Defense Evasion | T1036 |
Masquerading | Use of a “Free Coffee” lure and typosquatted domain to appear legitimate. |
🛑 Incident Response Actions
- Isolation: Endpoint identified as compromised; immediate isolation recommended.
- Process Kill: Malicious process execution confirmed and documented.
- IOC Logging: Indicators of Compromise (IOCs) added to blocklist.
- Remediation: Full threat eradication and system re-imaging required.
📝 Analyst Notes
The alert was triggered due to a phishing email containing a malicious attachment and embedded download link. The sender domain (coffeeshooop.com) was identified as a typosquatting domain.
Endpoint investigation confirmed that the user downloaded and executed the file (Coffee.exe), which subsequently spawned cmd.exe. This confirms successful malware execution and system compromise. The alert is classified as a True Positive and escalated to Critical severity.
[!ATTENTION] Please type in the analyst note manually, copy pasting this section entirely may result in unable to close this alert.
🏁 Conclusion
This case demonstrates a full attack lifecycle, highlighting the effectiveness of combining social engineering with cloud infrastructure abuse (AWS S3). Immediate response and containment are critical to prevent further lateral movement within the network.
tags: