SOC138 – Suspicious XLSM File Detected (Malicious Macro-Based Infection)
by
🧠 Summary
This investigation was triggered by a SOC138 – Detected Suspicious XLS File alert involving a macro-enabled Excel document (ORDER SHEET & SPEC.xlsm).
Threat intelligence confirmed that the file contains heavily obfuscated macros designed to execute malicious code. Behavioral indicators suggest exploitation techniques and payload execution.
Network logs further revealed suspicious outbound communication, confirming that the file was actively used in a malware infection scenario.
The affected host was immediately contained.
🚨 Alert Overview
- Event ID: 77
- Rule: SOC138 – Detected Suspicious XLS File
- Severity: Medium
- Source Host: Sofia
- Source IP: 172.16.17.56
- User: Sofia2020
- File Name: ORDER SHEET & SPEC.xlsm
- File Hash (SHA256):
7bcd31bd41686c32663c7cabf42b18c50399e3b3b4533fc2ff002d9f2e058813 - File Size: 2.66 MB
- Action: Allowed
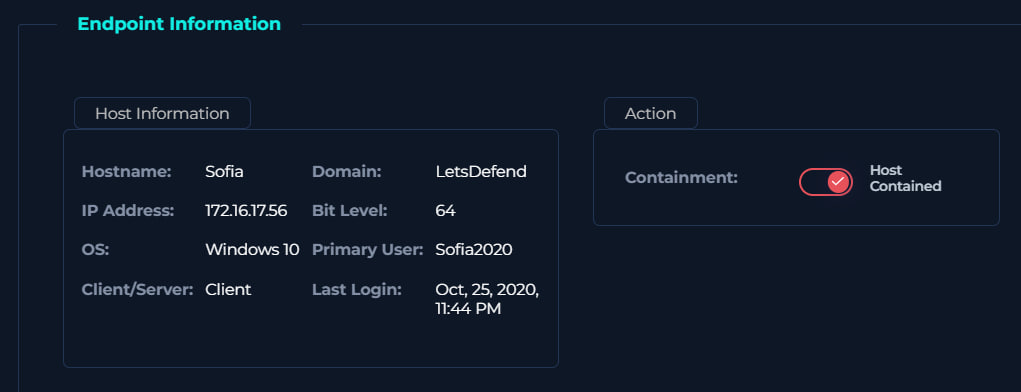
🖥️ Endpoint Information
- Hostname: Sofia
- Operating System: Windows 10 (64-bit)
- Domain: LetsDefend
- Primary User: Sofia2020
- Containment Status: ✅ Contained
🔍 File Analysis
🔎 VirusTotal Results
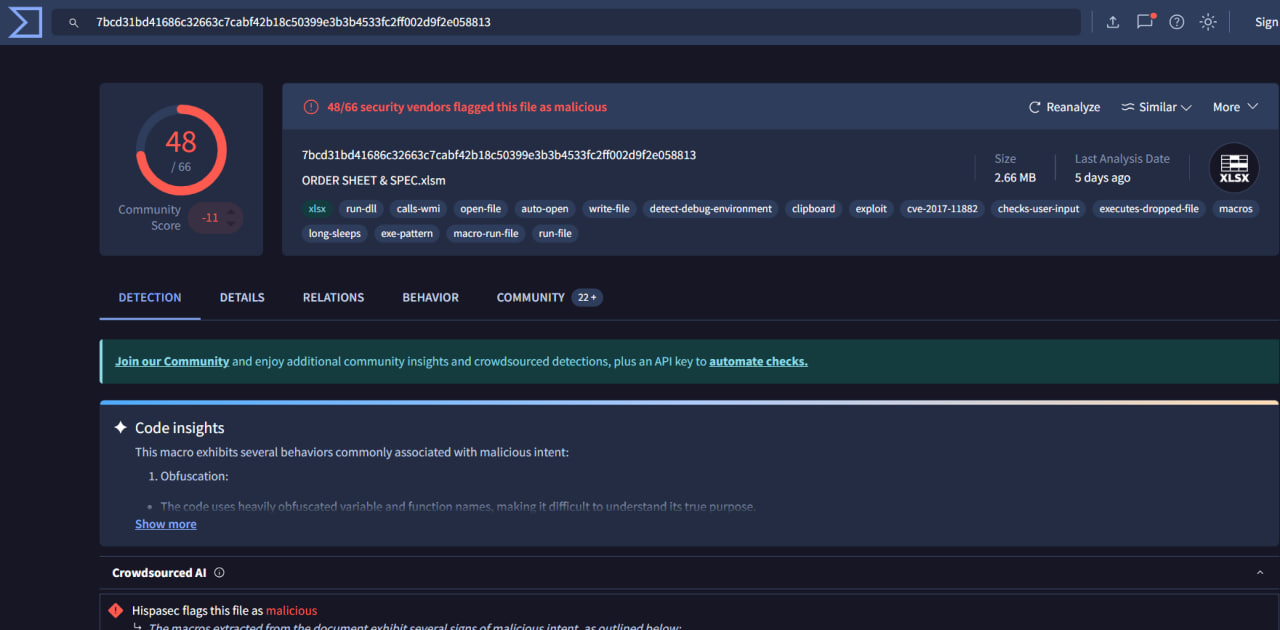
| Result | Value |
|---|---|
| Detection Ratio | 48 / 66 |
| Verdict | Malicious |
🧬 File Characteristics
- File Type: Excel Macro-Enabled File (.xlsm)
- Behavior Tags:
- macros
- obfuscated code
- auto-open execution
- run-dll / WMI calls
- exploit behavior (CVE-2017-11882)
- payload execution
🧠 Analysis
- High detection rate → confirmed malicious file
- Obfuscation → attempts to evade detection
- Macro execution → primary infection mechanism
- CVE reference → potential exploitation of known vulnerability
🌐 Network Analysis
| Attribute | Value |
|---|---|
| Source IP | 172.16.17.56 |
| Destination IP | 177.53.143.89 |
| Port | 443 |
| Protocol | HTTPS |
🧠 Analysis
- Suspicious outbound connection detected
- Encrypted traffic → possible C2 communication
- No legitimate business justification observed
📊 Log Analysis
📄 Raw Log Insight
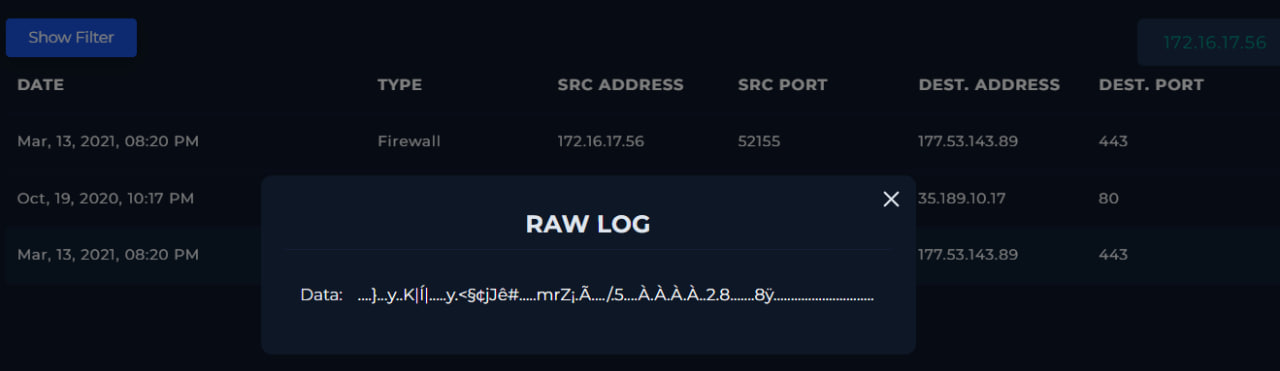
- Data appears:
- Encoded / obfuscated
- Non-human readable
🧠 Interpretation
- Likely:
- Encoded payload
- Encrypted communication
- Malware staging activity
🛡️ Affected Host Contained
📊 Behavioral Indicators
| Indicator | Status |
|---|---|
| Malicious File Detected | ✅ Confirmed |
| Macro Execution | ✅ Confirmed |
| Obfuscation | ✅ Present |
| Exploit Usage | ✅ Suspected (CVE-2017-11882) |
| External Communication | ✅ Confirmed |
| Host Compromise | ✅ Confirmed |
🧾 Investigation Steps
- Reviewed alert details and suspicious XLSM file
- Checked file hash in VirusTotal
- Confirmed high detection ratio (48/66)
- Analyzed macro behavior and obfuscation
- Identified exploit-related indicators
- Investigated firewall/network logs
- Detected suspicious outbound communication
- Analyzed raw log data (encoded payload)
- Contained the affected host
🚨 Incident Response Actions
- ✅ Host isolated / contained
- ✅ Malicious file identified
- ✅ Threat intelligence validated
- ✅ Network indicators identified
- ✅ Logs preserved for further analysis
🧬 MITRE ATT&CK Mapping
| Tactic | Technique | Description |
|---|---|---|
| Initial Access | T1566.001 – Phishing Attachment | Malicious Excel file delivery |
| Execution | T1204.002 – User Execution | User opened XLSM file |
| Execution | T1059.005 – Command Execution via Macros | Macro execution |
| Exploitation | T1203 – Exploitation for Client Execution | CVE-2017-11882 |
| Defense Evasion | T1027 – Obfuscated Files | Obfuscated macro code |
| Command & Control | T1071.001 – Web Protocols | HTTPS communication |
| Impact | T1105 – Ingress Tool Transfer | Payload delivery |
📌 Final Verdict
| Category | Result |
|---|---|
| Malware Presence | Confirmed |
| File Type | Malicious XLSM (Macro-based) |
| Infection Method | Macro Execution |
| Exploit Involvement | Likely (CVE-2017-11882) |
| Command & Control | Suspected |
| Host Compromise | Confirmed |
| Alert Classification | True Positive |
| Incident Severity | High |
🏁 Conclusion
This alert represents a confirmed macro-based malware infection delivered via an Excel document.
The file utilized:
- Obfuscated macro code
- Auto-execution techniques
- Possible exploitation of known vulnerabilities
Network activity confirmed communication with an external system, indicating potential command-and-control interaction or payload delivery.
Immediate containment was required to prevent:
- Lateral movement
- Data exfiltration
- Further malware execution
tags: