SOC119 – Proxy Alert: Malicious Executable File Detected (False Positive)
by
🧠 Summary
This investigation was triggered by a SOC119 – Proxy: Malicious Executable File Detected alert involving a request to download a file from win-rar.com.
At first glance, the alert appeared suspicious due to executable file download behavior. However, detailed analysis confirmed that the activity was legitimate and related to a normal user-initiated download from the official WinRAR website.
All supporting evidence, including process execution, network activity, and threat intelligence results, confirmed this as a false positive alert.
🚨 Alert Overview
- Event ID: 83
- Rule: SOC119 – Proxy: Malicious Executable File Detected
- Severity: Medium
- Source Host: SusieHost
- Source IP: 172.16.17.5
- User: Susie
- Destination IP: 51.195.68.163
- Destination Domain: win-rar.com
- Request URL: https://www.win-rar.com/postdownload.html?&L=0&Version=32bit
- Action: Allowed
🖥️ Endpoint Information
- Hostname: SusieHost
- Operating System: Windows Environment
- User Activity: Browser-based download
🔍 Log Analysis
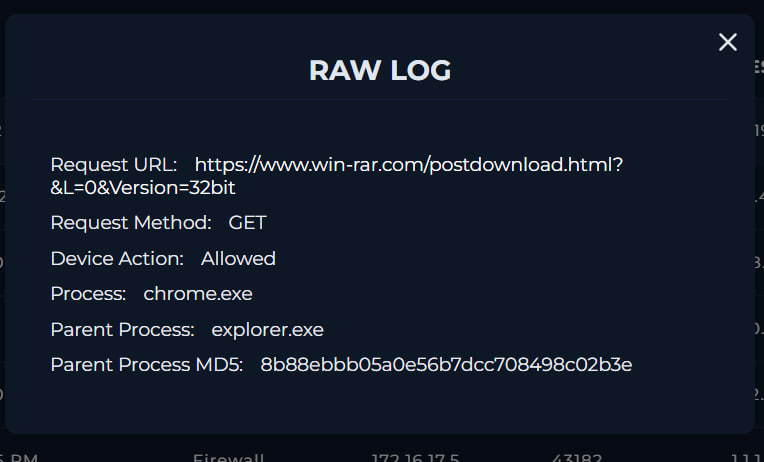
| Attribute | Value |
|---|---|
| Process | chrome.exe |
| Parent Process | explorer.exe |
| Request Method | GET |
| Action | Allowed |
🧠 Analysis
- Request originated from Chrome browser
- Parent process
explorer.exe→ normal user activity - Indicates manual user download, not malware execution
🌐 URL Analysis
🔎 VirusTotal (URL)
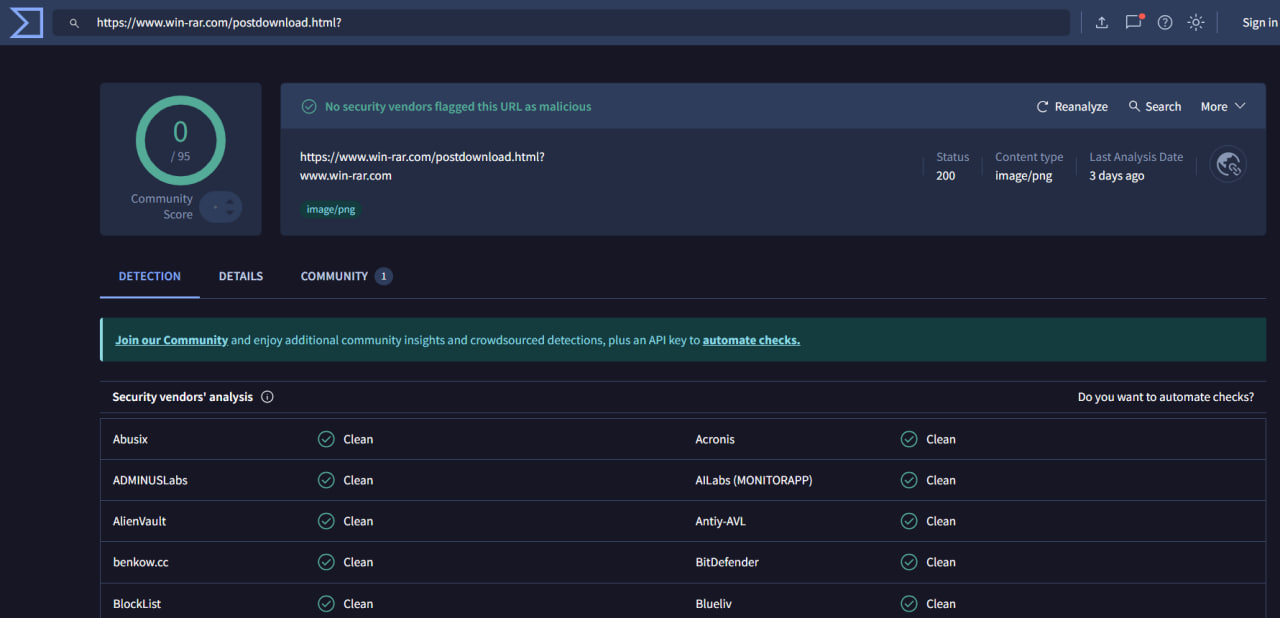
| Result | Value |
|---|---|
| Detection Ratio | 0 / 95 |
| Verdict | Clean |
- Official domain:
win-rar.com - No malicious indicators detected
🌐 IP Analysis
🔎 VirusTotal (IP: 51.195.68.163)
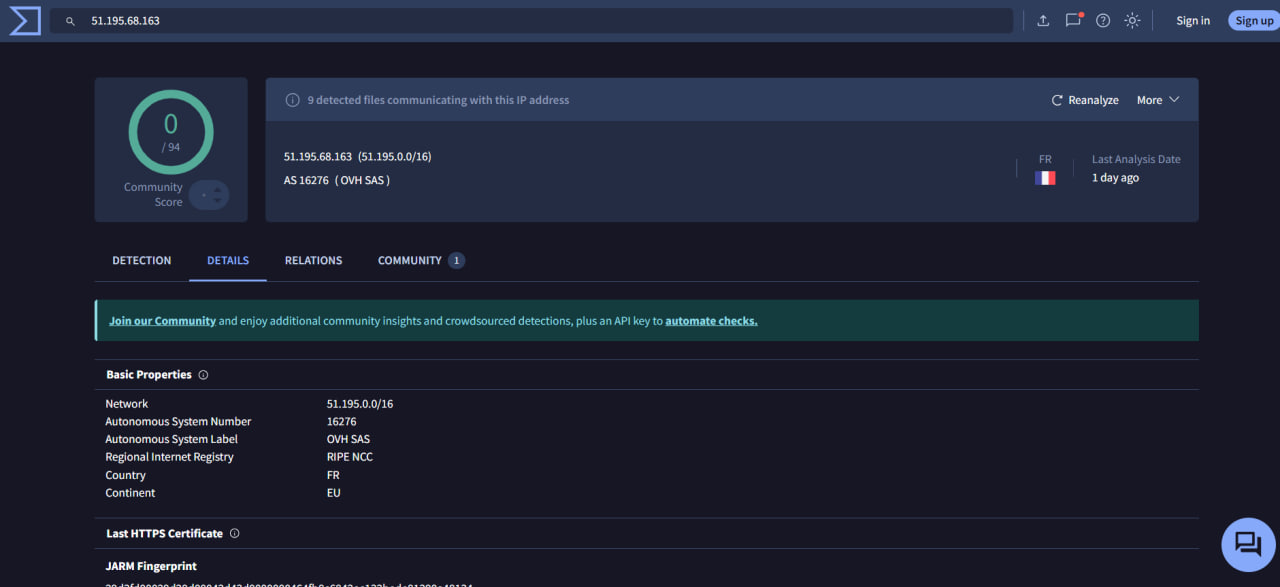
| Result | Value |
|---|---|
| Detection Ratio | 0 / 94 |
| ASN | OVH SAS |
| Country | France |
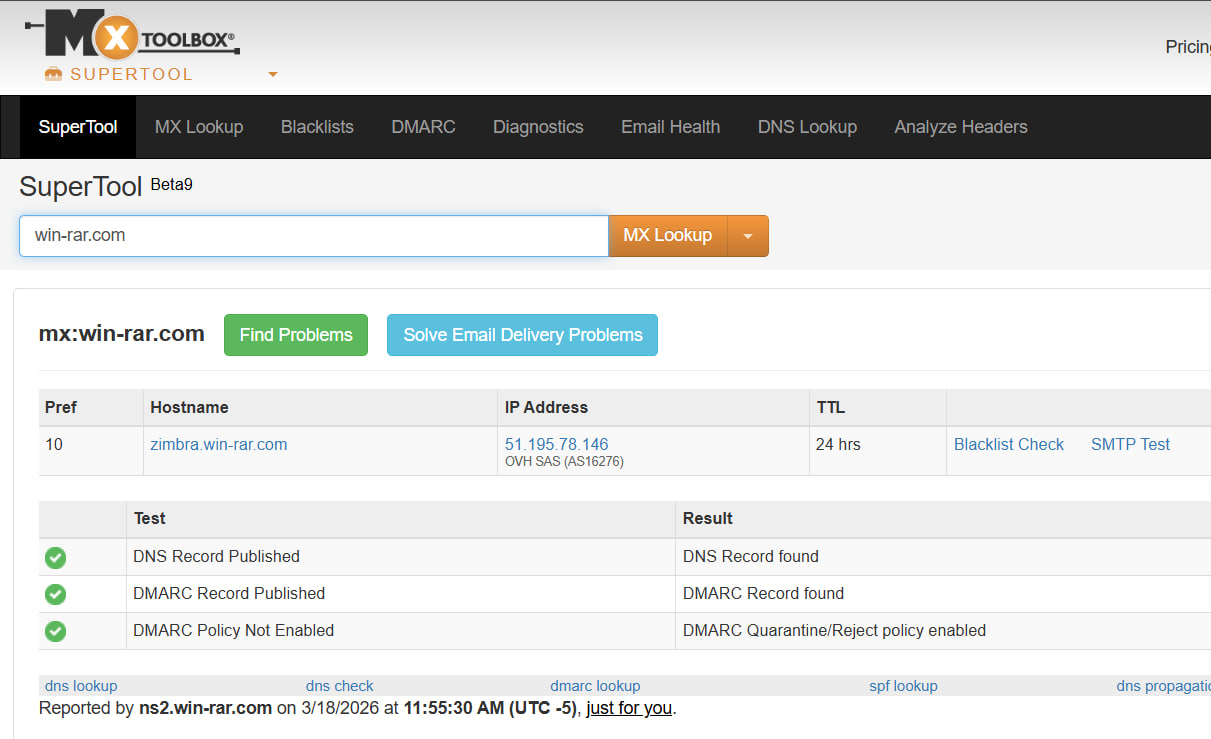
🔎 Domain Lookup
🧠 Analysis
- Hosting provider: OVH (legitimate cloud provider)
- No malicious reputation
- Common for hosting legitimate services
📊 Behavioral Analysis
| Check | Result |
|---|---|
| Suspicious Process | ❌ None |
| Malware Execution | ❌ None |
| Network Anomalies | ❌ None |
| CLI Activity | ❌ None |
| Browser History | ✅ Legitimate download |
| Endpoint Agent | ⚠️ Agent Down (Visibility Gap) |
⚠️ Key Observation
- Alert triggered due to:
- Executable file download detection
- However:
- No malicious payload confirmed
- No suspicious behavior observed
🧾 Investigation Steps
- Reviewed alert metadata and proxy logs
- Analyzed request URL and domain reputation
- Verified process chain (chrome.exe → explorer.exe)
- Checked endpoint telemetry (process, CLI, network)
- Investigated URL in VirusTotal
- Investigated destination IP reputation
- Correlated all findings with user activity
📌 Final Verdict
| Category | Result |
|---|---|
| File Source | Legitimate |
| Malware Presence | Not Detected |
| User Activity | Normal |
| Alert Classification | False Positive |
| Incident Severity | Informational |
🏁 Conclusion
This alert was triggered due to detection of an executable file download via proxy logs.
However, the request was made to the official WinRAR website and initiated by a legitimate browser process.
No indicators of compromise, malicious execution, or abnormal behavior were identified.
This activity is classified as a false positive, representing normal user download behavior.
tags: