SOC104 – Malware Detected (GoogleUpdate.exe False Positive)
by
🧠 Summary
This investigation was triggered by a SOC104 – Malware Detected alert involving a suspicious executable named googleupdate.exe.
Initial review raised concerns due to the filename being commonly abused by malware. However, deeper analysis revealed that the file was part of a legitimate Google Update process.
Despite a partial detection in sandbox analysis, all contextual and behavioral evidence confirmed that this was a false positive alert.
🚨 Alert Overview
- Event ID: 14
- Rule: SOC104 – Malware Detected
- Severity: High
- Source Host: JohnComputer
- Source IP: 172.16.17.82
- User: NT AUTHORITY\SYSTEM
- File Name: googleupdate.exe
- File Hash (MD5):
0bca3f16dd527b4150648ec1e36cb22a - File Size: 152.45 KB
- Action: Allowed
🖥️ Endpoint Information
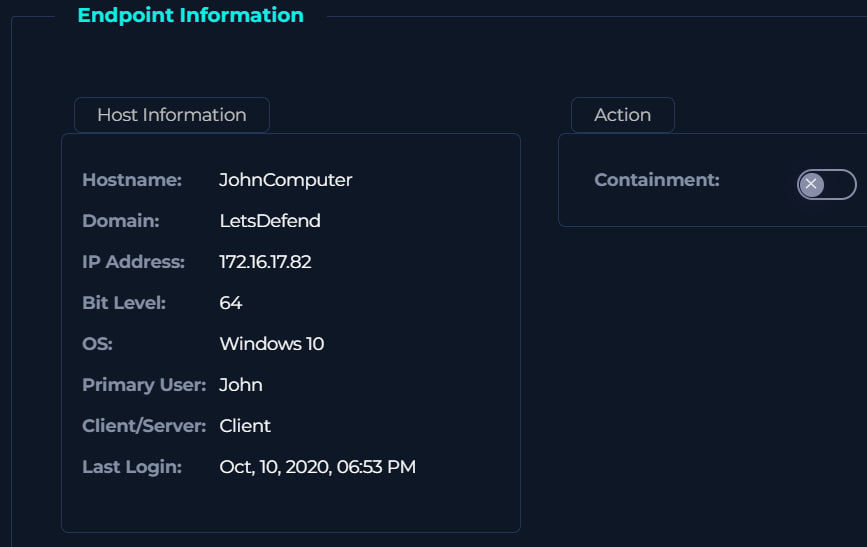
- Hostname: JohnComputer
- Operating System: Windows 10 (64-bit)
- Domain: LetsDefend
- Primary User: John
🔍 File & Process Analysis
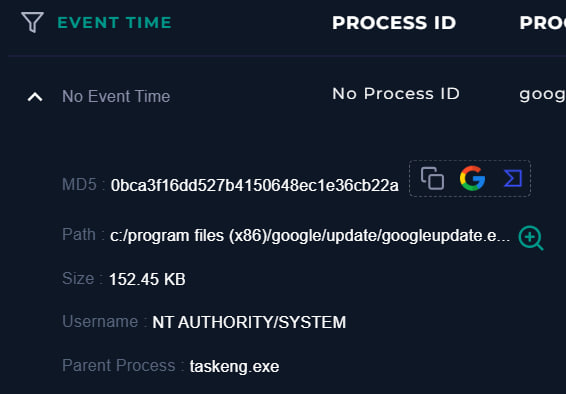
| Attribute | Value |
|---|---|
| File Path | C:\Program Files (x86)\Google\Update\googleupdate.exe |
| Parent Process | taskeng.exe |
| Execution User | NT AUTHORITY\SYSTEM |
| Execution Type | Scheduled Task |
🧠 Analysis
- The file path matches the legitimate Google Update directory
taskeng.exeindicates execution via Windows Task Scheduler- Running as SYSTEM is expected behavior for update services
✅ No anomalies detected in execution chain
🌐 Threat Intelligence Analysis
🔎 VirusTotal
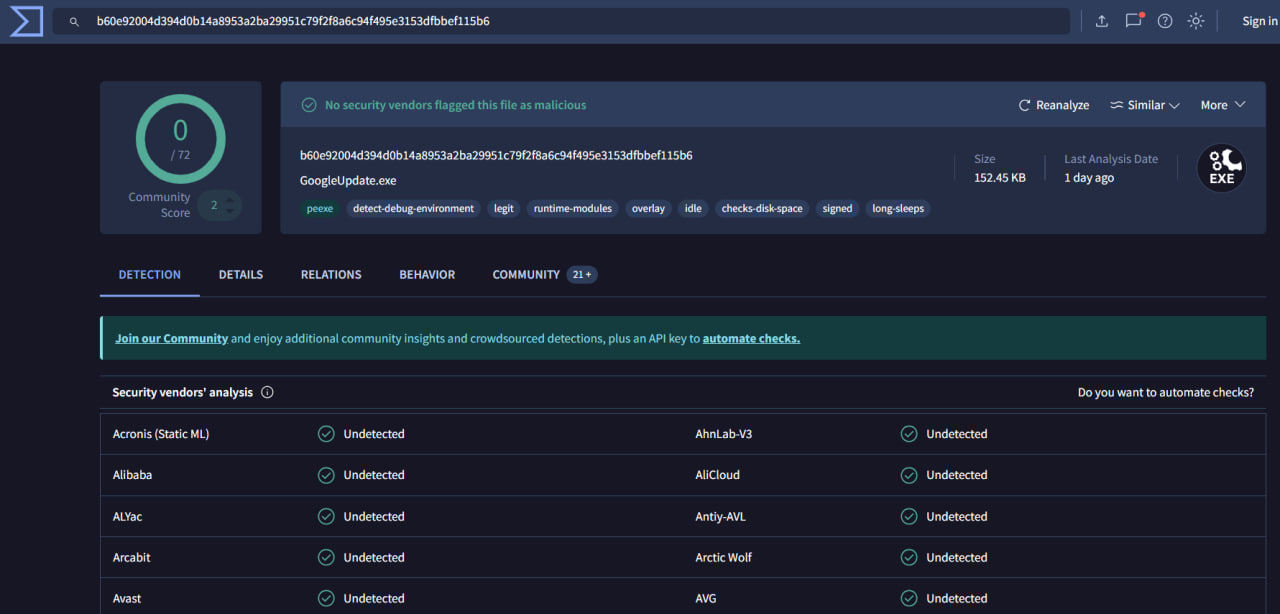
| Result | Value |
|---|---|
| Detection Ratio | 0 / 72 |
| Verdict | Clean |
- No vendors flagged the file as malicious
- Tags indicate legitimate signed executable behavior
🧪 Hybrid Analysis
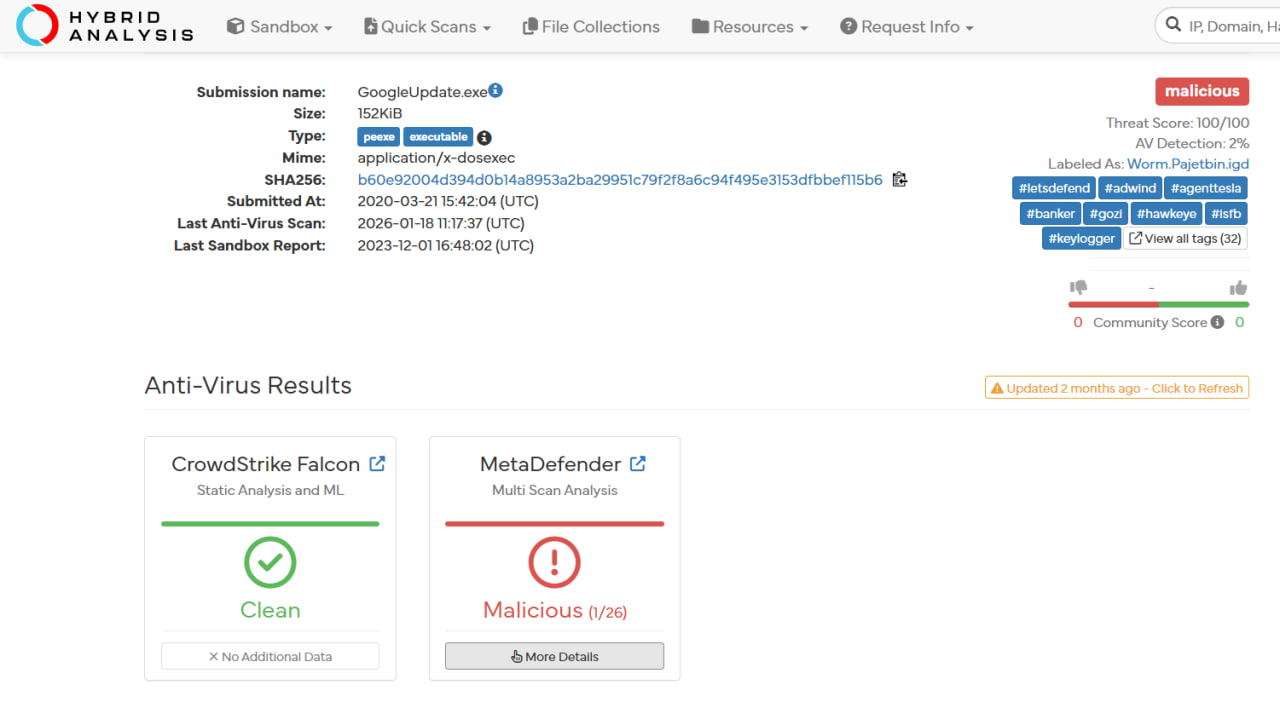
| Result | Value |
|---|---|
| Detection | 1 / 26 |
| Threat Score | 100 / 100 |
| Label | Worm.Pajetbin |
⚠️ Key Observations
- Only 1 engine detected the file
- Tags include:
keyloggerbankerworm
🧠 Interpretation
This is likely a heuristic or machine-learning false positive due to:
- Common filename (
googleupdate.exe) - Behavior resembling auto-update mechanisms
📊 Behavioral Analysis
| Check | Result |
|---|---|
| Suspicious Processes | ❌ None |
| Network Activity | ❌ None |
| Persistence Mechanisms | ❌ None |
| Lateral Movement | ❌ None |
| CLI Activity | ❌ None |
🧾 Investigation Steps
- Reviewed alert details and identified suspicious file
- Analyzed file path and execution chain
- Verified parent process (
taskeng.exe) - Checked endpoint logs for abnormal activity
- Investigated file hash in VirusTotal
- Cross-checked results in Hybrid Analysis
- Correlated all findings with system behavior
⚠️ Why This Alert Triggered
- Filename commonly abused by malware
- Heuristic detection from sandbox environment
- Auto-update behavior mimicking suspicious activity
📌 Final Verdict
| Category | Result |
|---|---|
| File Legitimacy | Legitimate |
| Malware Presence | Not Detected |
| Behavioral Indicators | Clean |
| Alert Classification | False Positive |
| Incident Severity | Informational |
🏁 Conclusion
This alert was triggered due to a commonly abused filename and heuristic detection in sandbox analysis.
However, all evidence including:
- Legitimate file path
- Normal execution via Task Scheduler
- Clean VirusTotal results
- No suspicious endpoint activity
confirms that this file is part of a legitimate Google Update process.
No malicious activity was observed, and the alert has been classified as a false positive.
tags: