SOC104 – Malware Detected (Invoice.exe Maze Ransomware Infection)
by
🧠 Summary
This investigation was triggered by a SOC104 – Malware Detected alert involving a suspicious executable named invoice.exe.
Initial endpoint review showed limited telemetry; however, deeper investigation revealed that the host had accessed a known malicious IP address.
Further threat intelligence analysis confirmed that both the download source (IP) and the file hash were associated with Maze ransomware activity.
The system was immediately contained, and the alert was classified as a True Positive malware infection.
🚨 Alert Overview
- Event ID: 36
- Rule: SOC104 – Malware Detected
- Severity: High
- Source Host: AdamPRD
- Source IP: 10.15.15.18
- User: Adam
- File Name: invoice.exe
- File Hash (MD5):
f83fb9ce6a83da58b20685c1d7e1e546 - File Size: 473.00 KB
- Action: Allowed
🖥️ Endpoint Information
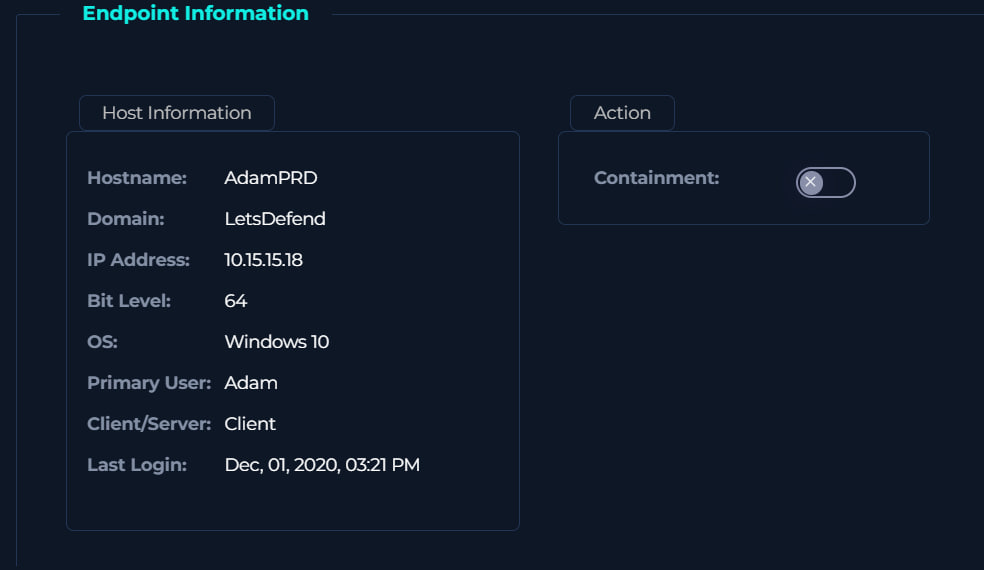
- Hostname: AdamPRD
- Operating System: Windows 10 (64-bit)
- Domain: LetsDefend
- Primary User: Adam
🔍 Initial Findings
- No process telemetry available
- No CLI or browser artifacts found
- No email delivery evidence
⚠️ Despite limited visibility, further investigation continued using network and threat intelligence data.
🌐 Network Analysis
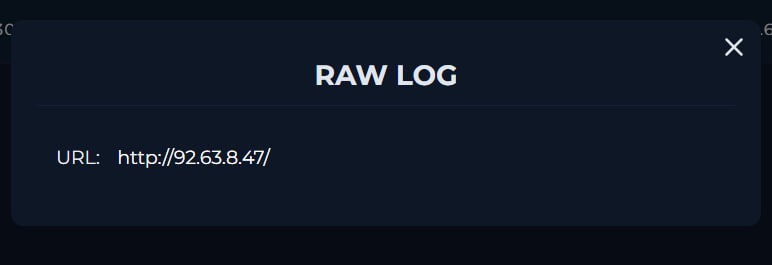
| Attribute | Value |
|---|---|
| Source IP | 10.15.15.18 |
| Destination IP | 92.63.8.47 |
| Protocol | HTTPS (443) |
| URL | http://92.63.8.47/ |
🧠 Analysis
- Endpoint accessed a direct IP-based URL
- Use of IP instead of domain → highly suspicious
- Indicates possible malware hosting or staging server
🌐 Threat Intelligence – IP Analysis
🔎 VirusTotal (IP)
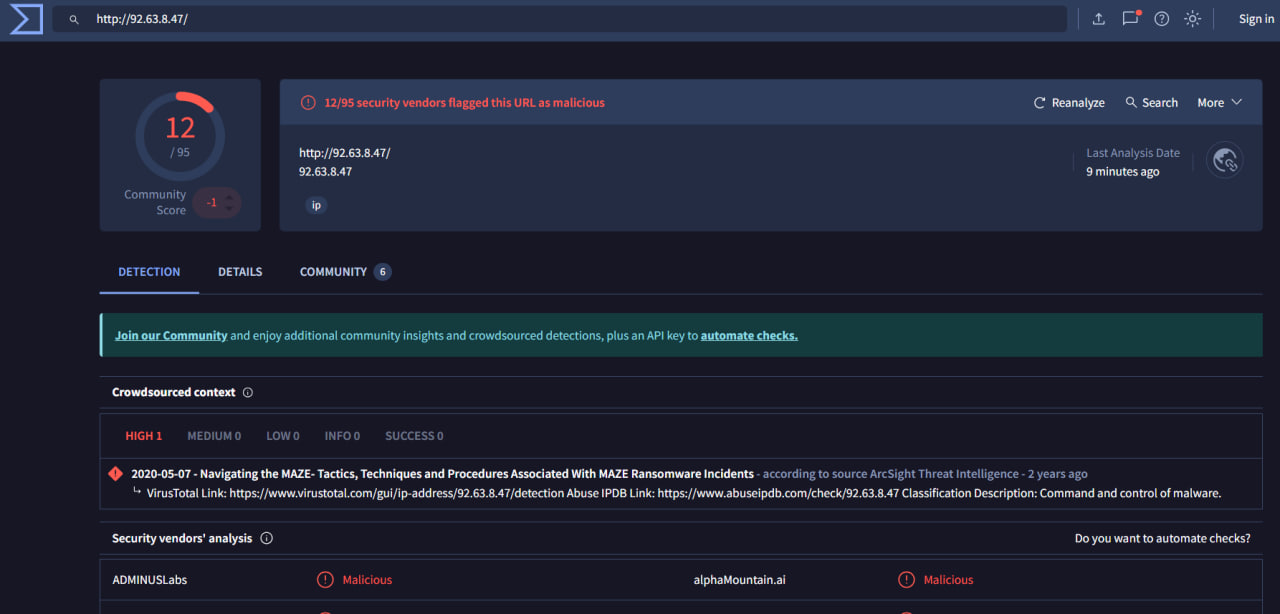
| Result | Value |
|---|---|
| Detection Ratio | 12 / 95 |
| Verdict | Malicious |
📌 Intelligence Insight
- Associated with:
- Command & Control (C2)
- Malware distribution
- Maze ransomware campaigns
🧪 Threat Intelligence – File Analysis
🔎 VirusTotal (File Hash)
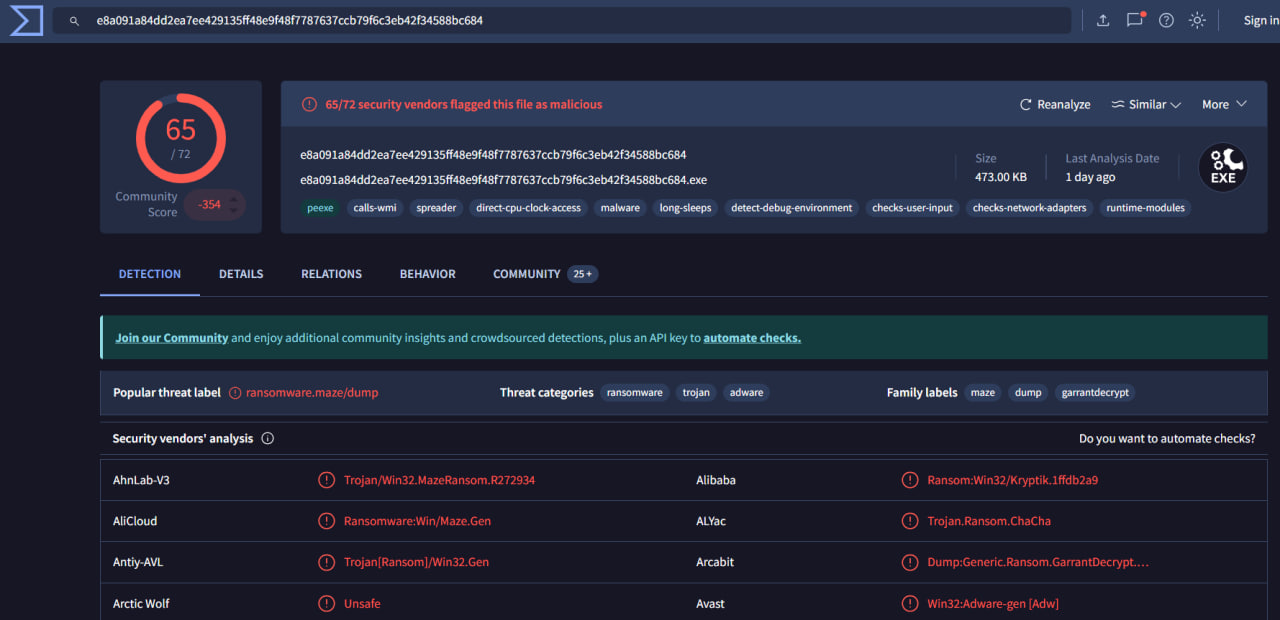
| Result | Value |
|---|---|
| Detection Ratio | 65 / 72 |
| Verdict | Malicious |
🧬 Threat Classification
- Ransomware: Maze
- Trojan Behavior: Present
- Adware Indicators: Minor
🧠 Interpretation
- Extremely high detection ratio → confirmed malware
- Known ransomware family → high impact threat
📊 Behavioral Indicators
| Indicator | Status |
|---|---|
| Malicious File Download | ✅ Confirmed |
| Connection to Malicious IP | ✅ Confirmed |
| Known Malware Hash | ✅ Confirmed |
| Endpoint Visibility | Limited |
| Execution Evidence | Likely |
🧾 Investigation Steps
- Reviewed alert metadata and file details
- Checked endpoint telemetry (process, CLI, browser)
- Identified suspicious network connection to external IP
- Investigated IP reputation using VirusTotal
- Confirmed IP linked to malicious activity
- Analyzed file hash in VirusTotal
- Confirmed file as Maze ransomware
- Correlated network + file indicators
- Contained the affected endpoint
🚨 Incident Response Actions
- ✅ Host isolated / contained
- ✅ Malicious IP identified
- ✅ Malware hash confirmed
- ✅ Threat intelligence correlation completed
- ✅ Logs preserved for forensic analysis
🧬 MITRE ATT&CK Mapping
| Tactic | Technique | Description |
|---|---|---|
| Initial Access | T1189 – Drive-by Compromise | Malicious file downloaded from external IP |
| Execution | T1204.002 – User Execution | User executed invoice.exe |
| Command & Control | T1071.001 – Web Protocols | Communication over HTTP/HTTPS |
| Command & Control | T1105 – Ingress Tool Transfer | Malware downloaded from remote server |
| Discovery | T1082 – System Information Discovery | System info gathered by malware |
| Defense Evasion | T1027 – Obfuscated Files | Possible evasion techniques used |
| Impact | T1486 – Data Encrypted for Impact | Ransomware encryption activity |
📌 Final Verdict
| Category | Result |
|---|---|
| Malware Presence | Confirmed |
| Threat Type | Maze Ransomware |
| Initial Vector | Malicious IP Download |
| Host Compromise | Confirmed |
| Alert Classification | True Positive |
| Incident Severity | Critical |
🏁 Conclusion
This alert represents a confirmed malware infection involving Maze ransomware.
Although endpoint telemetry was limited, correlation of:
- Malicious IP access
- High-confidence VirusTotal detections
- Known ransomware hash
provided sufficient evidence to confirm compromise.
The use of a direct IP-based download further indicates intentional malicious delivery infrastructure.
Immediate containment was required to prevent:
- Data encryption
- Lateral movement
- Ransomware propagation
tags: