SOC165 – SQL Injection Attempt Against Internal Web Server
by
🧠 Summary
This investigation began as a Possible SQL Injection Payload Detected (SOC165) alert.
Initial firewall logs revealed multiple SQL injection payload variations targeting the /search endpoint of an internal web server.
Further HTTP response analysis and device command history investigation confirmed that although the injection attempts reached the backend, no successful exploitation or compromise occurred.
The case was classified as:
True Positive – Unsuccessful SQL Injection Attempt
🚨 Alert Overview
- Event ID: 115
- Rule: SOC165 – Possible SQL Injection Payload Detected
- Severity: High
- Source IP: 167.99.169.17
- Destination IP: 172.16.17.18
- Hostname: WebServer1001
- HTTP Method: GET
- Device Action: Permitted
- User: webadmin
- Last Login: Feb, 10, 2022, 11:12 PM
🌐 Traffic Direction
- Source: External Public IP (DigitalOcean VPS)
- Destination: Internal Web Server (172.16.17.18)
Direction:
Internet → Company Network
This confirms the attack originated from outside the organization.
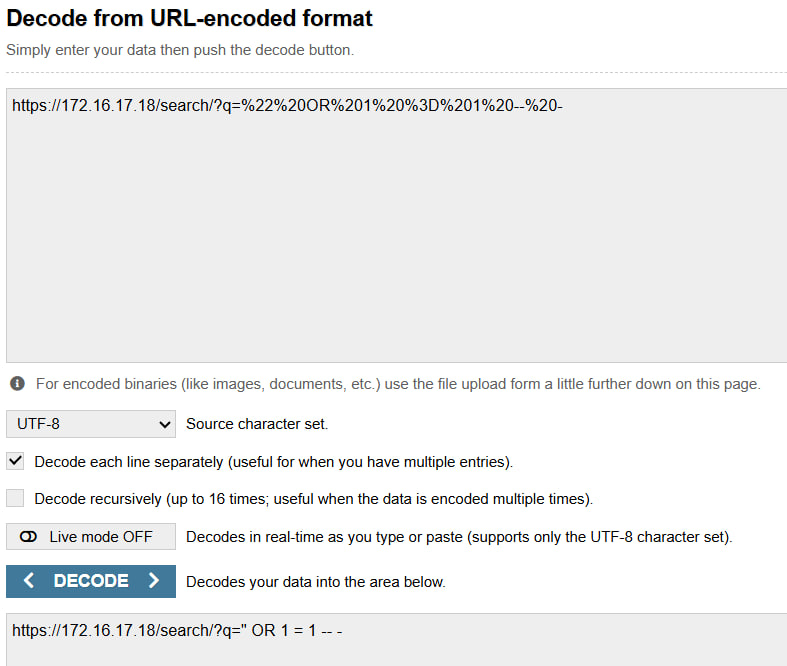
🔎 Step 1 – Payload Decoding & Analysis
🔐 Encoded Request
/search/?q=%22%20OR%201%20%3D%201%20--%20-
🔓 Decoded Payload
/search/?q=" OR 1 = 1 --
This is a classic Boolean-based SQL injection payload.
🔁 Additional Payload Variations Observed
/search/?q='
/search/?q=' OR '1'='1
/search/?q=' OR ''='
/search/?q=' ORDER BY 3--+
These variations indicate structured SQL enumeration behavior:
- Single quote testing
- Boolean condition injection
- Tautology validation
- Column count discovery using ORDER BY
This is consistent with automated SQL injection tools or manual exploitation attempts.
🖼 Example of Decoded URL (Using Online URL Decoder)
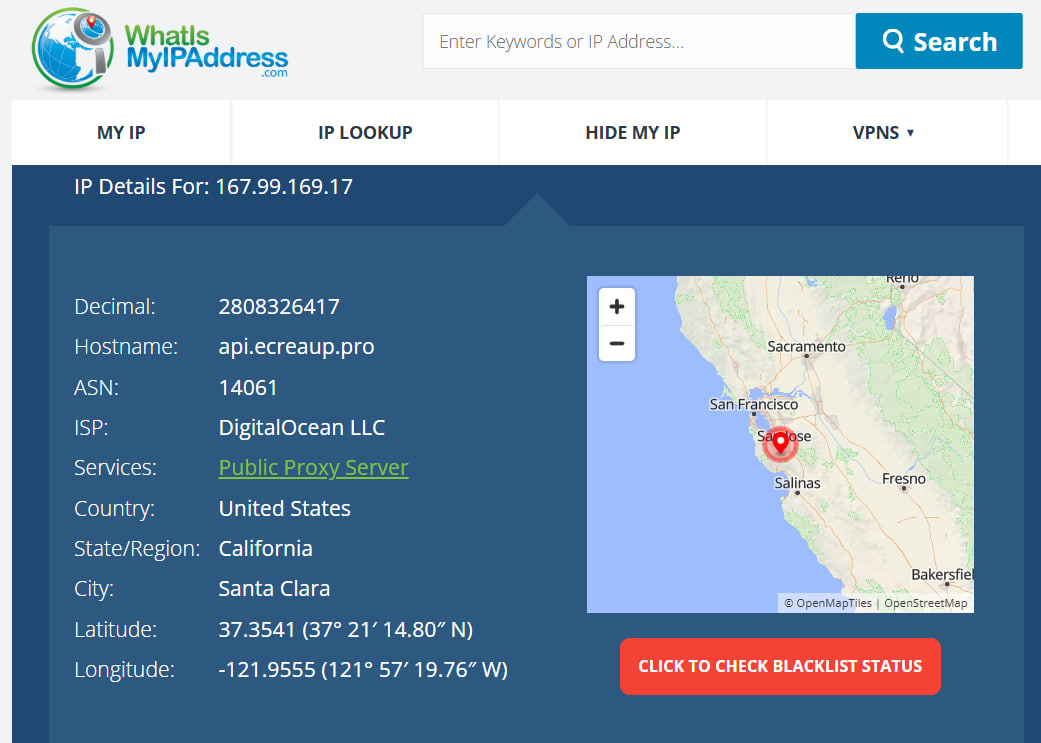
🛰 Step 2 – IP Ownership & Reputation Check
Source IP: 167.99.169.17
- Owner: DigitalOcean (Cloud Hosting Provider)
- Type: VPS Pool Address
- Common Usage: Cloud servers, automation tools, scanning infrastructure
💻 IP Details Check
🖼 VirusTotal Check
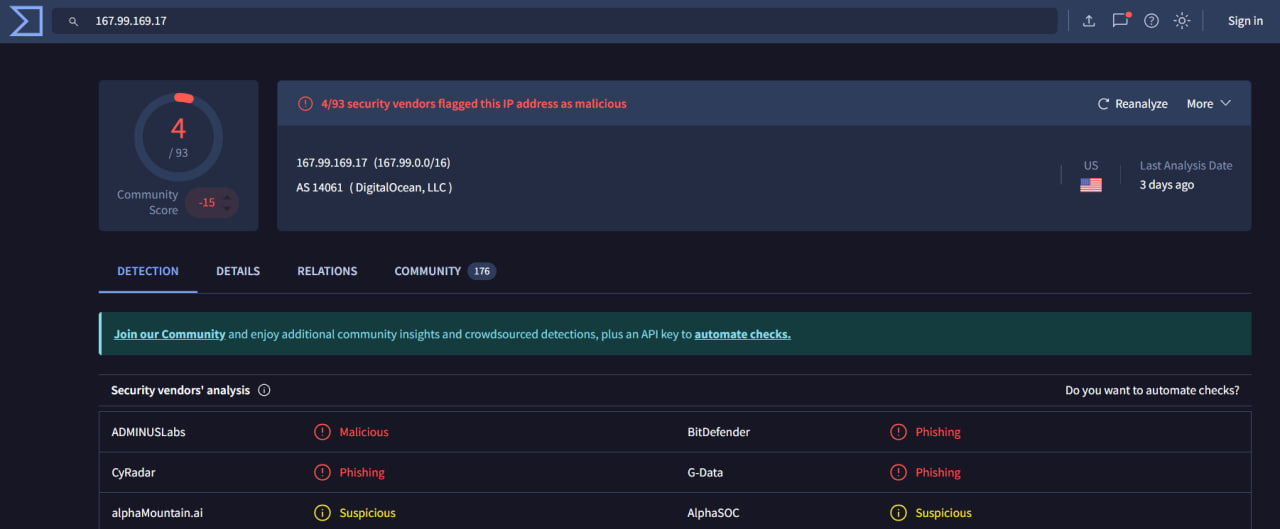
Cloud VPS addresses are commonly abused for reconnaissance and automated attacks.
📊 Step 3 – HTTP Response Analysis
| Request Type | HTTP Status | Response Size (Bytes) |
|---|---|---|
| Injection Attempts | 500 | 948 |
| Normal Homepage | 200 | 3547 |
All malicious payloads resulted in:
HTTP 500 – Internal Server Error
This suggests the backend query failed but did not return data.
No abnormal large responses were observed, which reduces likelihood of data extraction.
🖥 Step 4 – Device Command History Review
Device CLI logs were examined to identify possible command execution or compromise.
Observed commands:
cd web-root
docker-compose -f docker-compose-deploy.yml build
docker-compose -f docker-compose-deploy.yml up
These were legitimate deployment activities unrelated to the attack timeline.
No evidence of:
xp_cmdshell- Reverse shells
- Suspicious downloads
- New user creation
- Lateral movement
🎯 Final Analysis
Attack Type:
SQL Injection (Boolean-based + Column Enumeration)
Was the Attack Successful?
❌ No
Evidence Supporting This Conclusion:
- All injection attempts returned HTTP 500
- No successful 200 injection responses
- No abnormal response size patterns
- No suspicious command execution
- No internal compromise indicators
📂 Artifacts Collected
- Malicious IP: 167.99.169.17
- Target Endpoint:
/search - Decoded Payload:
" OR 1=1 --' OR ''='' ORDER BY 3--+' - Host: WebServer1001 (172.16.17.18)
🚫 Tier 2 Escalation
Not required.
Reason:
- External attack
- No successful compromise
- No internal lateral movement
🏁 Case Outcome
This was a confirmed SQL Injection attempt targeting an internal web server.
Although the payloads reached the application layer, exploitation was unsuccessful.
The case was closed as:
True Positive – No Impact
🔥 Skills Demonstrated
- Web Log Analysis
- SQL Injection Pattern Recognition
- Payload Decoding
- HTTP Response Correlation
- Threat Classification
- Tier 1 SOC Workflow
More blue team investigations coming soon 🚀
tags: