SOC120 – Phishing Mail Detected (Internal to Internal) – False Positive
by
🧠 Summary
This alert involved a phishing detection rule triggered for an internal-to-internal email.
Upon investigation, no malicious indicators were identified. The email contained no attachments, no URLs, and no suspicious content. The SMTP source was an internal mail server.
The alert was classified as a False Positive.
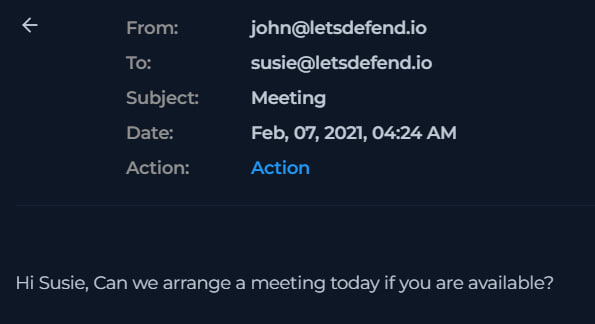
🚨 Alert Details
- Event ID: 52
- Rule: SOC120 – Phishing Mail Detected – Internal to Internal
- Severity Level: Security Analyst
- SMTP Address: 172.16.20.3
- Source: john@letsdefend.io
- Destination: susie@letsdefend.io
- Subject: Meeting
- Device Action: Allowed
- Event Time: Feb 07, 2021 – 04:24 AM
🔍 Phase 1 – Initial Email Parsing
The following details were reviewed during triage:
- Sender and recipient are internal users
- SMTP address
172.16.20.3is within private IP range (internal mail server) - Email subject is generic (“Meeting”)
- Sent at 04:24 AM (unusual but not malicious on its own)
📄 Email Content Review
Email Body:
Hi Susie, Can we arrange a meeting today if you are available?
Evidence:
Findings:
- No hyperlinks
- No attachments
- No credential harvesting attempt
- No urgent or coercive language
- No social engineering indicators
The content appears to be normal internal communication.
🌐 SMTP & Infrastructure Validation
The SMTP address:
172.16.20.3
- Falls within private internal IP range (172.16.0.0/12)
- Indicates email originated from internal mail infrastructure
- No signs of spoofing
🧪 Artifact Analysis
No artifacts were identified.
- No malicious domains
- No suspicious IP addresses
- No file hashes
- No attachments
- No embedded URLs
⚖️ Investigation Conclusion
| Category | Result |
|---|---|
| Attachment | None |
| Alert | False Positive |
| Execution | Not applicable |
| C2 Traffic | Not applicable |
| Compromise | No impact |
The email was determined to be legitimate internal communication.
🧠 Key SOC Lessons
- Not every phishing alert represents malicious activity.
- Internal-to-internal emails require verification but not assumption.
- Unusual timing alone does not equal compromise.
- Proper triage prevents unnecessary escalation.
- Rule-based detections can generate false positives.
🎯 Final Verdict
✔️ False Positive
✔️ No malicious indicators
✔️ No compromise detected
✔️ Alert closed after validation
tags: