SOC114 – Malicious Attachment Detected (Phishing Alert)
by
🧠 Summary
This alert involved a high-severity phishing email detected by Exchange with a malicious attachment.
During the investigation, the attachment was confirmed as malicious via hash analysis and sandbox behavior. However, internal log analysis showed no evidence of execution or C2 communication, meaning no compromise occurred.
The alert was classified as a True Positive (No Impact).
🚨 Alert Details
- Alert Name: SOC114 – Malicious Attachment Detected
- Severity: High
- Source: Exchange
- Event ID: 45
- Email Count: 1
🔍 Phase 1 – Email Parsing (Initial Triage)
Before deep analysis, the following information was reviewed:
- Sender address: accounting@cmail.carleton.ca
- Recipient: richard@letsdefend.io
- SMTP sending server: 49.234.43.39
- Subject line: Invoice
- Attachment presence: Excel file
- Email content characteristics: Appears to be as an invoice file
Key Objective: Determine whether this was a phishing attempt and whether the attachment was malicious.
🧪 Phase 2 – Attachment Analysis (Static & Sandbox)
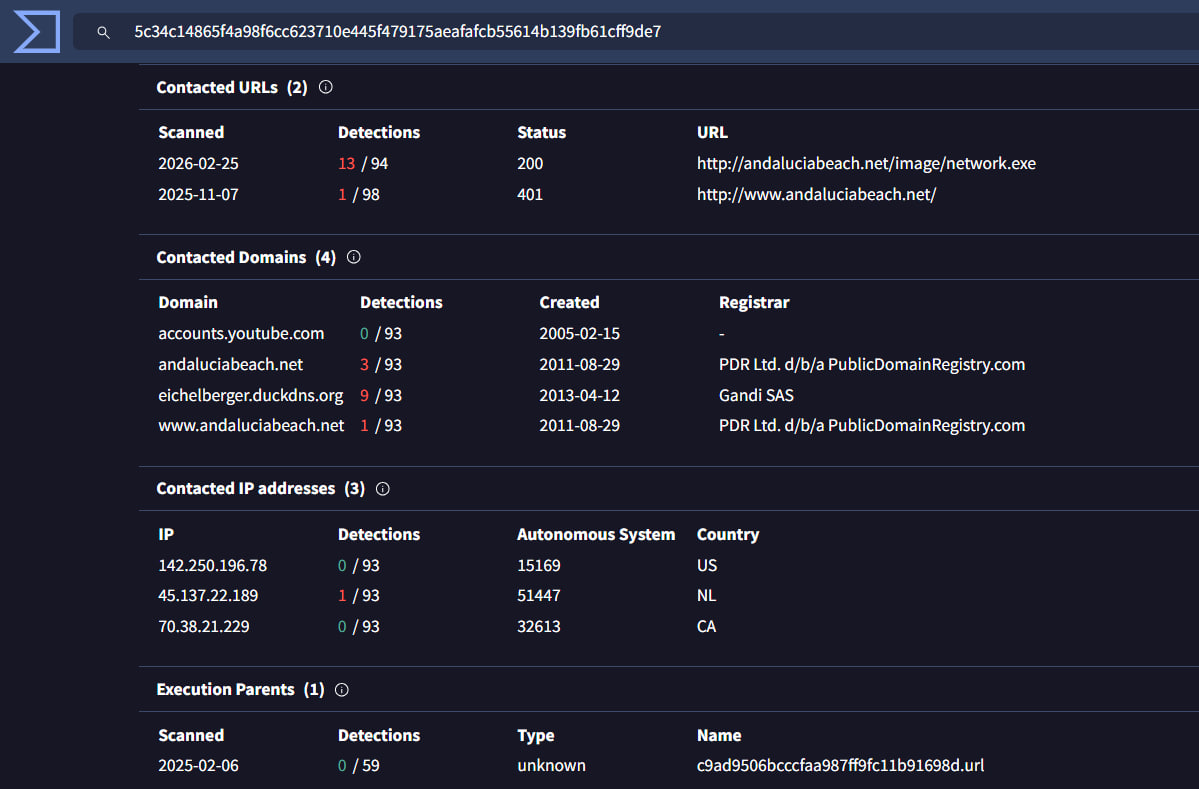
The attachment hash was analyzed in VirusTotal.
SHA256:
5c34c14865f4a98f6cc623710e445f479175aeafafcb55614b139fb61cff9de7
🔎 Sandbox Findings
The file attempted to:
- Download:
http://andaluciabeach.net/image/network.exe - Communicate with:
eichelberger.duckdns.org
These behaviors strongly indicate:
- Malware downloader activity
- Possible Command & Control (C2) communication
VirusTotal Result:
🌐 Phase 3 – C2 Identification
From sandbox behavior:
Suspicious Domains:
andaluciabeach.neteichelberger.duckdns.org
The domain eichelberger.duckdns.org is especially suspicious because:
- It uses DuckDNS (commonly abused free dynamic DNS provider)
- It showed multiple AV detections
- It matches typical C2 infrastructure patterns
📊 Phase 4 – Internal Log Validation
To determine impact, Log Management was checked for:
- Connections to
eichelberger.duckdns.org - Connections to resolved IP:
37.0.14.215- Resolved this IP from MXToolbox using found domain. - DNS queries to malicious domains
- Outbound traffic to sandbox-identified indicators
🔍 Result:
No internal logs showed:
- C2 communication
- DNS resolution
- Outbound connections
- File execution artifacts
⚖️ Investigation Conclusion
| Category | Result |
|---|---|
| Attachment | Malicious |
| Alert | True Positive |
| Execution | Not observed |
| C2 Communication | Not observed |
| Compromise | No impact detected |
The email contained a malicious attachment, but there was no evidence that any user executed the file.
🧾 Artifacts Documented
-
File Hash (SHA256):
5c34c14865f4a98f6cc623710e445f479175aeafafcb55614b139fb61cff9de7 -
Malicious Domain:
eichelberger.duckdns.org - 37.0.14.215 -
Malware Hosting Domain:
andaluciabeach.net - 70.38.21.234
These indicators were documented for monitoring and future detection.
🧠 Key SOC Lessons
- Malware delivery ≠ Malware execution
- Sandbox behavior must always be validated with internal logs
- Dynamic DNS domains are common C2 infrastructure
- Always document IOCs even if no compromise occurred
- True Positive does not always mean impact
🎯 Final Verdict
✔️ True Positive
✔️ Malicious attachment confirmed
✔️ No execution observed
✔️ No compromise detected
Alert successfully investigated and closed.
tags: